Month: February 2024
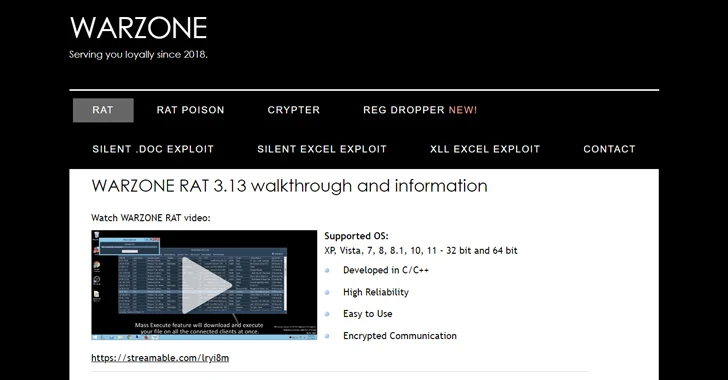
Feb 11, 2024NewsroomMalware / Cybercrime The U.S. Justice Department (DoJ) on Friday announced the seizure of online infrastructure that was used to sell a remote access trojan (RAT) called Warzone RAT. The domains – www.warzone[.]ws and three others – were “used to sell computer malware used by cybercriminals to secretly access and steal data from…
Read MoreVideo, Ransomware Called a “watershed year for ransomware”, 2023 marked a reversal from the decline in ransomware payments observed in the previous year 09 Feb 2024 Ransomware payments in 2023 reached a record-breaking $1.1 billion in 2023, according to an analysis by Chainalysis, a blockchain research firm. Calling 2023 a “watershed year for ransomware”, Chainalysis…
Read MoreFeb 10, 2024NewsroommacOS Malware / Cyber Threat Apple macOS users are the target of a new Rust-based backdoor that has been operating under the radar since November 2023. The backdoor, codenamed RustDoor by Bitdefender, has been found to impersonate an update for Microsoft Visual Studio and target both Intel and Arm architectures. The exact initial…
Read MoreFriday Squid Blogging: A Penguin Named “Squid” Amusing story about a penguin named “Squid.” As usual, you can also use this squid post to talk about the security stories in the news that I haven’t covered. Read my blog posting guidelines here. Tags: squid Posted on February 9, 2024 at 5:09 PM • 0 Comments…
Read MoreCisco has fixed three serious cross-site request forgery (CSRF) vulnerabilities in its Expressway Series collaboration gateway and a denial-of-service (DoS) flaw in the ClamAV anti-malware engine. CSRF flaws allow unauthenticated attackers to perform arbitrary actions on vulnerable devices by tricking users to click on a specifically crafted link. The actions execute with the privilege of…
Read MoreToday’s fast-paced digital landscape has ushered in a significant transformation in the way we perceive and utilize mobile devices. Gone are the days when phones merely facilitated voice communication; today, they have evolved into indispensable tools, deeply ingrained in our daily lives. This shift, however, has brought about new challenges, particularly in the realm of…
Read MoreCISA has added one new vulnerability to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the Known Exploited Vulnerabilities Catalog…
Read MoreFortinet released security updates to address critical remote code execution vulnerabilities in FortiOS (CVE-2024-21762, CVE-2024-23313) as well as an access control vulnerability in FortiClientEMS (CVE-2024-45581). A cyber threat actor could exploit these vulnerabilities to take control of an affected system. Note: According to Fortinet, CVE-2024-21762 is potentially being exploited in the wild. CISA encourages users…
Read MoreNo, Toothbrushes Were Not Used in a Massive DDoS Attack The widely reported story last week that 1.5 million smart toothbrushes were hacked and used in a DDoS attack is false. Near as I can tell, a German reporter talking to someone at Fortinet got it wrong, and then everyone else ran with it without…
Read MoreBusiness Security Heavy workloads and the specter of personal liability for incidents take a toll on security leaders, so much so that many of them look for the exits. What does this mean for corporate cyber-defenses? 08 Feb 2024 • , 5 min. read Cybersecurity is finally becoming a board-level issue. That’s as it should…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA