Month: February 2024
How SVR-Attributed Actors are Adapting to the Move of Government and Corporations to Cloud Infrastructure OVERVIEW This advisory details recent tactics, techniques, and procedures (TTPs) of the group commonly known as APT29, also known as Midnight Blizzard, the Dukes, or Cozy Bear. The UK National Cyber Security Centre (NCSC) and international partners assess that APT29…
Read MoreFeb 26, 2024The Hacker NewsSoftware Security / Cryptocurrency A set of fake npm packages discovered on the Node.js repository has been found to share ties with North Korean state-sponsored actors, new findings from Phylum show. The packages are named execution-time-async, data-time-utils, login-time-utils, mongodb-connection-utils, and mongodb-execution-utils. One of the packages in question, execution-time-async, masquerades as its…
Read MoreCISA, NCSC-UK, and Partners Release Advisory on Russian SVR Actors Targeting Cloud Infrastructure | CISA
by nlqip
CISA, in partnership with UK National Cyber Security Centre (NCSC) and other U.S. and international partners released the joint advisory, SVR Cyber Actors Adapt Tactics for Initial Cloud Access. This advisory provides recent tactics, techniques, and procedures (TTPs) used by Russian Foreign Intelligence Service (SVR) cyber actors—also known as APT29, the Dukes, CozyBear, and NOBELIUM/Midnight…
Read MoreApple Announces Post-Quantum Encryption Algorithms for iMessage Apple announced PQ3, its post-quantum encryption standard based on the Kyber secure key-encapsulation protocol, one of the post-quantum algorithms selected by NIST in 2022. There’s a lot of detail in the Apple blog post, and more in Douglas Stabila’s security analysis. I am of two minds about this.…
Read More“I didn’t pay much attention to it, because for 5 years of swimming in money I became very lazy,” LockBitSupp said. “At 20:47 I found that the site gives a new error 404 Not Found nginx, tried to enter the server through SSH and could not, the password did not fit, as it turned out…
Read MoreLast year, the Open Worldwide Application Security Project (OWASP) published multiple versions of the “OWASP Top 10 For Large Language Models,” reaching a 1.0 document in August and a 1.1 document in October. These documents not only demonstrate the rapidly evolving nature of Large Language Models, but the evolving ways in which they can be…
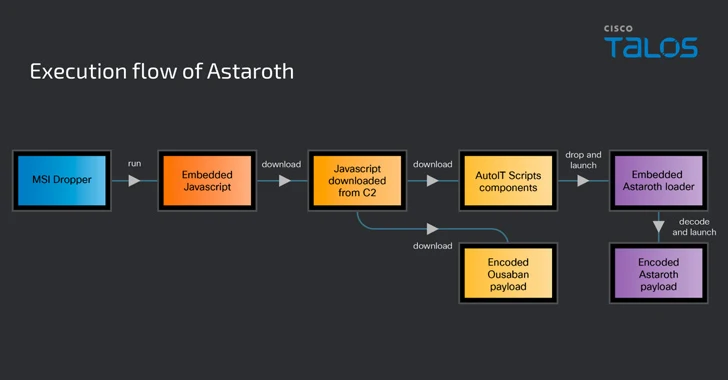
Read MoreCybersecurity researchers are warning about a spike in email phishing campaigns that are weaponizing the Google Cloud Run service to deliver various banking trojans such as Astaroth (aka Guildma), Mekotio, and Ousaban (aka Javali) to targets across Latin America (LATAM) and Europe. “The infection chains associated with these malware families feature the use of malicious…
Read MoreCommunication skills are some of the most fundamental learned in life. Whether in written, verbal, non-verbal, or visual form, the ability to communicate clearly and effectively is quickly becoming a top prerequisite for cybersecurity jobs. In fact, it’s become so highly valued that Hays’ first global cybersecurity report, released in 2023, identified communication as one…
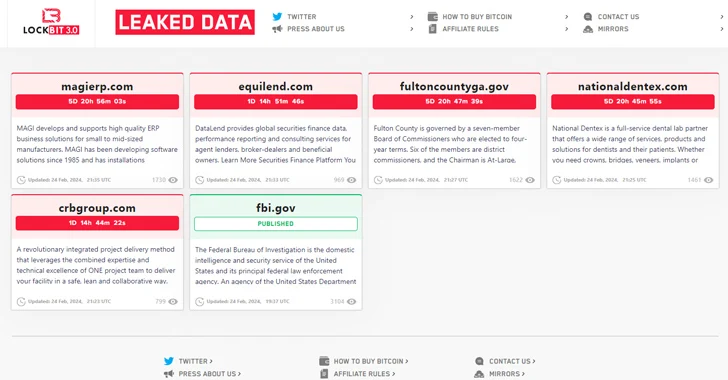
Read MoreThe threat actors behind the LockBit ransomware operation have resurfaced on the dark web using new infrastructure, days after an international law enforcement exercise seized control of its servers. To that end, the notorious group has moved its data leak portal to a new .onion address on the TOR network, listing 12 new victims as…
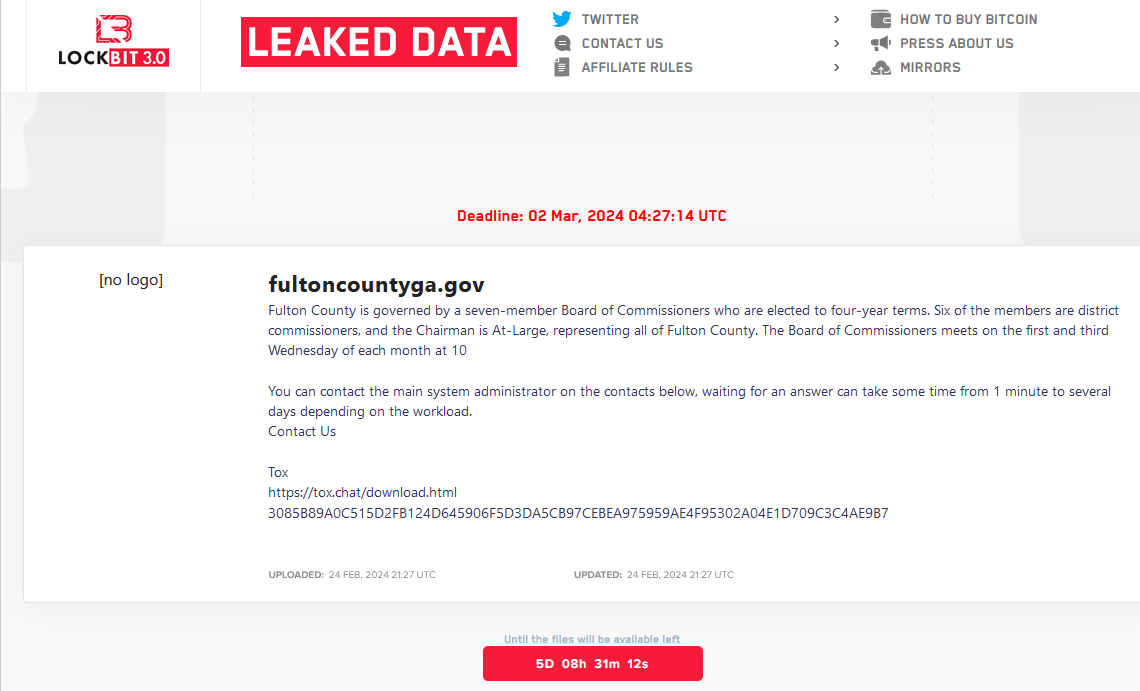
Read MoreFBI’s Lockbit Takedown Postponed a Ticking Time Bomb in Fulton County, Ga. – Krebs on Security
by nlqip
The FBI’s takedown of the LockBit ransomware group last week came as LockBit was preparing to release sensitive data stolen from government computer systems in Fulton County, Ga. But LockBit is now regrouping, and the gang says it will publish the stolen Fulton County data on March 2 unless paid a ransom. LockBit claims the…
Read More