What is Ransomware? Things You Need to Know About Ransomware | BlackFog
by nlqip
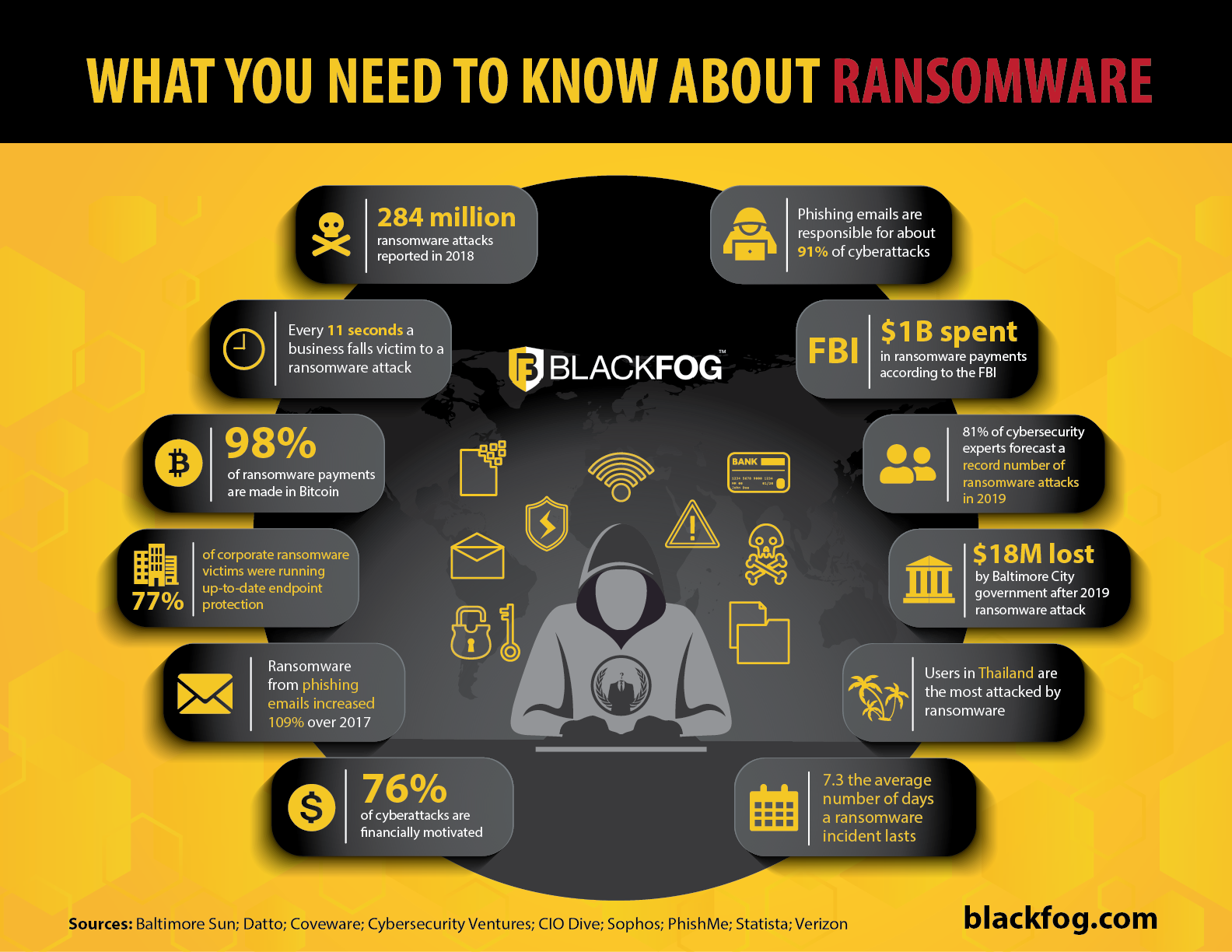
Ransomware is one of the biggest cybersecurity threats facing businesses in the current environment. While this form of cyberattack has been around for a while, it has exploded in popularity among criminals in recent years.
In 2023, it was reported by Verizon that almost a quarter of data breaches (24 percent) involved ransomware, while our own research found a 68 percent increase in the number of attacks compared with the previous year.
What’s more, in 2018, just over half of businesses worldwide (55.1 percent) reported being affected by ransomware. However, by 2023, this had grown to nearly three out of four (72.2 percent).
It’s therefore clear that ransomware attacks are a problem every enterprise needs to be aware of. In this blog we’ll address some of the most common questions about ransomware and outline some of the best ways to look past the myths and protect your organization from facing the ‘to pay or not to pay’ dilemma.
Ransomware is a type of malicious software that gains access to and encrypts files or systems and is designed to coerce businesses into paying money. It typically works by encrypting either mission-critical information or essential files that are necessary for a device to function. Encrypted files or machines make it impossible for a company to operate normally unless the business pays the criminals for the decryption key, leading to extensive downtime until systems can be restored.
What are the Different Types of Ransomware?
There are several types of ransomware attack businesses need to be aware of. Traditional types of ransomware infection include Crypto ransomware, which encrypts valuable files on a computer so that the user cannot access them, and Locker ransomware, which locks users out of their device completely until a ransom is paid. In either of these cases, the goal is to make it impossible for the victim to do business unless they pay for the key.
However, the number one ransomware threat today comes from double extortion attacks. These work by exfiltrating data in addition to encrypting it. Cybercriminals – typically working as part of highly-organized gangs – then demand a payment in order to prevent public release of sensitive business or personal data.
A double extortion ransomware threat can be especially dangerous as businesses cannot simply refuse to pay and turn to backups in order to recover data and restore operations. In these circumstances, where their most precious assets have already been stolen, they may decide they have no choice but to pay up in order to avoid further reputational and business damage if private information is exposed.
How Does Ransomware Work?
In a traditional ransomware attack, once the malware has been installed on a computer, it executes on the local machine and then contacts a third-party server to download other payloads (applications) to activate the malware. It subsequently starts encrypting all the files on your drive. After it has completed, it will display a paywall requesting money (usually in the form of non-traceable bitcoin) to have files decrypted. If firms don’t pay the ransom, an encrypted file can be deleted by the hackers.
Increasingly, however, there is a second stage of the attack. This sees the ransomware exfiltrate data back to its command and control center for use in future extortion attempts. It can do this via a number of endpoints, including desktop and laptop PCs, servers or mobile devices, which means companies will need to place strong emphasis on protecting the perimeter of their network not only from malicious software coming in, but also sensitive data being taken out.

How Does Ransomware Spread?
Ransomware is often spread through phishing emails that contain malicious links or attachments. It can also be spread by the “drive-by download” technique which occurs when a user unknowingly visits an infected website and malware is downloaded and installed without their knowledge.
What are the Latest Ransomware Trends?

The vast majority of ransomware attacks now seek to exfiltrate data in order to initiate double or triple ransomware threats. According to our research, more than nine out of ten incidents (91 percent) involved this in 2023, with more traditional efforts to encrypt data losing focus.
With many businesses calculating the reputation damage of public exposure of data to be so high, this is also allowing ransomware attackers to increase their demands. At the end of 2023, for instance, our research revealed the average payment totalled $850,000, which marked a 15 percent increase in just six months.
What Sectors are Cybercriminals Targeting?
Recent well-publicized attacks suggest that cybercriminals have set their sights on the public sector, local government and healthcare organizations with less than adequate cybersecurity protection in place and strong insurance policies. Smaller companies that operate within the supply chain of larger corporations are also highly vulnerable due to the access and data they can provide.
Our research shows healthcare (up by 138 percent year-on-year in 2023), education (up 70 percent) and government (up 57 percent) were the three most-targeted sectors last year. Small to medium-sized organizations were the prime targets, with the average victim employing 6,918 people. However, other firms that hold valuable data such as financial services and critical infrastructure and utilities companies are also among the enterprises most of interest to hackers.
Such organizations are particularly tempting targets to cybercriminals as they often possess highly sensitive data belonging to members of the public – such as personal images – that would be highly damaging were it to be publicly exposed. At the same time, organizations that run essential public services can ill-afford any downtime, so may feel more compelled to pay in order to minimize disruption.
Will Antimalware Solutions Protect You From Ransomware?

Antimalware and antivirus software aren’t enough to protect you from today’s modern threat landscape. One of the main reasons for this is that they focus on known attack vectors, using techniques such as signature matching in order to detect incoming threats.
Hackers are well aware of this and are always looking for the next successful ransomware variant to evade defenses. In 2024, cybercriminals are increasingly using tactics such as Fileless malware download ransom payloads and signatures to avoid detection. Fileless attacks are on the rise with 77 percent of successful attacks using Fileless exploits. In fact, as many as 75 percent of companies that fell victim to ransomware were running up-to-date endpoint protection on the infected machines.
Taking advantage of tools such as PowerShell is one common way in which Fileless attacks can be launched. Indeed, in 2023, BlackFog’s research found that over one in three ransomware incidents (35 percent) used PowerShell as their attack vector.
Antimalware tools may also find it difficult to protect against attacks where human error is involved, such as when employees fall victim to a phishing email that tricks them into handing over access credentials for key networks or databases. While email security tools should be able to stop such attacks from reaching people’s inboxes, they can never be 100 percent effective, and will do nothing to stop other social engineering attacks such as voice phishing.
Therefore, ensuring all employees have security awareness training to look out for telltale signs of these attacks is just as important as having the right technical solutions in place when it comes to stopping cybercriminals from stealing sensitive information.
What is the Impact of Ransomware?
The consequences of a ransomware incident can be severe and wide-ranging. Some of the most common issues businesses encounter include:
- Temporary or permanent loss of sensitive or proprietary information
- Disruption to regular operations
- Financial losses incurred to restore systems and files
- Reputational damage
What are Some Top Tips to Protect Firms From Ransomware?
As with any malware attack, defending against ransomware requires a multilayered approach. Firms cannot rely on traditional tools like firewalls and antivirus software alone to keep them safe, while human factors must also be considered. Among the top points to keep in mind are the following:
- Always back up your data
- Update your software regularly
- Educate the weakest link in your organization – your employees – to ensure they don’t fall victim to a phishing scam
- Take a layered approach to security to prevent cyberattacks
- Prevent data exfiltration by blocking outbound data flow
- Deploy an on-device solution to prevent unauthorized data from ever leaving your endpoints
How are Ransoms Typically Paid?
Thanks to the perceived anonymity offered by cryptocurrencies, ransomware operators most commonly demand that ransom payments are made in bitcoin. However, less common alternative payment options such as iTunes and Amazon gift cards have also been recorded.
To Pay or Not to Pay, What is the Correct Approach?
There is much debate around the ‘to pay or not to pay’ dilemma when dealing with ransomware. The official recommendation from law enforcement in the US and UK is never to pay the ransom. However, guidance from Forrester Research suggests that paying a ransom should be seen as a valid recovery path that should be explored and evaluated just like any other business decision.
A ransomware victim must consider its ability to recover from the cyberattack, the costs of outside consultants and ransomware recovery plans, as well as cybersecurity insurance. In some cases, this will cover the ransom, but this is becoming less common as cyber insurance providers seek to disincentivize ransomware payments. It is important to note that even if you pay there is no guarantee you will get your data back.
One of the main arguments against paying a ransom is that it will encourage future attacks on the business. In fact, research by Cybereason found that 80 percent of companies that paid a ransom were targeted for a second time, with 40 percent paying again. Of these, 70 percent paid a higher amount the second time round.
What is the Cost of Ransomware?

In 2022, BlackFog’s research found the average ransom demand by hackers to release files or have stolen data deleted was $258,143. However, by the end of 2023, this had risen to $850,700.
It’s important to remember that the direct cost of a ransom payment itself only accounts for a small portion of the overall financial losses a company can expect to see as a result of an attack. In fact, one report estimates that these costs only make up 15 percent of a firm’s ransomware expenses.
Indirect costs can include immediate lost business during downtime, longer-term reputational damage, the potential for regulatory fines and class-action lawsuit settlements and expenses relating to investigation, remediation and future hardening of IT networks.
When added up, the average total cost of a data breach in 2023 amounted to $4.45 million, according to IBM. Even if firms do have adequate cyber insurance policies in place to assist them with their recovery, these expenses can be crippling to small and medium-sized enterprises in particular, so it is no wonder so many firms file for bankruptcy following a data breach.
What is the Best Way to Prevent Ransomware?
The best way to protect against ransomware is to stop the attack from happening in the first place. These days hackers are attacking from all angles, profiling your employees’ behavior as they browse online and through applications on your company devices, collecting data from across your networks.
However, no antimalware solution is 100 percent foolproof. Being a victim of a cyberattack is a question of when, not if. Therefore, organizations must have specialized ransomware tools that are able to prevent attackers from removing data from the business in the event that their first lines of defense fail to prevent an intrusion.
In this case, a dedicated anti data exfiltration (ADX) solution will be hugely valuable. Through a layered approach to security such as that provided by BlackFog, the technology uses machine learning to build a picture of activity on a network and then spot, in real-time, unusual behavior. Once telltale indicators that an attacker is trying to remove unauthorized data from your device or network have been detected, these tools can step in automatically and stop them in their tracks.
It’s also important for these tools to work across all devices. Mobile ransomware and data exfiltration via personally-owned devices can be especially hard to stop using traditional centralized tools. Therefore, lightweight on-device solutions that can operate across every endpoint and do not break the security chain by sending data back to servers for analysis are essential for providing enterprise ransomware protection in a more flexible environment.
Learn more about how BlackFog protects enterprises from the threats posed by ransomware.
Source link
ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde
Recent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA

