Over 1,400 CrushFTP servers vulnerable to actively exploited bug
by nlqip
Over 1,400 CrushFTP servers exposed online were found vulnerable to attacks currently targeting a critical severity server-side template injection (SSTI) vulnerability previously exploited as a zero-day.
While CrushFTP describes CVE-2024-4040 as a VFS sandbox escape in its managed file transfer software that enables arbitrary file reading, unauthenticated attackers can use it to gain remote code execution (RCE) on unpatched systems.
The company warned customers on Friday to “update immediately” to block attacker attempts to escape the user’s virtual file system (VFS) and download system files.
On Tuesday, Rapid7’s vulnerability research team confirmed the security flaw’s severity, saying it was “fully unauthenticated and trivially exploitable.”
“Successful exploitation allows for not only arbitrary file read as root, but also authentication bypass for administrator account access and full remote code execution,” Rapid7 explained.
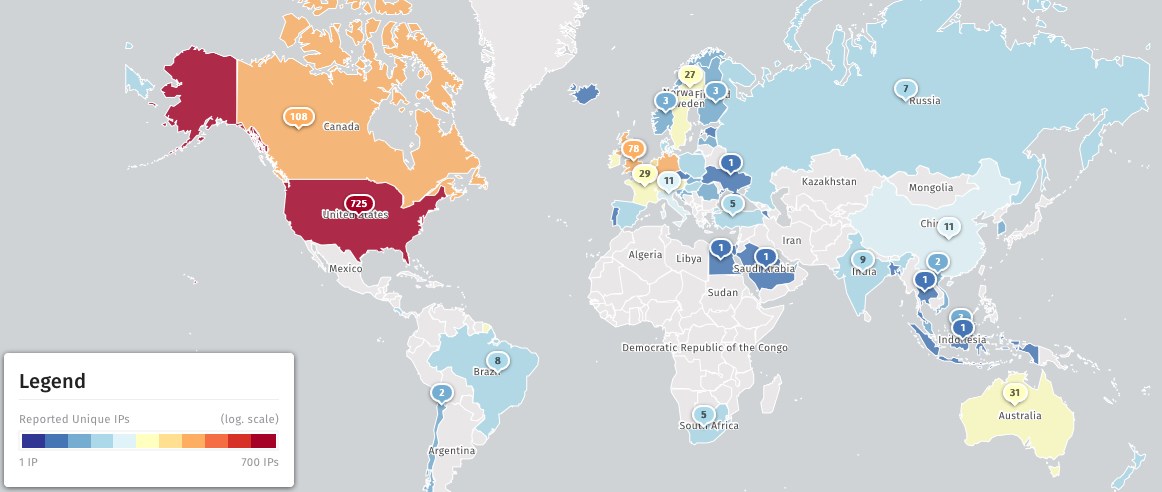
Security researchers from the Shadowserver threat monitoring platform have discovered 1,401 CrushFTP unpatched instances left exposed online, most of them in the United States (725), Germany (115), and Canada (108).
Shodan also currently tracks 5,232 Internet-exposed CrushFTP servers, although it doesn’t provide any information on how many of them might be vulnerable to attacks.
Actively exploited in targeted attacks
Cybersecurity company CrowdStrike released an intelligence report on Friday after CrushFTP disclosed the actively exploited zero-day and released patches, revealing that attackers were targeting CrushFTP servers at multiple U.S. organizations in what looked like a politically motivated intelligence-gathering campaign.
According to evidence found by Falcon OverWatch and Falcon Intelligence teams at CrowdStrike, CrushFTP zero-day was being exploited in targeted attacks.
CrushFTP users are advised to regularly check the vendor’s website for the latest instructions and prioritize patching to protect themselves against ongoing exploitation attempts.
CISA also added CVE-2024-4040 to its Known Exploited Vulnerabilities catalog on Wednesday, ordering that U.S. federal agencies should secure their vulnerable servers within a week, by May 1st.
In November, CrushFTP customers were also warned to patch a critical RCE vulnerability (CVE-2023-43177) after Converge security researchers who discovered and reported the flaw published a proof-of-concept exploit.
Source link
lol
Over 1,400 CrushFTP servers exposed online were found vulnerable to attacks currently targeting a critical severity server-side template injection (SSTI) vulnerability previously exploited as a zero-day. While CrushFTP describes CVE-2024-4040 as a VFS sandbox escape in its managed file transfer software that enables arbitrary file reading, unauthenticated attackers can use it to gain remote code execution…
Recent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA
