Month: April 2024
The first time I heard about distributed brute-force login attacks was from master web application firewall (WAF) administrator Marc LeBeau. At the time he was defending a hotel chain against attackers who were brute-force guessing customer passwords and withdrawing hotel points. According to LeBeau, there’s a popular attack vector among brute-force attackers right now that…
Read MoreCommunication is Key – Leveraging Business Frameworks to Develop a Detection and Response Strategy | Binary Defense
by nlqip
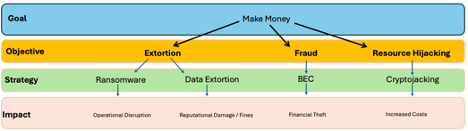
Operating a business within the modern threat landscape can often appear like an impossible task. With a constant stream of new vulnerabilities, malware, and adversaries flowing, security leadership can often become overwhelmed and stuck in “analysis paralysis” struggling to identify what threats to invest resources towards. It’s no secret that cybercrime has become big business…
Read MorePrivacy today isn’t just about staying away from prying eyes. The very act of communicating across the Internet with open, non-confidential protocols invites exposure to multiple threat types. Source link lol
Read MoreI would like to present as Exhibit A, this snippet culled from a 2018 survey on security:1 “Almost half of the business management team (48 percent) believes that app performance and speed are more important than security, whereas 56 percent of IT management ranked performance and security as equally important. 65 percent of companies…
Read MoreAllow me to nitpick for a moment: There’s a difference between data and information. Data are the facts or details from which information is derived. As such, standalone pieces of data are rarely useful. It’s not really information until data points are connected with context to tell a story. This nuance is more relevant than…
Read MoreRussia Attacks Global Network Infrastructure Through Vulnerabilities That Extend Far Beyond Their Targets
by nlqip
It’s a sad state of Internet affairs when the US government must publish a US-CERT Alert about Russia targeting US entities through negligent network infrastructure misconfigurations.1 In Alert TA18-106A, US-CERT discloses that since 2015, the US government, in partnership with the UK, has been receiving data from numerous sources that “large numbers” of enterprise-class and…
Read MorePart 4 of CRN’s 2024 Big Data 100 includes a look at the vendors solution providers should know in the big data management and integration tools space. Managerial Perogative By 2025 the total amount of digital data generated, gathered, copied and consumed globally is expected to be in the range of 175 to 180 zettabytes.…
Read MoreThe rise of poorly secured Internet of Things (IoT) devices has made it possible for attackers to gain access to targets of interest. Nation-states, spies, mercenaries, and others don’t need to dress up as repairmen to plant bugs in rooms anymore; they can just hack into a room that has vulnerable IoT devices. In May,…
Read MoreThreat intelligence is mainstreaming into a de-facto everyday tool of cyber-defense. But all that intelligence must be collected, analyzed, and prepared by someone. Enter threat researchers, the advanced scouts of cybersecurity. They are becoming more numerous and conspicuous as more intelligence on illicit hacker activity is demanded. Threat researchers trawl through the dark web, pick…
Read MoreFigure 16: QA Injection alert, “Page Injected!” Conclusion Panda’s expansion beyond traditional banking targets is following the trend we noticed during the 2017 holiday season.5 This is the first campaign we have seen targeting cryptocurrency sites, but it’s a move that makes sense, given the popularity of cryptocurrency. This act of simultaneous campaigns targeting several…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm