Botnet sent millions of emails with LockBit Black ransomware payloads
by nlqip

Since April, a new large-scale LockBit Black ransomware campaign has sent millions of phishing emails via the Phorpiex botnet.
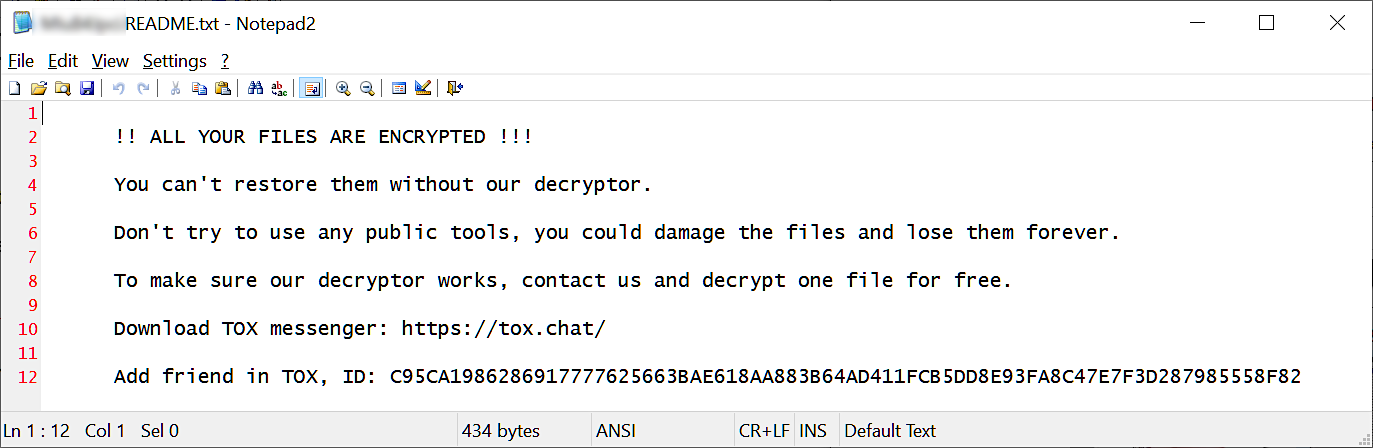
As New Jersey’s Cybersecurity and Communications Integration Cell (NJCCIC) warned on Friday, the attackers use ZIP attachments containing an executable that deploys the LockBit Black payload, which encrypts the recipients’ systems if launched.
The LockBit Black encryptor deployed in these attacks is likely built using the LockBit 3.0 builder leaked by a disgruntled developer on Twitter in September 2022. However, this campaign is not believed to have any affiliation with the actual LockBit ransomware operation.
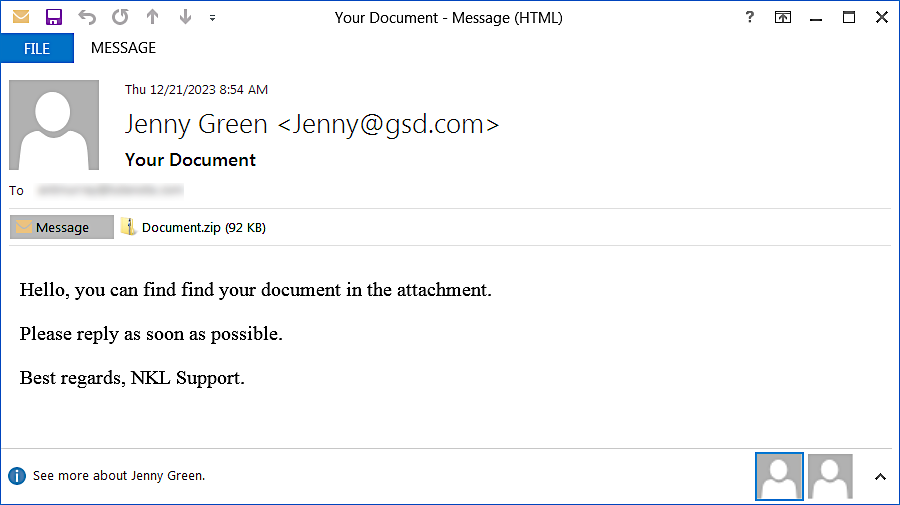
These phishing emails with “your document” and “photo of you???” subject lines are being sent using “Jenny Brown” or “Jenny Green” aliases from over 1,500 unique IP addresses worldwide, including Kazakhstan, Uzbekistan, Iran, Russia, and China.
The attack chain begins when the recipient opens the malicious ZIP archive attachment and executes the binary inside.
This executable then downloads a LockBit Black ransomware sample from the infrastructure of the Phorphiex botnet and executes it on the victim’s system. After launching it, it will attempt to steal sensitive data, terminate services, and encrypt files.
Cybersecurity company Proofpoint, which has been investigating these spray-and-pray attacks since April 24, said on Monday that the threat actors target companies in various industry verticals worldwide.
Although this approach is not new, the massive number of emails sent to deliver the malicious payloads and ransomware being used as a first-stage payload make it stand out even though it lacks the sophistication of other cyberattacks.
“Beginning April 24, 2024 and continuing daily for about a week, Proofpoint observed high-volume campaigns with millions of messages facilitated by the Phorpiex botnet and delivering LockBit Black ransomware,” Proofpoint security researchers said.
“This is the first time Proofpoint researchers have observed samples of LockBit Black ransomware (aka LockBit 3.0) being delivered via Phorphiex in such high volumes.”
The Phorpiex botnet (also known as Trik) has been active for over a decade. It evolved from a worm that spread via removable USB storage and Skype or Windows Live Messenger chats into an IRC-controlled trojan that used email spam delivery.
While it slowly grew to a massive size, controlling over 1 million infected devices after years of activity and development, the botnet’s operators tried selling the malware’s source code on a hacking forum after shutting down the Phorpiex infrastructure.
The Phorpiex botnet has also been used to deliver millions of sextortion emails (spamming over 30,000 emails per hour) and, more recently, used a clipboard hijacker module to replace cryptocurrency wallet addresses copied to the Windows clipboard with attacker-controlled ones.
Within a year after adding crypto-clipping support, Phorpiex’s operators hijacked 969 transactions and stole 3.64 Bitcoin ($172,300), 55.87 Ether ($216,000), and $55,000 worth of ERC20 tokens.
To defend against phishing attacks that push ransomware, NJCCIC recommends implementing ransomware risk mitigation strategies and using endpoint security solutions and email filtering solutions (like spam filters) to block potentially malicious messages.
Source link
lol
Since April, a new large-scale LockBit Black ransomware campaign has sent millions of phishing emails via the Phorpiex botnet. As New Jersey’s Cybersecurity and Communications Integration Cell (NJCCIC) warned on Friday, the attackers use ZIP attachments containing an executable that deploys the LockBit Black payload, which encrypts the recipients’ systems if launched. The LockBit Black encryptor…
Recent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA
