Windows Quick Assist abused in Black Basta ransomware attacks
by nlqip

Financially motivated cybercriminals abuse the Windows Quick Assist feature in social engineering attacks to deploy Black Basta ransomware payloads on victims’ networks.
Microsoft has been investigating this campaign since at least mid-April 2024, and, as they observed, the threat group (tracked as Storm-1811) started their attacks by email bombing the target after subscribing their addresses to various email subscription services.
Once their mailboxes flood with unsolicited messages, the threat actors call them while impersonating a Microsoft technical support or the attacked company’s IT or help desk staff to help remediate the spam issues.
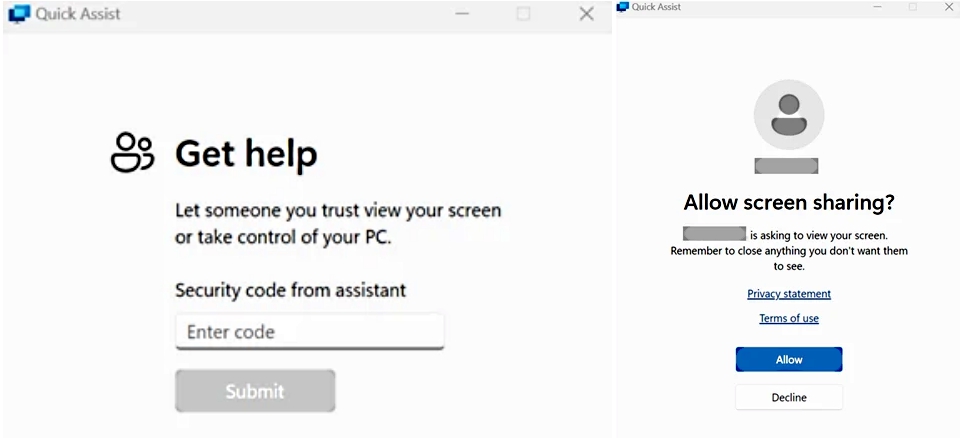
During this voice phishing attack, the attackers trick the victims into granting them access to their Windows devices by launching the Quick Assist built-in remote control and screen-sharing tool.
“Once the user allows access and control, the threat actor runs a scripted cURL command to download a series of batch files or ZIP files used to deliver malicious payloads,” Microsoft said.
“In several cases, Microsoft Threat Intelligence identified such activity leading to the download of Qakbot, RMM tools like ScreenConnect and NetSupport Manager, and Cobalt Strike.”
After installing their malicious tools and concluding the phone call, Storm-1811 performs domain enumeration, moves laterally through the victim’s network, and deploys Black Basta ransomware using the Windows PsExec telnet-replacement tool.
Cybersecurity company Rapid7, which also spotted the attacks, says the malicious actors will use “a batch script to harvest the victim’s credentials from the command line using PowerShell.”
“The credentials are gathered under the false context of the ‘update’requiring the user to log in. In most of the observed batch script variations, the credentials are immediately exfiltrated to the threat actor’s server via a Secure Copy command (SCP),” Rapid7 added.
“In at least one other observed script variant, credentials are saved to an archive and must be manually retrieved.”
To block these social engineering attacks, Microsoft advises network defenders to block or uninstall Quick Assist and similar remote monitoring and management tools if they’re not used and to train employees to recognize tech support scams.
Those targeted in these attacks should only allow others to connect to their device if they contacted their IT support personnel or Microsoft Support and immediately disconnect any Quick Assist sessions if they suspect malicious intent.
The Black Basta ransomware operation
After the Conti cybercrime group shut down two years ago following a series of embarrassing data breaches, it broke up into multiple factions, one of which is believed to be Black Basta.
Black Basta surfaced as a Ransomware-as-a-Service (RaaS) operation in April 2022. Since then, its affiliates have breached many high-profile victims, including German defense contractor Rheinmetall, U.K. technology outsourcing company Capita, Hyundai’s European division, the Toronto Public Library, the American Dental Association, industrial automation company and government contractor ABB, Sobeys, Knauf, and Yellow Pages Canada.
More recently, Black Basta was linked to a ransomware attack that hit U.S. healthcare giant Ascension, forcing it to divert ambulances to unaffected facilities.
As CISA and the FBI revealed in a joint advisory last week, Black Basta ransomware affiliates have breached more than 500 organizations between April 2022 and May 2024, encrypting and stealing data from at least 12 out of 16 critical infrastructure sectors.
Health-ISAC (Information Sharing and Analysis Center) also warned in a threat bulletin that the ransomware gang “has recently accelerated attacks against the healthcare sector.”
According to cybersecurity company Elliptic and cyber insurance firm Corvus Insurance research, Black Basta has collected at least $100 million in ransom payments from over 90 victims until November 2023.
Source link
lol
Financially motivated cybercriminals abuse the Windows Quick Assist feature in social engineering attacks to deploy Black Basta ransomware payloads on victims’ networks. Microsoft has been investigating this campaign since at least mid-April 2024, and, as they observed, the threat group (tracked as Storm-1811) started their attacks by email bombing the target after subscribing their addresses…
Recent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA
