Snowblind malware abuses Android security feature to bypass security
by nlqip

A novel Android attack vector from a piece of malware tracked as Snowblind is abusing a security feature to bypass existing anti-tampering protections in apps that handle sensitive user data.
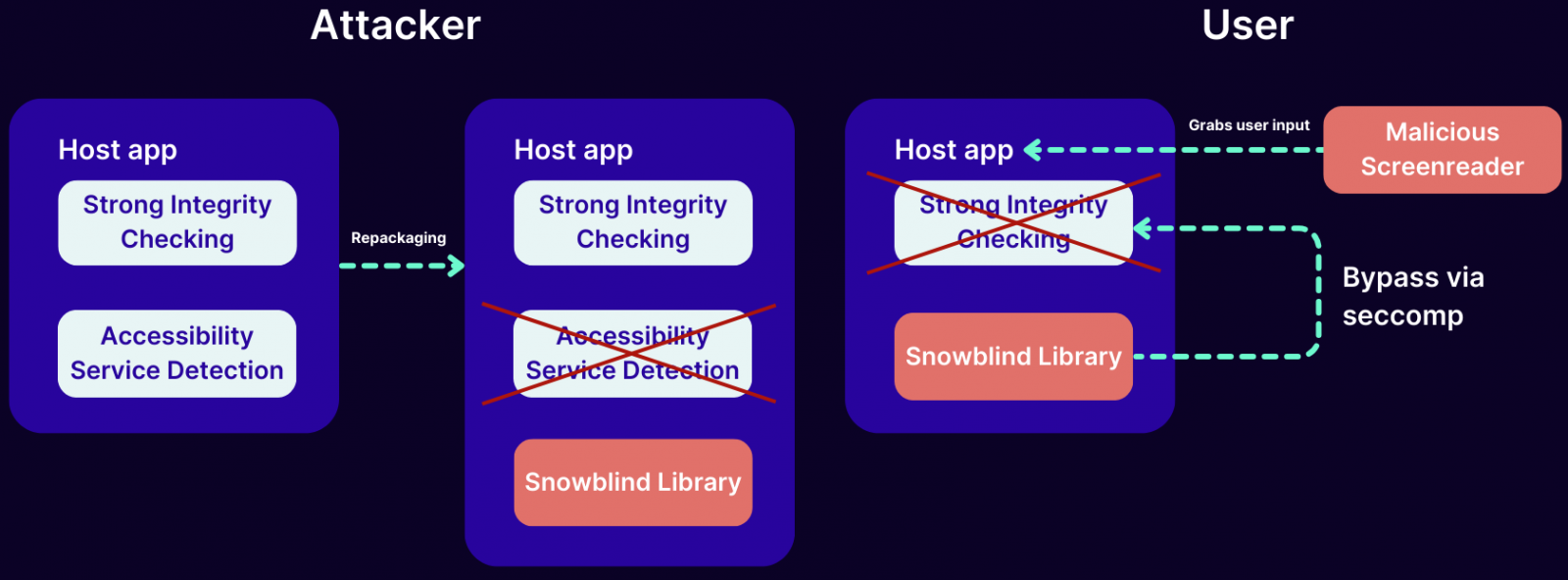
Snowblind’s goal is to repackage a target app to make them unable to detect abuse of accessibility services that allow it to obtain user input such as credentials, or to get remote control access to run malicious actions.
Unlike other Android malware, though, Snowblind abuses ‘seccomp’, short for secure computing, a Linux kernel feature that Android uses for integrity checks on applications, to protect users against malicious actions such as application repackaging.
Abusing seccomp security feature
Mobile app security company Promon was able to analyze how Snowblind achieves its goal undetected after receiving a sample from i-Sprint, a partner providing access and identity system protections to businesses.
“This malware attacked the app of one of i-Sprint’s Southeast Asian customers. Our analysis of Snowblind found that it uses a novel technique to attack Android apps based on the Linux kernel feature seccomp” – Promon
Seccomp is a Linux kernel security feature designed to reduce the attack surface of applications by restricting the system calls (syscalls) they can make. It acts as a filter for the syscalls an app is allowed to run, blocking those that have been abused in attacks.
Google first integrated seccomp in Android 8 (Oreo), implementing it in the Zygote process, which is the parent process of all Android apps.
Snowblind targets apps that handle sensitive data by injecting a native library which loads before the anti-tampering code, and installs a seccomp filter to intercepts system calls such as the ‘open() syscall,’ commonly used in file access.
When the APK of the target app is checked for tampering, Snowblind’s seccomp filter does not allow the call to proceed and instead triggers a SIGSYS signal indicating that the process sent a bad argument to the system call.
Snowblind also installs a signal handler for SIGSYS to inspect it and manipulate the thread’s registers, the researchers explain in a report shared with BleepingComputer.
This way, the malware can modify the ‘open()’ system call arguments to point the anti-tampering code to an unmodified version of the APK.
Due to the targeted nature of the seccomp filter, the performance impact and operational footprint are minimal, so the user is unlikely to notice anything during normal app operations.
Source: Promon
Attack scenarios
Promon says that the technique observed in Snowblind attacks “does not seem to be well-known” and the researchers believe that most apps do not protect against it.
In a video demonstrating how the attack works, the researchers show that a Snowblind attack is completely invisible to the user and can result in leaking login credentials.
The researchers told BleepingComputer that Snowblind can be used to disable various security features in apps, such as two-factor authentication, or biometric verification.
An attacker could use the technique “to read sensitive information displayed on the screen, navigate the device or control apps, bypass security measures by automating interactions that would typically require user intervention, as well as exfiltrate sensitive personally identifiable information and transaction data.”
Promon says that Snowblind was observed targeting one app of an i-Sprint customer in Southeast Asia. However, it is unclear how many apps have been targeted so far. Furthermore, the method could be adopted by other adversaries to bypass protections in Android.
BleepingComputer has contacted Google with a request for a comment on the active abuse of seccomp to bypass Android protections, and a spokesperson responded with the following statement:
Based on our current detection, no apps containing this malware are found on Google Play.
Android users are automatically protected against known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services.
The company spokesperson added that “Google Play Protect can warn users or block apps known to exhibit malicious behavior, even when those apps come from sources outside of Play.”
Source link
lol
A novel Android attack vector from a piece of malware tracked as Snowblind is abusing a security feature to bypass existing anti-tampering protections in apps that handle sensitive user data. Snowblind’s goal is to repackage a target app to make them unable to detect abuse of accessibility services that allow it to obtain user input…
Recent Posts
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
