Month: June 2024
Jun 14, 2024NewsroomPrivacy / Ad Tracking Google’s plans to deprecate third-party tracking cookies in its Chrome web browser with Privacy Sandbox has run into fresh trouble after Austrian privacy non-profit noyb (none of your business) said the feature can still be used to track users. “While the so-called ‘Privacy Sandbox’ is advertised as an improvement…
Read MoreJun 15, 2024NewsroomArtificial Intelligence / Privacy Meta on Friday said it’s delaying its efforts to train the company’s large language models (LLMs) using public content shared by adult users on Facebook and Instagram in the European Union following a request from the Irish Data Protection Commission (DPC). The company expressed disappointment at having to put…
Read MoreESET Research The I-SOON data leak confirms that this contractor is involved in cyberespionage for China, while Iran-aligned groups step up aggressive tactics following the Hamas-led attack on Israel in 2023 14 Jun 2024 • , 2 min. read In this episode of the ESET Research Podcast, we dissect the most interesting findings of the…
Read MoreHow Arid Viper spies on Android users in the Middle East – Week in security with Tony Anscombe
by nlqip
Video The spyware, called AridSpy by ESET, is distributed through websites that pose as various messaging apps, a job search app, and a Palestinian Civil Registry app 14 Jun 2024 This week, ESET researchers released their findings about five campaigns that used trojanized apps to target Android users in Egypt and Palestine. Initiated in 2022,…
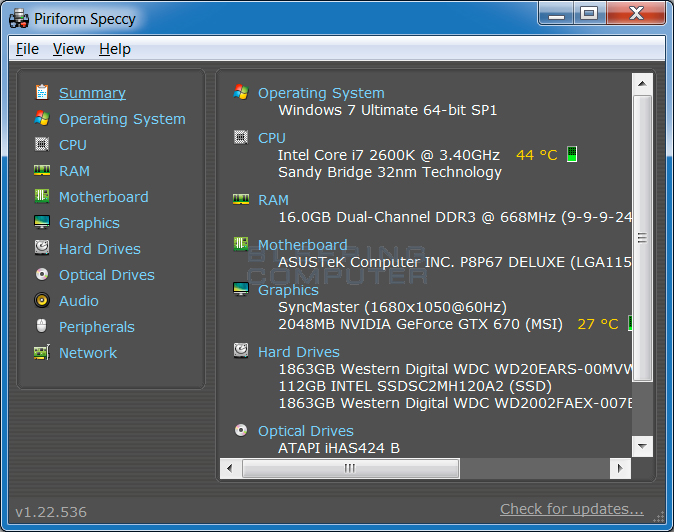
Read MoreScreenshots for Speccy BleepingComputer Review: Speccy is a tool that provides detailed information about the hardware components and operating system of the computer it is run on. This information is extremely valuable when you want to upgrade existing hardware, find out what specific hardware is installed on your computer, and whether or not the current…
Read MoreThe last 12 months have witnessed a rapid-fire round of innovation and adoption of new technologies. Powerful new identities, environments and attack methods are shaping the quickly changing cybersecurity threat landscape, rendering it more complex and causing the diffusion of risk reduction focus. New CyberArk research indicates the rise of machine identities and the increasing…
Read MoreIn the modern digital landscape, cybersecurity isn’t just a technical challenge – it’s a business imperative. At the heart of cybersecurity is identity security – the principle that the right people have the right access at the right time. As we venture further into the digital world, protecting the business from modern threats is crucial, which inherently…
Read MoreSimply put, APIs (short for application programming interface) are how machines, cloud workloads, automation and other non-human entities communicate with one another. They also represent an access point to highly sensitive company data and services. Almost every organization uses these machine interfaces, and their usage is only growing because they are essential to digital transformation and automation…
Read MoreImage: Keytronic PCBA manufacturing giant Keytronic is warning it suffered a data breach after the Black Basta ransomware gang leaked 530GB of the company’s stolen data two weeks ago. Key Tronic, better known as Keytronic, is an American technology company that initially started as an Original Equipment Manufacturer (OEM) of keyboards and mice but is now one of…
Read MoreFriday Squid Blogging: Squid Cartoon Squid humor. As usual, you can also use this squid post to talk about the security stories in the news that I haven’t covered. Read my blog posting guidelines here. Tags: squid Posted on June 14, 2024 at 5:06 PM • 0 Comments Sidebar photo of Bruce Schneier by Joe…
Read More