Month: June 2024
Jun 10, 2024NewsroomCloud Security / Vulnerability Microsoft is warning about the potential abuse of Azure Service Tags by malicious actors to forge requests from a trusted service and get around firewall rules, thereby allowing them to gain unauthorized access to cloud resources. “This case does highlight an inherent risk in using service tags as a…
Read MoreStaying Sharp: Cybersecurity CPEs Explained Perhaps even more so than in other professional domains, cybersecurity professionals constantly face new threats. To ensure you stay on top of your game, many certification programs require earning Continuing Professional Education (CPE) credits. CPEs are essentially units of measurement used to quantify the time and effort professionals spend on…
Read MoreHTTPS vs HTTP: Know the difference between secure and non-secure web protocols At a glance, HTTP and HTTPs may seem similar but they are different. HTTP transmits data in plain text, whereas HTTPS utilizes TLS/SSL encryption to secure communication. Let’s crack the code on HTTP vs HTTPS in this article. You will discover the stark…
Read MoreExploiting Mistyped URLs Interesting research: “Hyperlink Hijacking: Exploiting Erroneous URL Links to Phantom Domains“: Abstract: Web users often follow hyperlinks hastily, expecting them to be correctly programmed. However, it is possible those links contain typos or other mistakes. By discovering active but erroneous hyperlinks, a malicious actor can spoof a website or service, impersonating the…
Read MoreWhat is Operational Technology? Operational Technology (OT) is the backbone of our modern world as we know it today. Think about the daily operations of a factory, the precise control of our power grids, and even the supply of clean water to our homes. All of these modern capabilities are made possible and efficient due…
Read MoreMorocco as an emerging cybercrime originator Although cybercrime operations are a global phenomenon, most financially motivated cybercriminals operate from a well-understood list of countries, including China, Russia, Ukraine, the US, Romania, and Nigeria. But at this year’s Sleuthcon, a new nation emerged that threatens to break into the ranks of top cybercrime havens: Morocco. Microsoft…
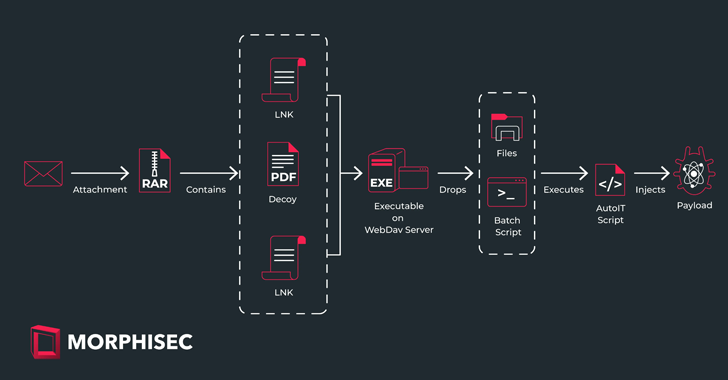
Read MoreJun 10, 2024NewsroomCyber Espionage / Malware Cybersecurity researchers have disclosed details of a threat actor known as Sticky Werewolf that has been linked to cyber attacks targeting entities in Russia and Belarus. The phishing attacks were aimed at a pharmaceutical company, a Russian research institute dealing with microbiology and vaccine development, and the aviation sector,…
Read MoreAnd in another similarity to conventional attack types, “nation-states are probably one of the biggest risks here because they have the ability and resources to invest in this [type of attack],” says David Youssef a managing director at FTI Consulting and leader of the North America incident response efforts for the firm’s cybersecurity practice. Bad…
Read MoreBrave browser experienced its most significant growth month ever in May 2024, now used by more than 78.95 million monthly users, up 7.3%. The privacy-focused web browser experienced substantial growth in Latin America, where the browser became one of the top apps in the Google Play Store in several countries. Using the historical method, the Brave’s monthly…
Read MoreA group of Israeli researchers explored the security of the Visual Studio Code marketplace and managed to “infect” over 100 organizations by trojanizing a copy of the popular ‘Dracula Official theme to include risky code. Visual Studio Code (VSCode) is a source code editor published by Microsoft and used by many professional software developers worldwide.…
Read MoreRecent Posts
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict