Hackers abused API to verify millions of Authy MFA phone numbers
by nlqip
Twilio has confirmed that an unsecured API endpoint allowed threat actors to verify the phone numbers of millions of Authy multi-factor authentication users, potentially making them vulnerable to SMS phishing and SIM swapping attacks.
Authy is a mobile app that generates multi-factor authentication codes at websites where you have MFA enabled.
In late June, a threat actor named ShinyHunters leaked a CSV text file containing what they claim are 33 million phone numbers registered with the Authy service.
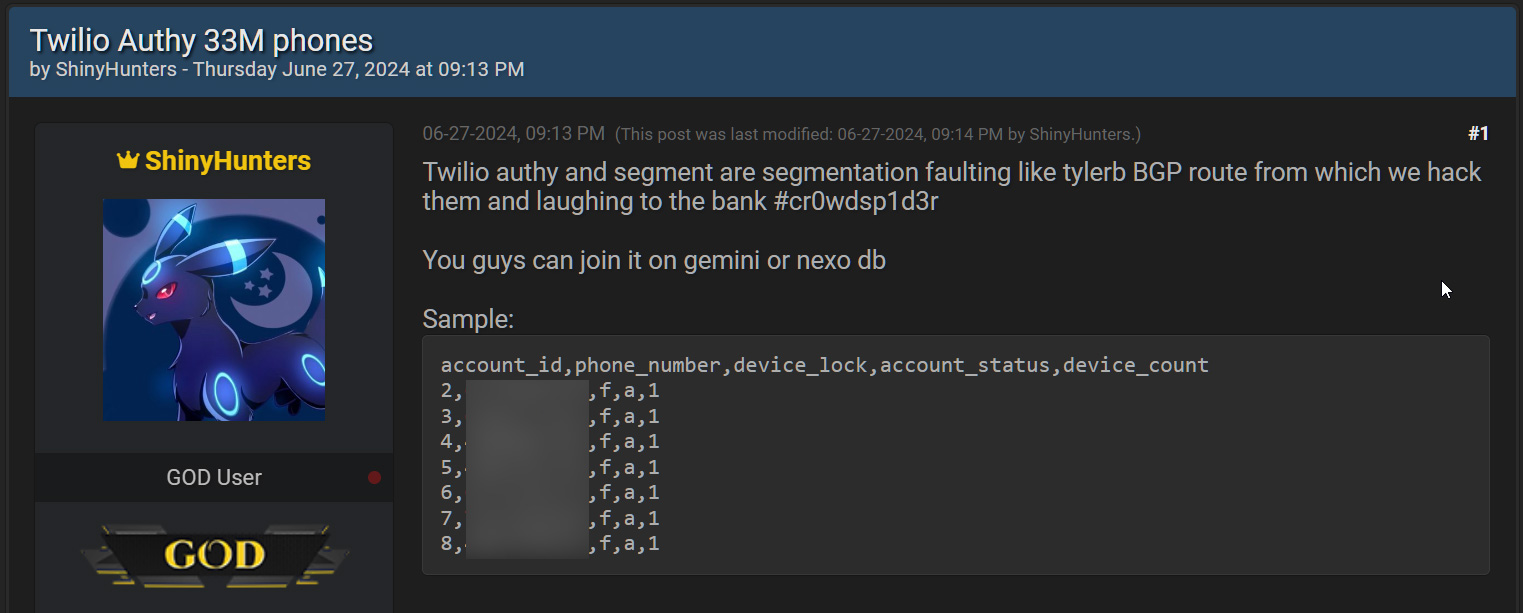
Source: BleepingComputer
The CSV file contains 33,420,546 rows, each containing an account ID, phone number, an “over_the_top” column, account status, and device count.
Twilio has now confirmed to BleepingComputer that the threat actors compiled the list of phone numbers using an unauthenticated API endpoint.
“Twilio has detected that threat actors were able to identify data associated with Authy accounts, including phone numbers, due to an unauthenticated endpoint. We have taken action to secure this endpoint and no longer allow unauthenticated requests,” Twilio told BleepingComputer.
“We have seen no evidence that the threat actors obtained access to Twilio’s systems or other sensitive data. As a precaution, we are requesting all Authy users to update to the latest Android and iOS apps for the latest security updates and encourage all Authy users to stay diligent and have heightened awareness around phishing and smishing attacks.”
Abusing unsecured APIs
BleepingComputer has learned that the data was compiled by feeding a massive list of phone numbers into the unsecured API endpoint. If the number was valid, the endpoint would return information about the associated accounts registered with Authy.
Now that the API has been secured, it can no longer be abused to verify whether a phone number is used with Authy.
This technique is similar to how threat actors abused an unsecured Twitter API and Facebook API to compile profiles of tens of millions of users that contain both public and non-public information.
While the Authy scrape only contained phone numbers, they can still be advantageous to users looking to conduct smishing and SIM swapping attacks to breach accounts.
ShinyHunters alludes to this in their post, stating, “You guys can join it on gemini or Nexo db,” suggesting that threat actors compare the list of phone numbers to those leaked in alleged Gemini and Nexo data breaches.
If matches are found, the threat actors could attempt to perform SIM swapping attacks or phishing attacks to breach the cryptocurrency exchange accounts and steal all the assets.
Twilio has now released a new security update and recommends that users upgrade to Authy Android (v25.1.0) and iOS App (v26.1.0), which includes security updates. It is unclear how this security update helps to protect users from threat actors using the scraped data in attacks.
Authy users should also ensure their mobile accounts are configured to block number transfers without providing a passcode or turning off security protections.
Furthermore, Authy users should be on the lookout for potential SMS phishing attacks that attempt to steal more sensitive data, such as passwords.
In what appears to be an unrelated breach, Twilio has also begun sending data breach notifications after a third-party vendor’s unsecured AWS S3 bucket exposed SMS-related data sent through the company.
Source link
lol
Twilio has confirmed that an unsecured API endpoint allowed threat actors to verify the phone numbers of millions of Authy multi-factor authentication users, potentially making them vulnerable to SMS phishing and SIM swapping attacks. Authy is a mobile app that generates multi-factor authentication codes at websites where you have MFA enabled. In late June, a…
Recent Posts
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
