A threat actor that was previously observed using an open-source network mapping tool has greatly expanded their operations to infect over 1,500 victims.
Sysdig, which is tracking the cluster under the name CRYSTALRAY, said the activities have witnessed a 10x surge, adding it includes “mass scanning, exploiting multiple vulnerabilities, and placing backdoors using multiple [open-source software] security tools.”
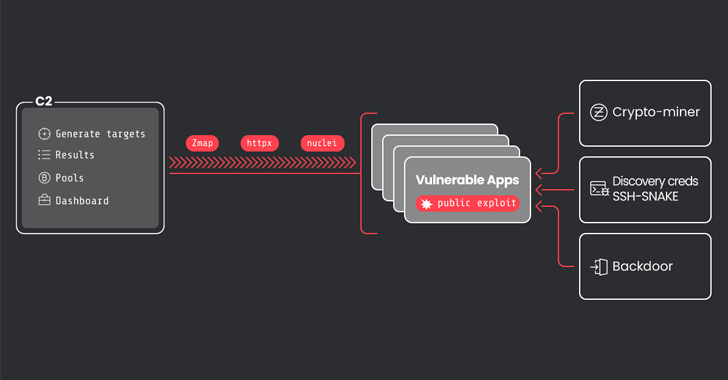
The primary objective of the attacks is to harvest and sell credentials, deploy cryptocurrency miners, and maintain persistence in victim environments.
Prominent among the open-source programs used by the threat actor is SSH-Snake, which was first released in January 2024. It has been described as a tool to carry out automatic network traversal using SSH private keys discovered on systems.
The abuse of the software by CRYSTALRAY was documented by the cybersecurity company earlier this February, with the tool deployed for lateral movement following the exploitation of known security flaws in public-facing Apache ActiveMQ and Atlassian Confluence instances.
Joshua Rogers, the developer behind SSH-Snake told The Hacker News at the time that the tool only automates what would have been otherwise manual steps, and called on companies to “discover the attack paths that exist – and fix them.”
Some of the other tools employed by the attackers include asn, zmap, httpx, and nuclei in order to check if a domain is active and launch scans for vulnerable services such as Apache ActiveMQ, Apache RocketMQ, Atlassian Confluence, Laravel, Metabase, Openfire, Oracle WebLogic Server, and Solr.

CRYSTALRAY also weaponizes its initial foothold to conduct a wide-ranging credential discovery process that goes beyond moving between servers accessible via SSH. Persistent access to the compromised environment is accomplished by means of a legitimate command-and-control (C2) framework called Sliver and a reverse shell manager codenamed Platypus.
In a further bid to derive monetary value from the infected assets, cryptocurrency miner payloads are delivered to illicitly use the victim resources for financial gain, while simultaneously taking steps to terminate competing miners that may have already been running on the machines.
“CRYSTALRAY is able to discover and extract credentials from vulnerable systems, which are then sold on black markets for thousands of dollars,” Sysdig researcher Miguel Hernández said. “The credentials being sold involve a multitude of services, including Cloud Service Providers and SaaS email providers.”