Small but mighty: Top 5 hacking tools that can fit in your pocket
by nlqip
While blue teams defend, red teams attack. They share a common goal, however – help identify and address gaps in organizations’ defenses before these weaknesses can be exploited by malicious actors. The blue/red team exercises provide invaluable insights across the technical, procedural and human sides of security and can ultimately help organizations fend off actual attacks.
We recently looked at a few open-source tools that blue teams may use while defending against simulated attacks, as well as at four gadgets that could, in the wrong hands, cause security trouble. This time around, we’ll round up five cutting-edge, compact tools that hobbyist hardware hackers as well as red teamers or ethical hackers may wield while honing their skills or doing their job.
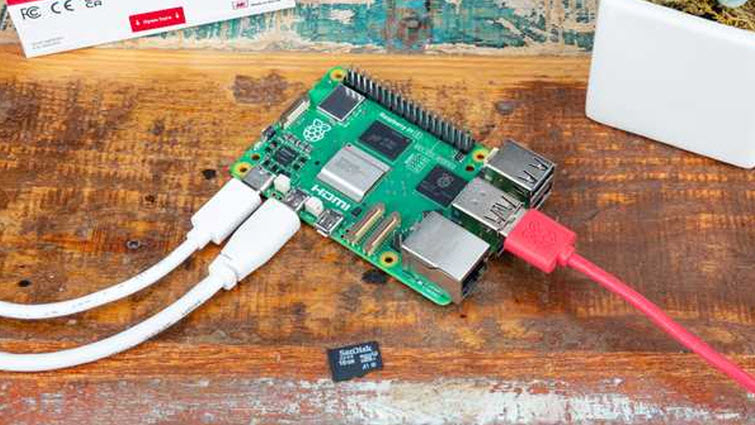
1. Raspberry Pi 5
Thanks especially to its versatility, power and vibrant community-driven ecosystem, the Raspberry Pi has become a favored tool among security professionals, students, and enthusiasts alike. Primarily an affordable single-board computer, Raspberry Pi can also be loaded with various penetration testing tools and serve multiple roles.
It can, for example, ‘morph’ into a network sniffer and capture packets for detailed analysis or run scripts for automated security tests. It’s also ideal for on-the-go testing of tools and for analyzing Internet of Things (IoT) devices, identifying vulnerabilities before cybercriminals have the chance to exploit them.
The Raspberry Pi supports a variety of operating systems tailored to different purposes and user preferences. Its official operating system, Raspberry Pi OS (formerly Raspbian), is based on Debian Linux and is optimized for the ARM architecture.
Additionally, popular distributions like Kali Linux are available, and they’re specifically crafted for penetration testing and security auditing. These distributions come pre-loaded with a suite of tools for network scanning, vulnerability assessment, wireless attacks, and more.
Also, here are a few interesting tools and projects that can leverage Raspberry Pi as the underlying hardware platform:
- FruityWifi: Used to audit wireless networks and enable advanced attacks via a web interface.
- Ha-Pi: Provides tools for penetration testing, including Aircrack Ng Suite and Metasploit.
- Raspberry Pwn: Includes tools like scapy, Wireshark, and tcpdump.
- Wireless Attack Toolkit (WAT): Performs Wi-Fi network penetration testing on ARM platforms.
- PwnPi: A simplified version of Debian Wheezy for pentesting.
- NetPi: A project aimed at creating a network analyzer with commercial-grade features.
2. HackRF One
The HackRF One is a Swiss army knife for radio frequency (RF) enthusiasts and professionals alike. This open-source device lets everybody from curious hobbyists to seasoned professionals dive into the invisible ocean of RFs and explore and manipulate the waves that carry everything from your favorite music station to critical communication signals.
Designed to be versatile, this single-board software-defined radio (SDR) peripheral can both transmit and receive signals from 1 MHz to 6 GHz. This vast range means you can experiment with virtually any type of wireless communication, from AM/FM radio to Wi-Fi and even satellite signals. It’s almost like having the keys to every wireless protocol ever conceived, all in one compact form factor.
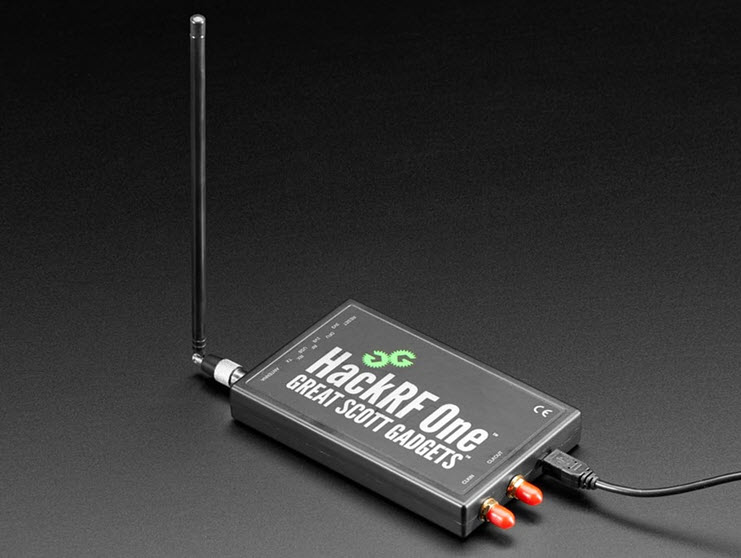
Despite its advanced capabilities, HackRF One is portable and robust enough for fieldwork, allowing security professionals to test wireless network vulnerabilities or RF engineers to troubleshoot signal issues on the go.
Speaking of which, it lets you assess the security of wireless systems, perform replay attacks, and explore the vulnerabilities of IoT devices. This includes emulating and analyzing car remote controls, alarms, and other devices, manipulating GPS signals, communicating with RFID tags, and performing signal analysis and satellite communication tracking.
3. WiFi Pineapple
Admittedly, you may need a larger pocket for this one, but this sleek gadget that looks like an innocuous router holds the power to uncover the hidden secrets of wireless networks. The WiFi Pineapple is used for probing the security of wireless networks by simulating a conventional access point where it attracts unsuspecting users. It has two network interfaces: one for providing internet access and the other for interacting with nearby Wi-Fi devices.

At the core of the WiFi Pineapple is its custom operating system, Pineapple OS. This Linux-based OS is specifically intended for wireless penetration testing and comes pre-loaded with a plethora of powerful tools. Pineapple OS provides a stable and efficient environment, ensuring that the device operates smoothly during complex security assessments.
Key purposes:
- Evil twin attacks: Creates rogue access points to intercept network traffic and gather sensitive information.
- Deauth tests: Forces disconnections from legitimate networks to enable man-in-the-middle attacks.
- Security assessments: Identifies vulnerabilities and configuration gaps in wireless networks.
- Controlled attacks: Helps administrators understand and develop better security policies.
- Versatile functionality: Provides various automated and manual wireless network pentesting tools.
4. Deauther Watch
The name says it all. Essentially a wearable that integrates capabilities for executing Wi-Fi deauthentication attacks, this gadget disrupts the Wi-Fi connection between a device (such as a smartphone, laptop, or IoT device) and a Wi-Fi router by sending specially crafted deauthentication packets.
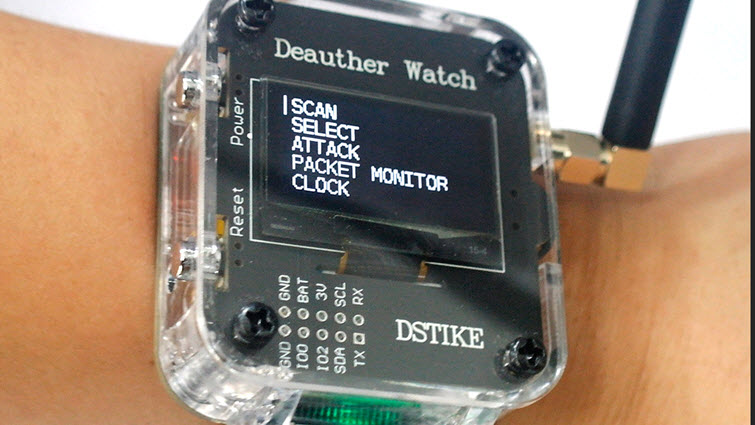
Additionally, the Deauther Watch may come with features such as Wi-Fi scanning and monitoring, and packet capturing to detect vulnerabilities or monitor network activity. The ESP8266 Deauther V3 software provides a command-line interface (CLI) via USB and tests 2.4 GHz WiFi networks for vulnerabilities.
5. Ubertooth One
The Ubertooth One is primarily designed for monitoring Bluetooth communications and analyses of Bluetooth packets, as well as for the testing of Bluetooth-enabled Internet of Things (IoT) devices. This open-source gadget supports various security testing scenarios, including sniffing for sensitive information exchanged over Bluetooth connections. Indeed, its capabilities of extend beyond typical Bluetooth adapters and it can be customized to meet specific security testing needs.
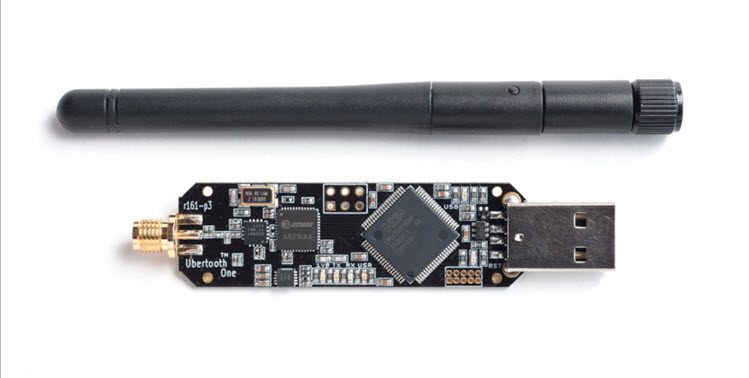
It is based on the GreatFET platform and features a capable radio transceiver chipset. The Ubertooth One operates in the 2.4 GHz ISM band and supports Bluetooth Low Energy (BLE) and Classic Bluetooth protocols, making it versatile enough to tackle a wide range of applications.
Conclusion
As with all gadgets of this kind, ethical considerations are paramount. The tech needs to be used in environments and situations where permission is granted, such as in controlled testing environments or for educational purposes. Indeed, using them to conduct unsanctioned attacks is illegal in many jurisdictions and can come with severe consequences. Meanwhile, organizations need to implement a combination of technical measures, policies, and user education so that they stay safe from unauthorized use of these devices on their networks.
Source link
lol
While blue teams defend, red teams attack. They share a common goal, however – help identify and address gaps in organizations’ defenses before these weaknesses can be exploited by malicious actors. The blue/red team exercises provide invaluable insights across the technical, procedural and human sides of security and can ultimately help organizations fend off actual…
Recent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA
