Surge in Magniber ransomware attacks impact home users worldwide
by nlqip

A massive Magniber ransomware campaign is underway, encrypting home users’ devices worldwide and demanding thousand-dollar ransoms to receive a decryptor.
Magniber launched in 2017 as a successor to the Cerber ransomware operation when it was spotted being distributed by the Magnitude exploit kit.
Since then, the ransomware operation has seen bursts of activity over the years, with the threat actors utilizing various methods to distribute Magniber and encrypt devices. These tactics include using Windows zero-days, fake Windows and browser updates, and trojanized software cracks and key generators.
Unlike the larger ransomware operations, Magniber has primarily targeted individual users who download malicious software and execute it on their home or small business systems.
In 2018, AhnLab released a decryptor for the Magniber ransomware. However, it no longer works as the threat actors fixed the bug allowing free file decryption.
Ongoing Magniber campaign
Since July 20, BleepingComputer has seen a surge in Magniber ransomware victims seeking help in our forums.
Ransomware identification site ID-Ransomware has also seen a surge, with almost 720 submissions to the site since July 20, 2024.
While it unclear how victims are being infected, BleepingComputer has been told by a few victims that their device was encrypted after running software cracks or key generators, which is a method the threat actors used in the past.
Once launched, the ransomware encrypts files on the device and appends a random 5-9 character extension, like .oaxysw or .oymtk, to encrypted file names.
The ransomware will also create a ransom note named READ_ME.htm, which contains information about what happened to a person’s files and a unique URL to the threat actor’s Tor ransom site.
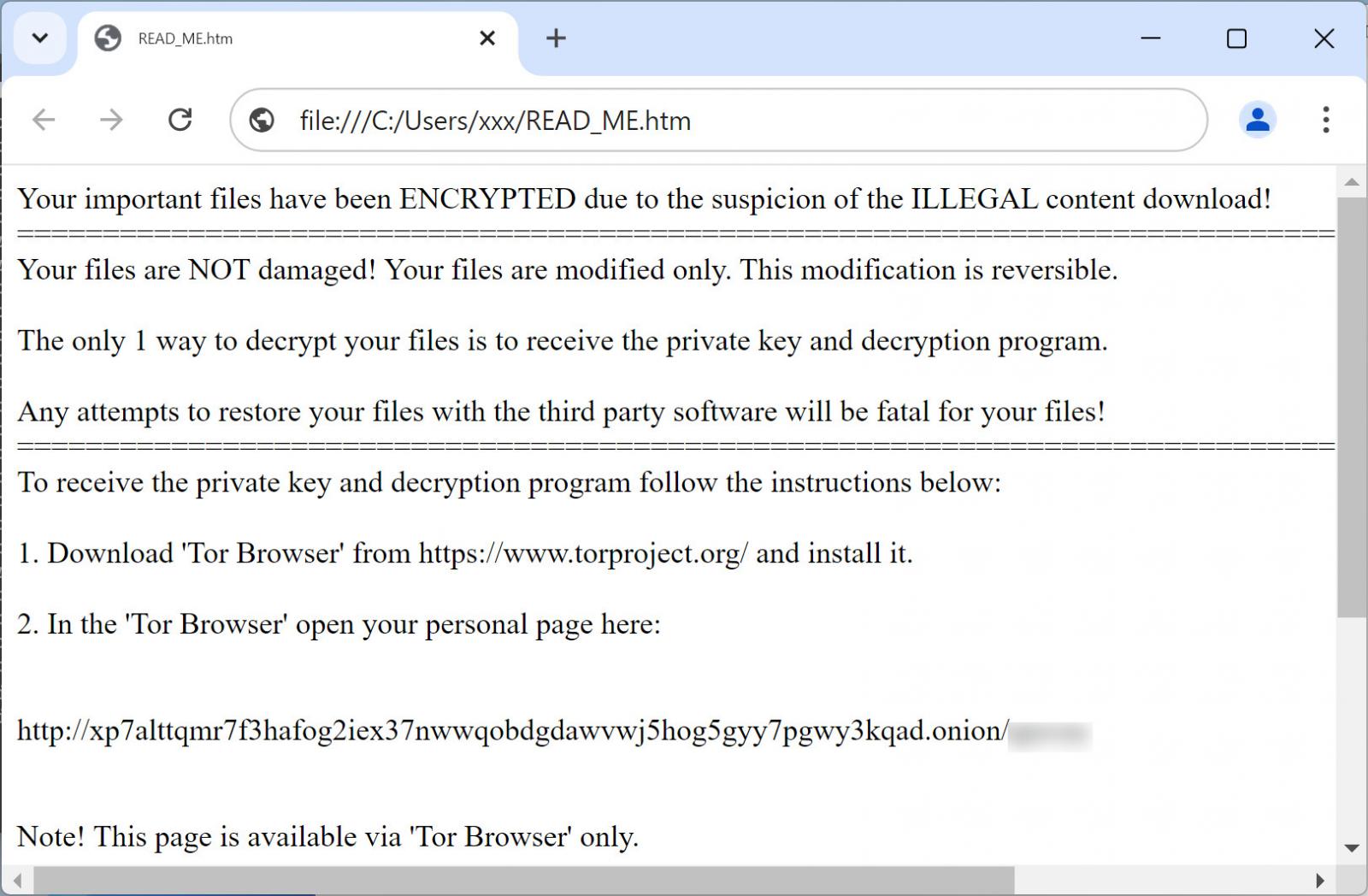
Source: BleepingComputer
As Magniber typically targets consumers, the ransom demands start at $1,000 and then increase to $5,000 if a Bitcoin payment is not made within three days.
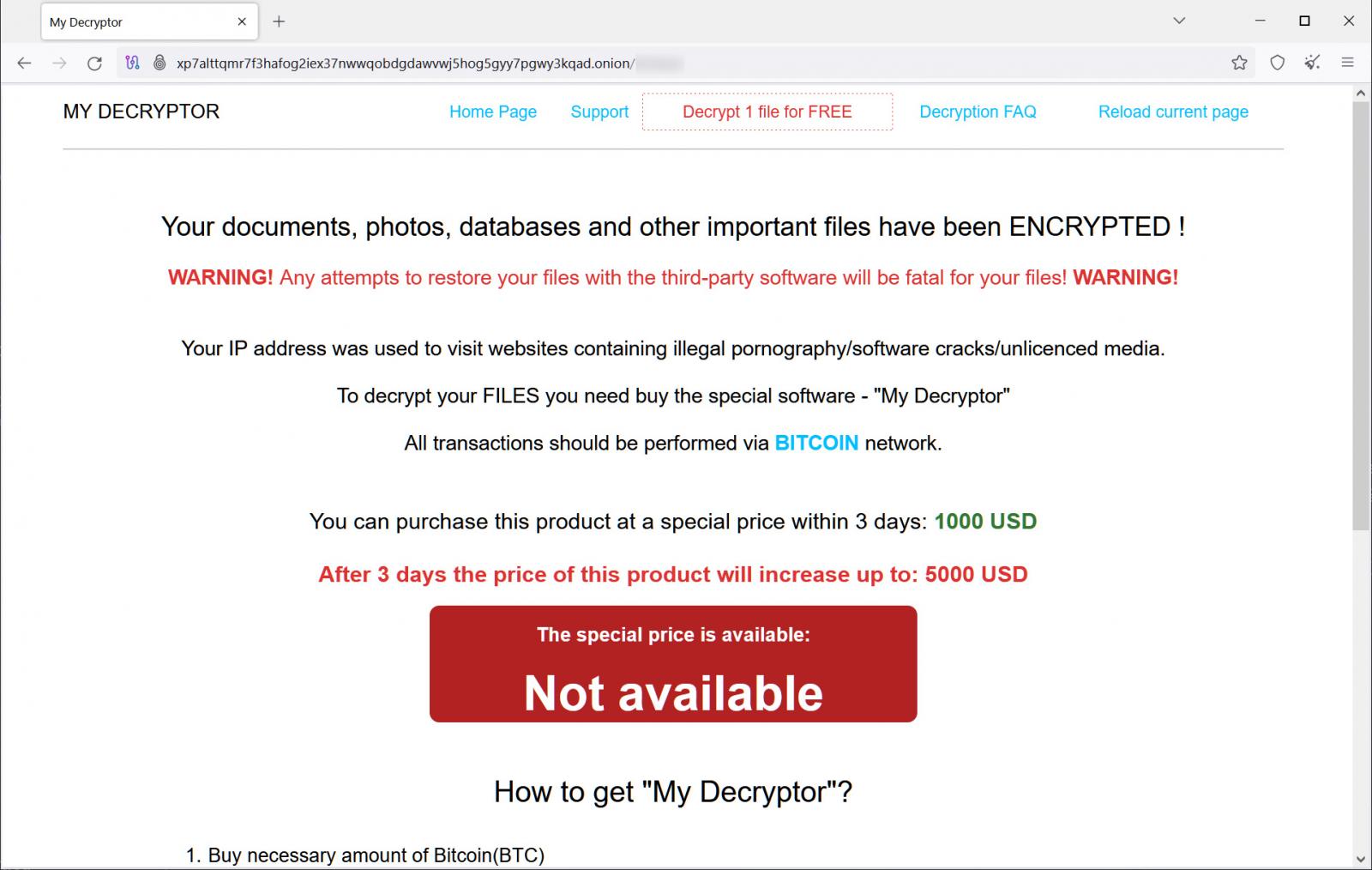
Source: BleepingComputer
Unfortunately, there is no way to decrypt files encrypted by the current versions of Magniber for free.
It is strongly advised to avoid software cracks and key generators as it’s not only illegal but also a common method used to distribute malware and ransomware.
For those impacted by the ransomware, you can use our dedicated Magniber support topic to receive help or receive answers to questions.
Source link
lol
A massive Magniber ransomware campaign is underway, encrypting home users’ devices worldwide and demanding thousand-dollar ransoms to receive a decryptor. Magniber launched in 2017 as a successor to the Cerber ransomware operation when it was spotted being distributed by the Magnitude exploit kit. Since then, the ransomware operation has seen bursts of activity over the…
Recent Posts
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
