Hackers are exploiting critical bug in LiteSpeed Cache plugin
by nlqip

Hackers have already started to exploit the critical severity vulnerability that affects LiteSpeed Cache, a WordPress plugin used for accelerating response times, a day after technical details become public.
The security issue is tracked as CVE-2024-28000 and allows escalating privileges without authentication in all versions of the WordPress plugin up to 6.3.0.1.
The vulnerability stems from a weak hash check in the plugin’s user simulation feature which can be exploited by attackers brute-forcing the hash value to create rogue admin accounts.
This could lead to a complete takeover of the affected websites, allowing the installation of malicious plugins, altering critical settings, redirecting traffic to malicious sites, and stealing user data.
Patchstack’s Rafie Muhammad shared the details on how to trigger the hash generation in a post yesterday, showing how to brute-force the hash to escalate privileges and then create a new administrator account via the REST API.
Muhammad’s method demonstrated that a brute force attack cycling through all 1 million possible security hash values at three requests per second can gain site access as any user ID in as little as a few hours and as much as a week.
LiteSpeed Cache is used by over 5 million sites. As of this writing, only about 30% run a safe version of the plugin, leaving an attack surface of millions of vulnerable websites.
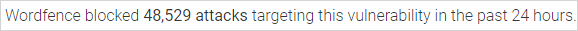
WordPress security firm Wordfence reports that it has detected and blocked over 48,500 attacks targeting CVE-2024-28000 over the last 24 hours, a figure that reflects intense exploitation activity.
Wordfence’s Chloe Charmberland warned about this scenario yesterday, saying, “We have no doubts that this vulnerability will be actively exploited very soon.”
This is the second time this year that hackers have targeted LiteSpeed Cache. In May, attackers used a cross-site scripting flaw (CVE-2023-40000) to create rogue administrator accounts and take over vulnerable websites.
At the time, WPScan reported that threat actors began scanning for targets in April, with over 1.2 million probes detected from a single malicious IP address.
Users of LiteSpeed Cache are recommended to upgrade to the latest available version, 6.4.1, as soon as possible or uninstall the plugin from your website.
Source link
lol
Hackers have already started to exploit the critical severity vulnerability that affects LiteSpeed Cache, a WordPress plugin used for accelerating response times, a day after technical details become public. The security issue is tracked as CVE-2024-28000 and allows escalating privileges without authentication in all versions of the WordPress plugin up to 6.3.0.1. The vulnerability stems from…
Recent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA
