Windows vulnerability abused braille “spaces” in zero-day attacks
by nlqip
A recently fixed “Windows MSHTML spoofing vulnerability” tracked under CVE-2024-43461 is now marked as previously exploited after it was used in attacks by the Void Banshee APT hacking group.
When first disclosed as part of the September 2024 Patch Tuesday, Microsoft had not marked the vulnerability as previously exploited. However, on Friday, Microsoft updated the CVE-2024-43461 advisory to indicate it had been exploited in attacks before it was fixed.
The flaw’s discovery was attributed to Peter Girnus, a Senior Threat Researcher at Trend Micro’s Zero Day, who told BleepingComputer that the CVE-2024-43461 flaw was exploited in zero-day attacks by Void Banshee to install information-stealing malware.
Void Banshee is an APT hacking group first tracked by Trend Micro that targets organizations in North America, Europe, and Southeast Asia to steal data and for financial gain.
The CVE-2024-43461 zero-day
In July, Check Point Research and Trend Micro both reported on the same attacks that exploited Windows zero-days to infect devices with the Atlantida info-stealer, used to steal passwords, authentication cookies, and cryptocurrency wallets from infected devices.
The attacks utilized zero-days tracked as CVE-2024-38112 (fixed in July) and CVE-2024-43461 (fixed this month) as part of the attack chain.
The discovery of the CVE-2024-38112 zero-day was attributed to Check Point researcher Haifei Li, who says it was used to force Windows to open malicious websites in Internet Explorer rather than Microsoft Edge when launching specially crafted shortcut files.
“Specifically, the attackers used special Windows Internet Shortcut files (.url extension name), which, when clicked, would call the retired Internet Explorer (IE) to visit the attacker-controlled URL,” explained Li in a July Check Point Research report.
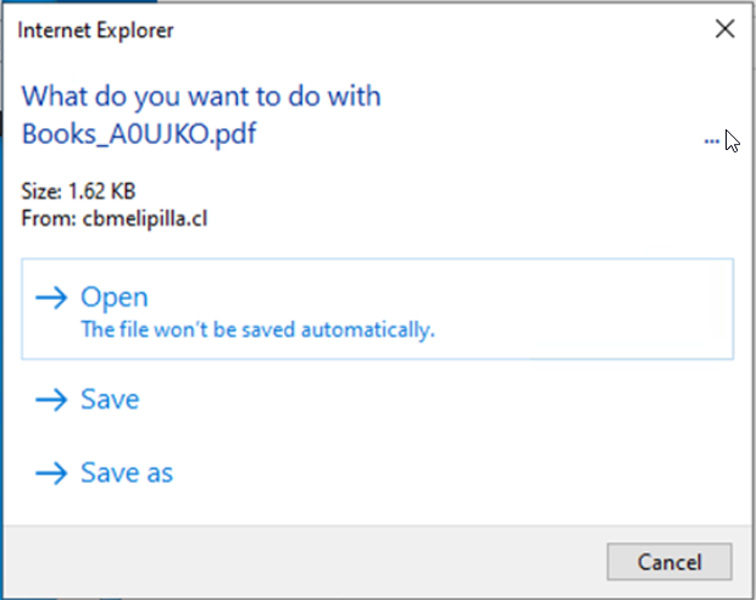
These URLs were used to download a malicious HTA file and prompt the user to open it. When opened, a script would run to install the Atlantida info-stealer.
The HTA files utilized a different zero-day tracked as CVE-2024-43461 to hide the HTA file extension and make the file appear as a PDF when Windows prompted users as to whether it should be opened, as shown below.
ZDI researcher Peter Girnus told BleepingComputer that the CVE-2024-43461 flaw was also used in the Void Banshee attacks to create a CWE-451 condition through HTA file names that included 26 encoded braille whitespace characters (%E2%A0%80) to hide the .hta extension.
As you can see below, the file name starts as a PDF file but includes twenty-six repeated encoded braille whitespace characters (%E2%A0%80) followed by a final ‘.hta’ extension.
Books_A0UJKO.pdf%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80.hta
When Windows opens this file, the braille whitespace characters push the HTA extension outside the user interface, only delineated by a ‘…’ string in Windows prompts, as seen below. This caused the HTA files to appear as PDF files, making them more likely to be opened.
Source: Trend Micro
After installing the security update for CVE-2024-43461, Girnus says the whitespace is not stripped, but Windows now shows the actual .hta extension for the file in prompts.
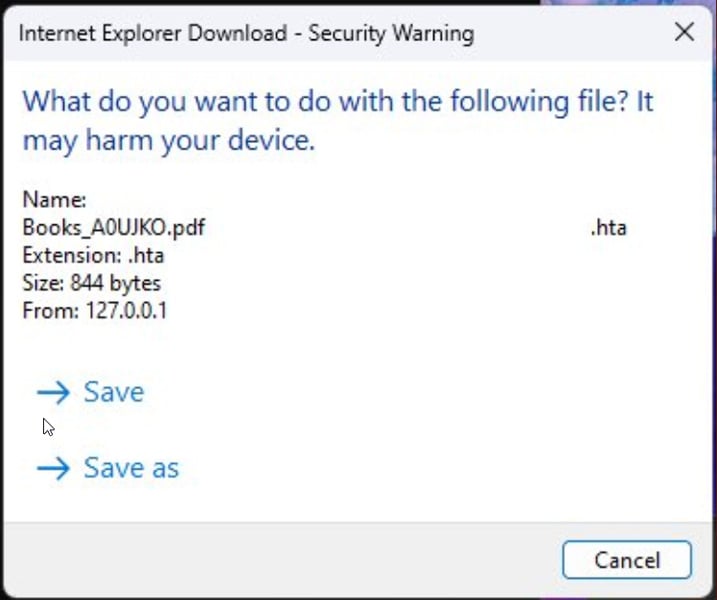
Source: Peter Girnus
Unfortunately, this fix is not perfect, as the included whitespace will likely still confuse people into thinking the file is a PDF rather than an HTA file.
Microsoft fixed three other actively exploited zero-days in the September Patch Tuesday, including CVE-2024-38217, which was exploited in LNK stomping attacks to bypass the Mark of the Web security feature.
Source link
lol
A recently fixed “Windows MSHTML spoofing vulnerability” tracked under CVE-2024-43461 is now marked as previously exploited after it was used in attacks by the Void Banshee APT hacking group. When first disclosed as part of the September 2024 Patch Tuesday, Microsoft had not marked the vulnerability as previously exploited. However, on Friday, Microsoft updated the CVE-2024-43461 advisory…
Recent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA
