Critical Veeam RCE bug now used in Frag ransomware attacks
by nlqip

After being used in Akira and Fog ransomware attacks, a critical Veeam Backup & Replication (VBR) security flaw was also recently exploited to deploy Frag ransomware.
Code White security researcher Florian Hauser found that the vulnerability (tracked as CVE-2024-40711) is caused by a deserialization of untrusted data weakness that unauthenticated threat actors can exploit to gain remote code execution (RCE) on Veeam VBR servers.
watchTowr Labs, which published a technical analysis on CVE-2024-40711 on September 9, delayed releasing a proof-of-concept exploit until September 15 to give admins enough time to apply security updates issued by Veeam on September 4.
Code White also delayed sharing more details when it disclosed the flaw because it “might instantly be abused by ransomware gangs.”
These delays were prompted by Veeam’s VBR software being a popular target for threat actors seeking quick access to a company’s backup data since many businesses use it as a disaster recovery and data protection solution to back up, restore, and replicate virtual, physical, and cloud machines.
However, Sophos X-Ops incident responders found that this did very little to delay Akira and Fog ransomware attacks. The threat actors exploited the RCE flaw together with stolen VPN gateway credentials to add rogue accounts to the local Administrators and Remote Desktop Users groups on unpatched and Internet-exposed servers.
More recently, Sophos also discovered that the same threat activity cluster (tracked as “STAC 5881”) used CVE-2024-40711 exploits in attacks that led to Frag ransomware being deployed on compromised networks.
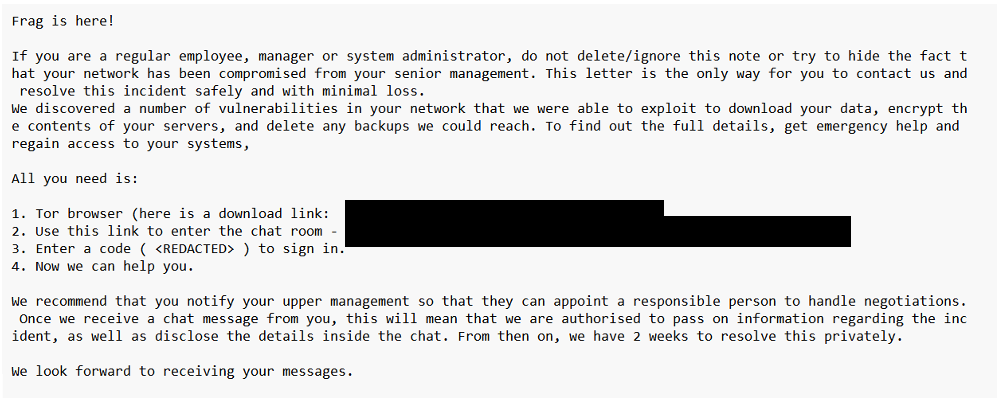
”In a recent case MDR analysts once again observed the tactics associated with STAC 5881 – but this time observed the deployment of a previously-undocumented ransomware called ‘Frag,'” said Sean Gallagher, a principal threat researcher at Sophos X-Ops.
“Similar to the previous events, the threat actor used a compromised VPN appliance for access, leveraged the VEEAM vulnerability, and created a new account named ‘point’. However in this incident a ‘point2’ account was also created.”
In a recent report, British cybersecurity company Agger Labs said that the recently surfaced Frag ransomware gang extensively uses Living Off The Land binaries (LOLBins) in their attacks—legitimate software already available on compromised systems—making it challenging for defenders to detect their activity.
They also have a similar playbook to Akira and Fog operators, as they’ll likely target unpatched vulnerabilities and misconfigurations in backup and storage solutions during their attacks.
In March 2023, Veeam patched another high-severity VBR vulnerability (CVE-2023-27532) that can let malicious actors breach backup infrastructure. Months later, a CVE-2023-27532 exploit (used in attacks linked to the financially motivated FIN7 threat group) was deployed in Cuba ransomware attacks targeting U.S. critical infrastructure organizations.
Veeam says over 550,000 customers worldwide use its products, including roughly 74% of all companies in the Global 2,000 list.
Source link
lol
After being used in Akira and Fog ransomware attacks, a critical Veeam Backup & Replication (VBR) security flaw was also recently exploited to deploy Frag ransomware. Code White security researcher Florian Hauser found that the vulnerability (tracked as CVE-2024-40711) is caused by a deserialization of untrusted data weakness that unauthenticated threat actors can exploit to…
Recent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA
