Cybersecurity Snapshot: CISA Warns of Global Spear-Phishing Threat, While OWASP Releases AI Security Resources
by nlqip

CISA is warning about a spear-phishing campaign that spreads malicious RDP files. Plus, OWASP is offering guidance about deepfakes and AI security. Meanwhile, cybercriminals have amplified their use of malware for fake software-update attacks. And get the latest on CISA’s international plan, Interpol’s cyber crackdown and ransomware trends.
Dive into six things that are top of mind for the week ending Nov. 8.
1 – CISA: Beware of nasty spear-phishing campaign
Proactively restrict outbound remote-desktop protocol (RDP) connections. Block transmission of RDP files via email. Prevent RDP file execution.
Those are three security measures cyber teams should proactively take in response to an ongoing and “large scale” email spear-phishing campaign targeting victims with malicious RDP files, according to the U.S. Cybersecurity and Infrastructure Security Agency (CISA).
A foreign threat actor is carrying out the campaign. Several vertical sectors, including government and IT, are being targeted.
“Once access has been gained, the threat actor may pursue additional activity, such as deploying malicious code to achieve persistent access to the target’s network,” CISA’s alert reads.
Other CISA recommendations include:
- Adopt phishing-resistant multi-factor authentication (MFA), such as FIDO tokens, and try to avoid SMS-based MFA
- Educate users on how to spot suspicious emails
- Hunt for malicious activity in your network using indicators of compromise (IoCs) and tactics, techniques and procedures
Although CISA didn’t name the hacker group responsible for this campaign, its alert includes links to related articles from Microsoft and AWS that identify it as Midnight Blizzard. Also known as APT29, this group is affiliated with Russia’s government.
To get more details, check out the CISA alert “Foreign Threat Actor Conducting Large-Scale Spear-Phishing Campaign with RDP Attachments.”
For more information about securing RDP tools:
2 – OWASP issues AI security resources
How should your organization respond to deepfakes? What’s the right way of establishing a center of excellence for AI security in your organization? Where can you find a comprehensive guide of tools to secure generative AI applications?
You’ll find answers to these questions in a new set of resources for AI security from the Open Worldwide Application Security Project’s OWASP Top 10 for LLM Application Security Project.
The new resources are meant to help organizations securely adopt, develop and deploy LLM and generative AI systems and applications “with a comprehensive strategy encompassing governance, collaboration and practical tools,” OWASP said in a statement.
These are the new resources:
- “The Guide for Preparing and Responding to Deepfake Events,” which unpacks four types of deepfake schemes – financial fraud, job interview fraud, social engineering and misinformation – and offers guidance about each one in these areas:
- preparation
- detection and analysis
- containment eradication and recovery
- post-incident activity
- “The LLM and GenAI Center of Excellence Guide,” which aims to help CISOs and fellow organization leaders create a center of excellence for generative AI security that facilitates collaboration among various teams, including security, legal, data science and operations, so they can develop:
- Generative AI security policies
- Risk assessment and management processes
- Training and awareness
- Research and development
- “The AI Security Solution Landscape Guide,” which offers security teams a comprehensive catalog of open source and commercial tools for securing LLMs and generative AI applications.
To get more details, read OWASP’s announcement “OWASP Dramatically Expands GenAI Security Guidance.”
For more information about protecting your organization against deepfakes:
3 – Fake update variants dominate list of top malware in Q3
Hackers are doubling down on fake software-update attacks.
That’s the main takeaway from the Center for Internet Security’s list of the 10 most prevalent malware used during the third quarter.
Malware variants used to carry out fake browser-update attacks took the top four spots in the list: SocGholish, LandUpdate808, ClearFake and ZPHP. Collectively, they accounted for 77% of the quarter’s malware infections.

(Source: “Top 10 Malware Q3 2024”, Center for Internet Security, October 2024)
In a fake software-update attack, a victim gets duped into installing a legitimate-looking update for, say, their preferred browser, that instead infects their computers with malware.
Here’s the full list, in descending order:
- SocGholish, a downloader distributed through malicious websites that tricks users into downloading it by offering fake software updates
- LandUpdate808, a JavaScript downloader distributed through malicious websites via fake browser updates.
- ClearFake, another JavaScript downloader used for fake browser-update attacks.
- ZPHP, another JavaScript downloader used for fake software-update attacks.
- Agent Tesla, a remote access trojan (RAT) that captures credentials, keystrokes and screenshots
- CoinMiner, a cryptocurrency miner that spreads using Windows Management Instrumentation (WMI)
- Arechclient2, also known as SectopRAT, is a .NET RAT whose capabilities include multiple stealth functions
- Mirai, a malware botnet that compromises IoT devices to launch DDoS attacks
- NanoCore, a RAT that spreads via malspam as a malicious Excel spreadsheet
- Lumma Stealer, an infostealer used to swipe personally identifiable information (PII), credentials, cookies and banking information
To get more information, the CIS blog “Top 10 Malware Q3 2024” offers details, context and indicators of compromise for each malware strain.
For details on fake update attacks:
VIDEO
Fake Chrome Update Malware (The PC Security Channel)
4 – CISA’s first international plan unveiled
CISA has released its first-ever international plan, which outlines a strategy for boosting the agency’s collaboration with cybersecurity agencies from other countries.
Aligning cybersecurity efforts and goals with international partners is critical for tackling cyberthreats in the U.S. and abroad, according to the agency.

The three core pillars of CISA’s “2025 – 2026 International Strategic Plan” are:
- Help make more resilient other countries’ assets, systems and networks that impact U.S. critical infrastructure
- Boost the integrated cyber defenses of the U.S. and its international partners against their shared global cyberthreats
- Unify the coordination of international activities to strengthen cyberdefenses collectively
The plan will allow CISA to “reduce risk to the globally interconnected and interdependent cyber and physical infrastructure that Americans rely on every day,” CISA Director Jen Easterly said in a statement.
5 – Interpol hits phishers, ransomware gangs, info stealers
Interpol and its partners took down 22,000 malicious IP addresses and seized thousands of servers, laptops, and mobile phones used by cybercriminals to conduct phishing scams, deploy ransomware and steal information.
The four-month global operation, titled Synergia II and announced this week, involved law enforcement agencies and private-sector partners from 95 countries and netted 41 arrests.

“Together, we’ve not only dismantled malicious infrastructure but also prevented hundreds of thousands of potential victims from falling prey to cybercrime,” Neal Jetton, Director of Interpol’s Cybercrime Directorate, said in a statement.
In Hong Kong, more than 1,000 servers were taken offline, while authorities in Macau, China took another 291 servers offline. Meanwhile, in Estonia, authorities seized 80GB of server data, which is now being analyzed for links to phishing and banking malware.
For more information about global cybercrime trends:
6 – IST: Ransomware attacks surged in 2023
Ransomware gangs went into hyperdrive last year, increasing their attacks by 73% compared with 2022, according to the non-profit think tank Institute for Security and Technology (IST).
The IST attributes the sharp increase in attacks to a shift by ransomware groups to “big game hunting” – going after prominent, large organizations with deep pockets.
“Available evidence suggests that government and industry actions taken in 2023 were not enough to significantly reduce the profitability of the ransomware model,” reads an IST blog.
Global Ransomware Incidents in 2023
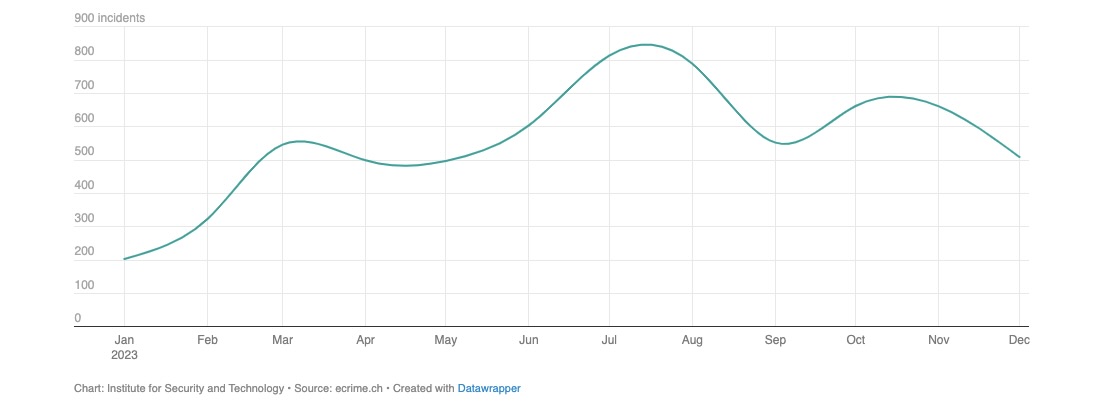
Another takeaway: The ransomware-as-a-service (RaaS) model continued to prove extremely profitable in 2023, and it injected dynamism into the ransomware ecosystem.
The RaaS model prompted ransomware groups “to shift allegiances, form new groups, or iterate existing variants,” the IST blog reads.
The industry sector that ransomware groups hit the hardest was construction, followed by hospitals and healthcare, and by IT services and consulting. Financial services and law offices rounded out the top five.
To learn more about ransomware trends:
Source link
lol
CISA is warning about a spear-phishing campaign that spreads malicious RDP files. Plus, OWASP is offering guidance about deepfakes and AI security. Meanwhile, cybercriminals have amplified their use of malware for fake software-update attacks. And get the latest on CISA’s international plan, Interpol’s cyber crackdown and ransomware trends. Dive into six things that are top…
Recent Posts
- Hackers abuse Avast anti-rootkit driver to disable defenses
- Microsoft testing Windows 11 support for third-party passkeys
- Windows 11 24H2 update blocked on PCs with Assassin’s Creed, Star Wars Outlaws
- Windows 10 KB5046714 update fixes bug preventing app uninstalls
- Eight Key Takeaways From Kyndryl’s First Investor Day
