Android malware ‘Necro’ infects 11 million devices via Google Play
by nlqip

A new version of the Necro Trojan malware for Android was installed on 11 million devices through Google Play in malicious SDK supply chain attacks.
This new version of the Necro Trojan was installed through malicious advertising software development kits (SDK) used by legitimate apps, Android game mods, and modified versions of popular software, such as Spotify, WhatsApp, and Minecraft.
Necro installs several payloads to infected devices and activates various malicious plugins, including:
- Adware that loads links through invisible WebView windows (Island plugin, Cube SDK)
- Modules that download and execute arbitrary JavaScript and DEX files (Happy SDK, Jar SDK)
- Tools specifically designed to facilitate subscription fraud (Web plugin, Happy SDK, Tap plugin)
- Mechanisms that use infected devices as proxies to route malicious traffic (NProxy plugin)
Necro Trojan on Google Play
Kaspersky discovered the presence of Necro loader on two apps on Google Play, both of which have a substantial userbase.
The first one is Wuta Camera by ‘Benqu,’ a photo editing and beautification tool with over 10,000,000 downloads on Google Play.
Source: BleepingComputer
The threat analysts report that Necro appeared on the app with the release of version 6.3.2.148, and it remained embedded until version 6.3.6.148, which is when Kaspersky notified Google.
While the trojan was removed in version 6.3.7.138, any payloads that might have been installed via the older versions might still lurk on Android devices.
The second legitimate app that carried Necro is Max Browser by ‘WA message recover-wamr,’ which had 1 million downloads on Google Play until it was removed, following Kaspersky’s report.
Kaspersky claims that Max Browser’s latest version, 1.2.0, still carries Necro, so there’s no clean version available to upgrade to, and users of the web browser are recommended to uninstall it immediately and switch to a different browser.
Kaspersky says the two apps were infected by an advertising SDK named ‘Coral SDK,’ which employed obfuscation to hide its malicious activities and also image steganography to download the second-stage payload, shellPlugin, disguised as harmless PNG images.
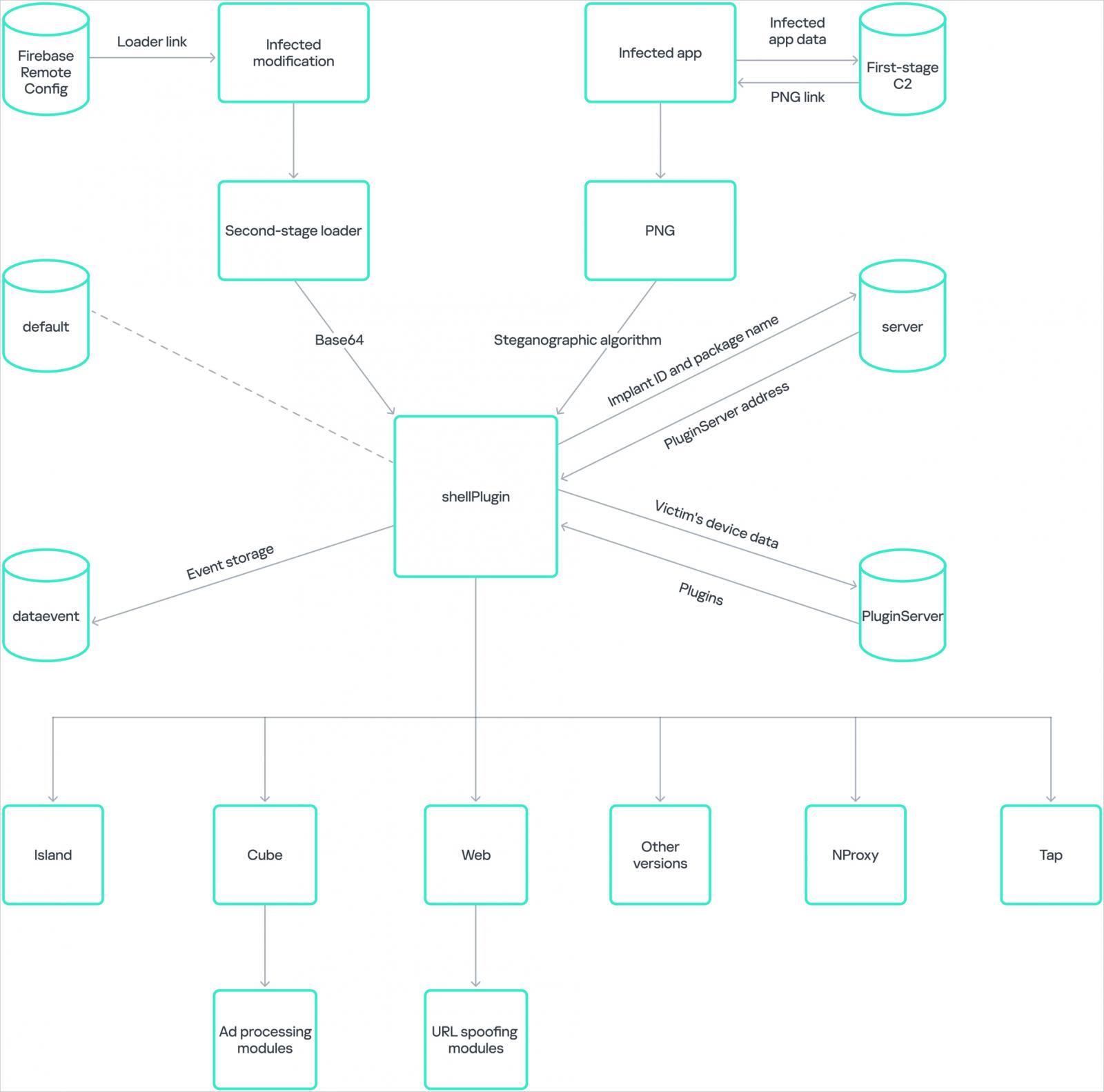
Source: Kaspersky
Google told BleepingComputer they were aware of the reported apps and were investigating them.
Outside official sources
Outside the Play Store, the Necro Trojan is spread primarily through modified versions of popular apps (mods) that were distributed via unofficial websites.
Notable examples spotted by Kaspersky include WhatsApp mods ‘GBWhatsApp’ and ‘FMWhatsApp,’ which promise better privacy controls and extended file-sharing limits. Another is the Spotify mod, ‘Spotify Plus,’ which promises free access to ad-free premium services.
Source: Kaspersky
The report also mentions Minecraft mods and mods for other popular games like Stumble Guys, Car Parking Multiplayer, and Melon Sandbox, which were infected with the Necro loader.
In all cases, the malicious behavior was the same—displaying ads in the background to generate fraudulent revenue for the attackers, installing apps and APKs without the user’s consent, and using invisible WebViews to interact with paid services.
As unofficial Android software websites do not report download numbers reliably, the total number of infections by this latest Necro Trojan wave is unknown, but it is at least 11 million from Google Play.
Source link
lol
A new version of the Necro Trojan malware for Android was installed on 11 million devices through Google Play in malicious SDK supply chain attacks. This new version of the Necro Trojan was installed through malicious advertising software development kits (SDK) used by legitimate apps, Android game mods, and modified versions of popular software, such as Spotify,…
Recent Posts
- Windows 10 KB5046714 update fixes bug preventing app uninstalls
- Eight Key Takeaways From Kyndryl’s First Investor Day
- QNAP pulls buggy QTS firmware causing widespread NAS issues
- N-able Exec: ‘Cybersecurity And Compliance Are A Team Sport’
- Hackers breach US firm over Wi-Fi from Russia in ‘Nearest Neighbor Attack’
