Infostealer malware bypasses Chrome’s new cookie-theft defenses
by nlqip

Infostealer malware developers released updates claiming to bypass Google Chrome’s recently introduced feature App-Bound Encryption to protect sensitive data such as cookies.
App-Bound Encryption was introduced in Chrome 127 and is designed to encrypt cookies and stored passwords using a Windows service that runs with system privileges.
This model does not allow infostealer malware, which runs with the permissions of the logged user, to steal secrets stored in Chrome browser.
To bypass this protection, the malware would need system privileges or to inject code into Chrome, both noisy actions that are likely to trigger warnings from security tools, said Will Harris of the Chrome security team.
However, security researchers g0njxa and also RussianPanda9xx obseerved multiple infostealer developers boasting that they have implemented a working bypass for their tools (MeduzaStealer, Whitesnake, Lumma Stealer, Lumar (PovertyStealer), Vidar Stealer, StealC).
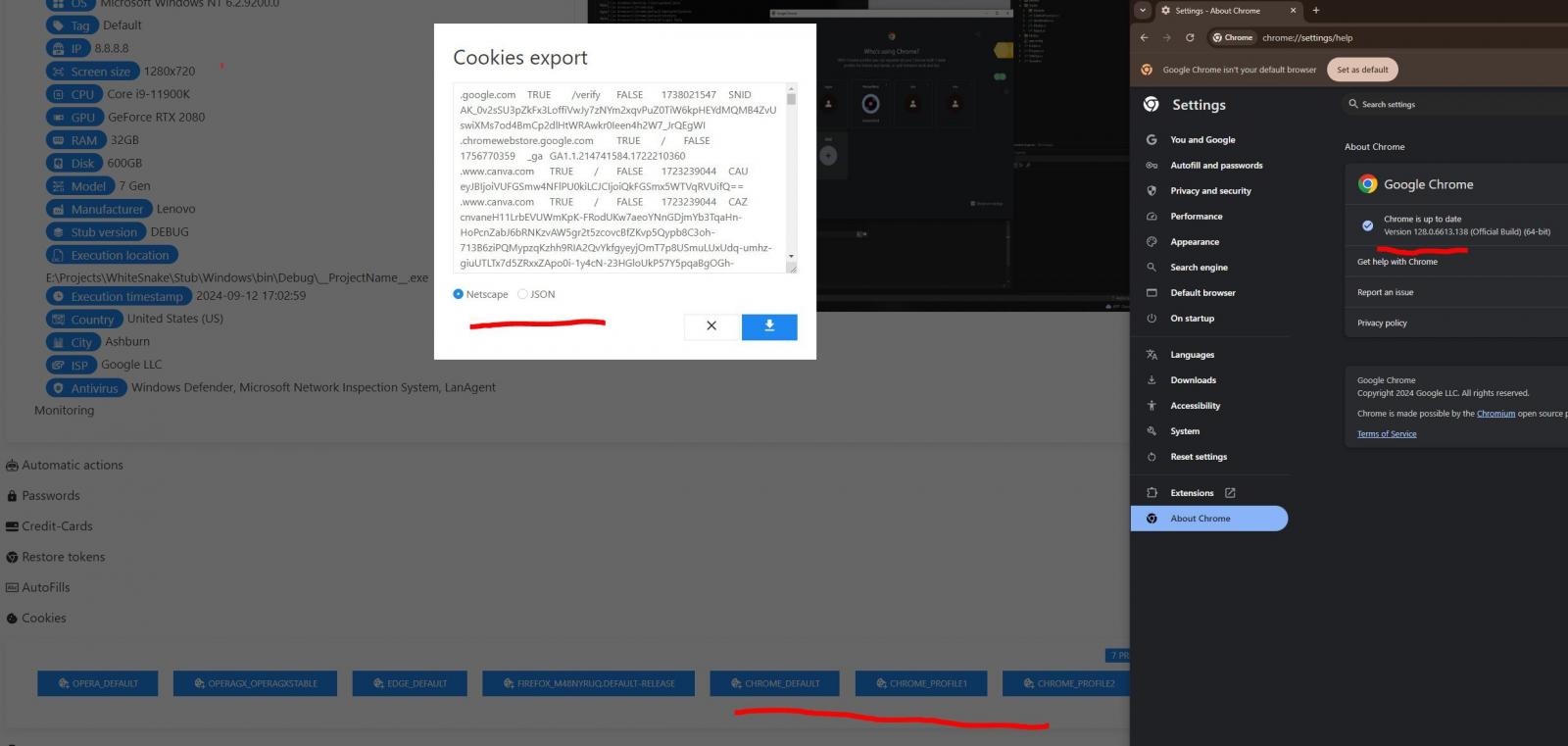
Source: @g0njxa
It appears that at least some of the claims are real, as g0njxa confirmed for BleepingComputer that the latest variant of Lumma Stealer can bypass the encryption feature in Chrome 129, the currently the most recent version of the browser.
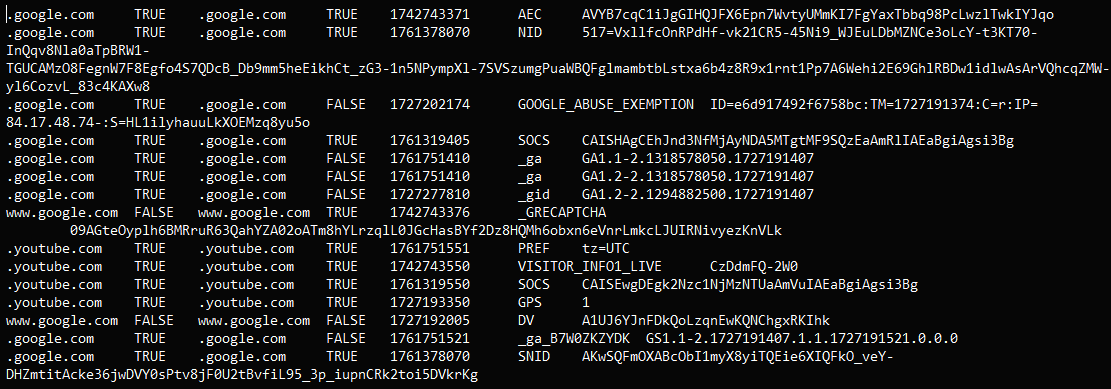
Source: @g0njxa
The researcher tested the malware on a Windows 10 Pro system in a sandbox environment.
In terms of timing, Meduza, and WhiteSnake implemented their bypassing mechanisms over two weeks ago, Lumma last week, and Vidar and StealC this week.
Lumar initially responded to App-Bound Encryption by implementing a temporary solution that required launching the malware with admin rights, but followed with a bypass mechanism that works with the privileges of the logged-in user.
The developers of Lumma Stealer assured its customer that they don’t need to execute the malware with admin privileges for the cookie theft to work.
“Added a new method of collecting Chrome cookies. The new method does not require admin rights and/or restart, which simplifies the crypt build and reduces the chances of detection, and thus increase the knock rate.” – developers of Lumma Stealer
How exactly the bypass of App-Bound Encryption is achieved remains undisclosed, but the authors of Rhadamanthys malware commented that it took them 10 minutes to reverse the encryption.
BleepingComputer contacted the tech giant for a comment about the malware developer’s response to App-Bound Encryption in Chrome but we are still waiting for a reply.
Source link
lol
Infostealer malware developers released updates claiming to bypass Google Chrome’s recently introduced feature App-Bound Encryption to protect sensitive data such as cookies. App-Bound Encryption was introduced in Chrome 127 and is designed to encrypt cookies and stored passwords using a Windows service that runs with system privileges. This model does not allow infostealer malware, which runs with the…
Recent Posts
- Windows 10 KB5046714 update fixes bug preventing app uninstalls
- Eight Key Takeaways From Kyndryl’s First Investor Day
- QNAP pulls buggy QTS firmware causing widespread NAS issues
- N-able Exec: ‘Cybersecurity And Compliance Are A Team Sport’
- Hackers breach US firm over Wi-Fi from Russia in ‘Nearest Neighbor Attack’
