DDoS site Dstat.cc seized and two suspects arrested in Germany
by nlqip
The Dstat.cc DDoS review platform has been seized by law enforcement, and two suspects have been arrested after the service helped fuel distributed denial-of-service attacks for years.
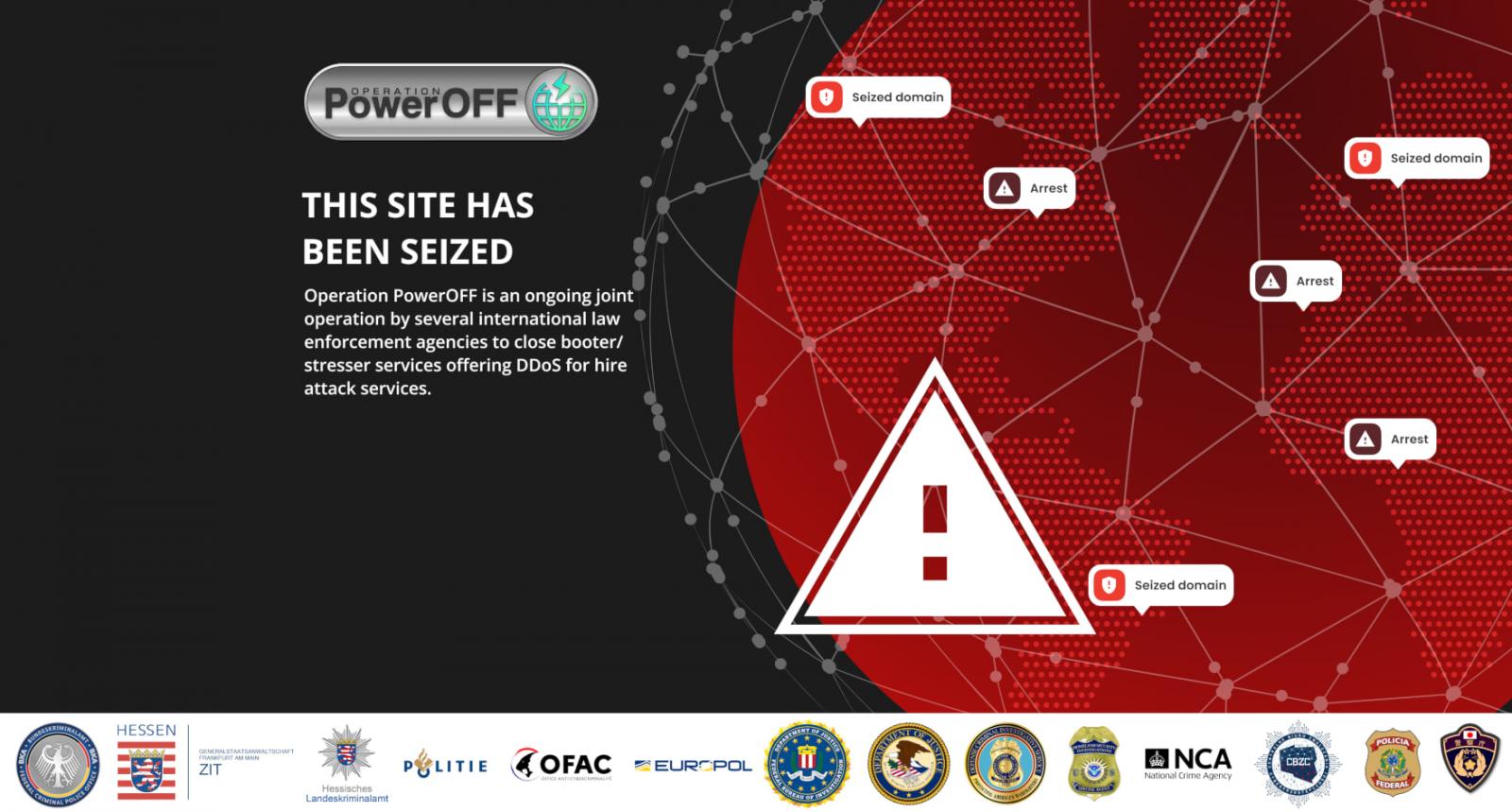
The seizure and arrests were conducted as part of “Operation PowerOFF,” an ongoing international law enforcement operation that targets DDoS-for-hire platforms, aka “booters” or “stressers,” to seize infrastructure and arrest the operators.
These platforms are responsible for service disruptions to online services and can cause significant economic damages, as well as impact to the operation of critical services, such as healthcare.
While Dstat.cc did not provide the DDoS attack services themselves, it helped facilitate attacks by allowing threat actors to showcase the effectiveness of their DDoS attack capabilities. It also provided reviews and recommendations on stressors that could be used for different types of attacks.
The service also hosted a Telegram channel under the same name with 6,600 members, which threat actors heavily used to discuss their latest attacks or offer their services.
BleepingComputer has confirmed that this Telegram channel has now been wiped of all messages and locked to prevent new discussions.
The police action targeting Dstat.cc, was spearheaded by the Central Office for Combating Cybercrime (ZIT) of the Frankfurt General Prosecutor’s Office, the Hesse State Criminal Police Office (HLKA), and the Federal Criminal Police Office (BKA)
The authorities arrested two suspects, aged 19 and 28, who are believed to be managing Dstat.cc and also the synthetic drugs market, “Flight RCS.” Flight RCS operated on the clear net, making it far more easily accessible to internet users.
“The platform enabled users, even without advanced technical skills, to perform DDoS attacks, disrupting or disabling online services,” explains BKA.
“Stresser services have recently gained attention in police investigations and are often used by hacktivist groups like Killnet.”
Source: BleepingComputer
The German police state that pro-Russia hacktivist group Killnet utilized Dstat.cc to showcase their attacks.
Passion, another pro-Russia “hacktivist” group, used Dstat.cc to demonstrate its L4 and L7 attack capabilities against DDoS mitigation services, as part of their attacks on hospitals and healthcare orgs in the US and Europe.
Searches and seizures were conducted in seven distinct locations in Germany, France, Greece, Iceland, and the United States.
The two arrested men now face charges under Section 127 of the German Criminal Code, which incur punishments of up to ten years in prison (maximum) and monetary fines.
Previously, Operation PowerOFF has taken down DigitalStress in the UK and arrested its suspected owner, and arrested two operators of a booter service in Poland. Other actions led to the seizure of 13 and 48 domains hosting stressor platforms in two separate enforcement waves.
DDoS attacks have seen increased usage for revenge, extortion, and hacktivism over the past couple of years. Many individuals also participate voluntarily in DDoS attacks, offering their device’s network connectivity to attack online platforms for political reasons.
However, DDoS attacks are illegal and a punishable crime in most jurisdictions. When the infrastructure of those services falls into the hands of the police, they are examined for forensic evidence leading to the identity of those who purchased access and carried out DDoS attacks.
Unfortunately, some who contribute their resources to attack gamers may not realize their actions are illegal. This caused the Dutch Police to send emails to customers of a seized DDoS platform, warning them that continued cyber offenses would lead to prosecution.
Source link
lol
The Dstat.cc DDoS review platform has been seized by law enforcement, and two suspects have been arrested after the service helped fuel distributed denial-of-service attacks for years. The seizure and arrests were conducted as part of “Operation PowerOFF,” an ongoing international law enforcement operation that targets DDoS-for-hire platforms, aka “booters” or “stressers,” to seize infrastructure and…
