D-Link won’t fix critical flaw affecting 60,000 older NAS devices
by nlqip

More than 60,000 D-Link network-attached storage devices that have reached end-of-life are vulnerable to a command injection vulnerability with a publicly available exploit.
The flaw, tracked as CVE-2024-10914, has a critical 9.2 severity score and is present in the ‘cgi_user_add’ command where the name parameter is insufficiently sanitized.
An unauthenticated attacker could exploit it to inject arbitrary shell commands by sending specially crafted HTTP GET requests to the devices.
The flaw impacts multiple models of D-Link network-attached storage (NAS) devices that are commonly used by small businesses:
- DNS-320 Version 1.00
- DNS-320LW Version 1.01.0914.2012
- DNS-325 Version 1.01, Version 1.02
- DNS-340L Version 1.08
In a technical write-up that provides exploit details, security researcher Netsecfish says that leveraging the vulnerability requires sending “a crafted HTTP GET request to the NAS device with malicious input in the name parameter.”
curl "http://[Target-IP]/cgi-bin/account_mgr.cgi cmd=cgi_user_add&name=%27;<INJECTED_SHELL_COMMAND>;%27"
“This curl request constructs a URL that triggers the cgi_user_add command with a name parameter that includes an injected shell command,” the researcher explains.
A search that Netsecfish conducted on the FOFA platform returned 61,147 results at 41,097 unique IP addresses for D-Link devices vulnerable to CVE-2024-10914.
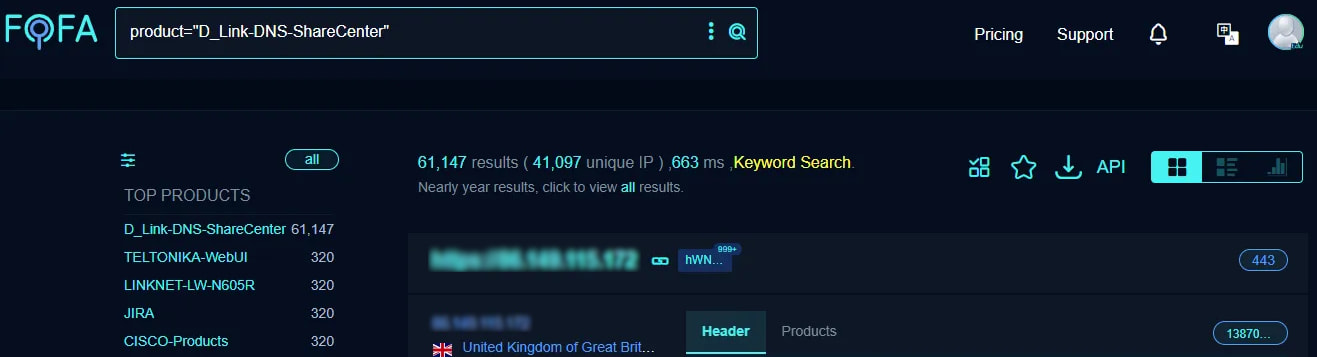
Source: Netsecfish
In a security bulletin today, D-Link has confirmed that a fix for CVE-2024-10914 is not coming and the vendor recommends that users retire vulnerable products.
If that is not possible at the moment, users should at least isolate them from the public internet or place them under stricter access conditions.
The same researcher discovered in April this year an arbitrary command injection and hardcoded backdoor flaw, tracked as CVE-2024-3273, impacting mostly the same D-Link NAS models as the latest flaw.
Back then, FOFA internet scans returned 92,589 results.
Responding to the situation at the time, a D-Link spokesperson told BleepingComputer that the networking firm no longer makes NAS devices, and the impacted products had reached EoL and will not be receiving security updates.
Source link
lol
More than 60,000 D-Link network-attached storage devices that have reached end-of-life are vulnerable to a command injection vulnerability with a publicly available exploit. The flaw, tracked as CVE-2024-10914, has a critical 9.2 severity score and is present in the ‘cgi_user_add’ command where the name parameter is insufficiently sanitized. An unauthenticated attacker could exploit it to inject…
Recent Posts
- Microsoft pulls WinAppSDK update breaking Windows 10 app uninstalls
- CISA says BianLian ransomware now focuses only on data theft
- Microsoft disrupts ONNX phishing-as-a-service infrastructure
- Five Cyber Agencies Sound Alarm About Active Directory Attacks: Beyond the Basics
- CISA Adds Three Known Exploited Vulnerabilities to Catalog | CISA
