Japan warns of attacks linked to North Korean Kimsuky hackers
by nlqip

Japan’s Computer Emergency Response Team Coordination Center (JPCERT/CC) is warning that Japanese organizations are being targeted in attacks by the North Korean ‘Kimsuky’ threat actors.
The US government has attributed Kimsuky as a North Korean advanced persistent threat (APT) group that conducts attacks against targets worldwide to gather intelligence on topics of interest to the North Korean government.
The threat actors are known to use social engineering and phishing to gain initial access to networks. They then deploy custom malware to steal data and retain persistence on networks.
Japan says Kimsuky attacks were detected earlier this year, and attribution was based on indicators of compromise (IoCs) shared by AhnLab Security Intelligence Center (ASEC) in two separate reports (1, 2).
“JPCERT/CC has confirmed attack activities targeting Japanese organizations by an attack group called Kimsuky in March 2024,” warns the JPCERT.
Starts with phishing
The attackers start their attacks by sending phishing emails impersonating security and diplomatic organizations to targets in Japan, carrying a malicious ZIP attachment.
The ZIP contains an executable that leads to malware infection and two decoy document files. The executable filename also uses many spaces to appear as a document, hiding the “.exe” part.
When executed by the victim, the payload downloads and executes a VBS file and also configures ‘C:UsersPublicPicturesdesktop.ini.bak’ to start automatically via Wscript.
The VBS file downloads a PowerShell script to collect information, such as process lists, network details, file lists from folders (Downloads, Documents, Desktop), and user account information. This information is then sent to a remote URL under the control of the attackers.
This collected information helps Kimsuky determine if the infected device is a legitimate user machine or an analysis environment.
Finally, a new VBS file is created and executed to download a PowerShell script that logs keystrokes and clipboard information, which is then sent to the attackers.
.png)
Source: JPCERT/CC
The information collected by the keylogger could include credentials allowing the threat actors to spread further into the organization’s systems and applications.
Latest Kimsuky attacks
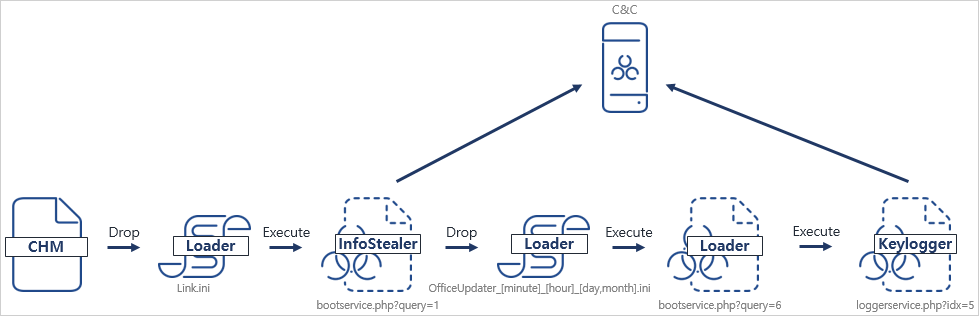
In May 2024, ASEC discovered Kimsuky was distributing a CHM malware strain in Korea. The malware had previously been spread in various formats, including LNK, DOC, and OneNote.
The attack flow involves executing a Compiled HTML Help (CHM) file that displays a help screen while simultaneously running a malicious script in the background.
Source: ASEC
This script creates and executes a file in the user’s profile path. The file then connects to an external URL to execute additional malicious Base64-encoded scripts.
These scripts are responsible for exfiltrating user information, creating and registering a malicious script as a service, and performing keylogging.
Compared to past variants, the latest malware samples seen by ASEC analysts employ more sophisticated obfuscation to evade detection.
Given the detected Kimsuky activity in Japan, the country’s CERT underlines the need for organizations to be vigilant against CHM files that can contain executable scripts designed to deliver malware.
Source link
lol
Japan’s Computer Emergency Response Team Coordination Center (JPCERT/CC) is warning that Japanese organizations are being targeted in attacks by the North Korean ‘Kimsuky’ threat actors. The US government has attributed Kimsuky as a North Korean advanced persistent threat (APT) group that conducts attacks against targets worldwide to gather intelligence on topics of interest to the…
