Author: nlqip
MS-ISAC ADVISORY NUMBER: 2024-106 DATE(S) ISSUED: 09/27/2024 OVERVIEW: Multiple vulnerabilities have been discovered in PHP, the most severe of which could allow for remote code execution. PHP is a programming language originally designed for use in web-based applications with HTML content. Successful exploitation could allow for remote code execution in the context of the affected…
Read MoreOrganizations face an ever-increasing array of sophisticated threats in today’s rapidly evolving cybersecurity landscape. Security Information and Event Management (SIEM) systems have become crucial tools in the fight against these threats. They provide real-time analysis of security alerts generated by various network hardware and software;’. However, the effectiveness of a SIEM solution heavily depends on…
Read MoreThe Data Protection Commission (DPC) in Ireland has fined Meta Platforms Ireland Limited (MPIL) €91 million ($100 million) for storing in plaintext passwords of hundreds of millions of users. The incident occurred in 2019. At the time, Meta disclosed it publicly and notified DPC, which initiated an investigation into the tech giant’s practices for storing…
Read MoreIn today’s rapidly evolving digital landscape, small and medium-sized businesses (SMBs) face an increasingly complex array of cybersecurity threats. As cyber-attacks become more sophisticated and frequent, more than traditional security measures are often needed to protect against these advanced threats. This is where Security Information and Event Management (SIEM) solutions come into play. Cloud-based SIEM…
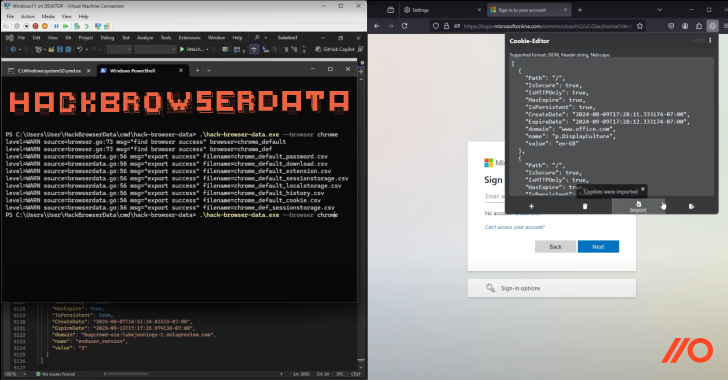
Read MoreAttackers are increasingly turning to session hijacking to get around widespread MFA adoption. The data supports this, as: 147,000 token replay attacks were detected by Microsoft in 2023, a 111% increase year-over-year (Microsoft). Attacks on session cookies now happen in the same order of magnitude as password-based attacks (Google). But session hijacking isn’t a new…
Read MoreA critical vulnerability in NVIDIA Container Toolkit impacts all AI applications in a cloud or on-premise environment that rely on it to access GPU resources. The security issue is tracked as CVE-2024-0132 and allows an adversary to perform container escape attacks and gain full access to the host system, where they could execute commands or exfiltrate sensitive information.…
Read MoreCritical security vulnerabilities have been disclosed in six different Automatic Tank Gauge (ATG) systems from five manufacturers that could expose them to remote attacks. “These vulnerabilities pose significant real-world risks, as they could be exploited by malicious actors to cause widespread damage, including physical damage, environmental hazards, and economic losses,” Bitsight researcher Pedro Umbelino said…
Read MoreIn today’s digital landscape, website security is paramount. WordPress has become an attractive target for cybercriminals as it continues to dominate the content management system (CMS) market, powering over 40% of all websites. Website owners are constantly seeking robust security solutions to protect their online assets. One question that often arises is: can a SIEM…
Read MoreMicrosoft warns that some Windows 11 systems enter reboot loops or might freeze with blue screens after installing the September 2024 KB5043145 preview update. This month’s KB5043145 optional update was released on Thursday with fixes for multiple issues, including Edge and task manager freezes. One day after this cumulative update rolled out, Redmond added a…
Read MoreOrganizations face an ever-increasing array of sophisticated threats in today’s rapidly evolving cybersecurity landscape. As cyber-attacks become more complex and frequent, the need for robust and efficient security measures has never been more critical. Endpoint Detection and Response (EDR) solutions have emerged as a crucial component of modern cybersecurity strategies. However, the effectiveness of these…
Read MoreRecent Posts
- Police bust pirate streaming service making €250 million per month
- The Black Friday 2024 Cybersecurity, IT, VPN, & Antivirus Deals
- Multiple Vulnerabilities in Mozilla Products Could Allow for Arbitrary Code Execution
- Nutanix Grows New Customers As Channel Engagement Increases, CEO Says
- Tenable Selected by Tohoku University to Secure External-Facing Assets Amidst Migration to the Cloud