Author: nlqip
Tenable Research discovered a remote code execution (RCE) vulnerability in Google Cloud Platform (GCP) that is now fixed and that we dubbed CloudImposer. The vulnerability could have allowed an attacker to hijack an internal software dependency that Google pre-installs on each Google Cloud Composer pipeline-orchestration tool. Tenable Research also found risky guidance in GCP documentation…
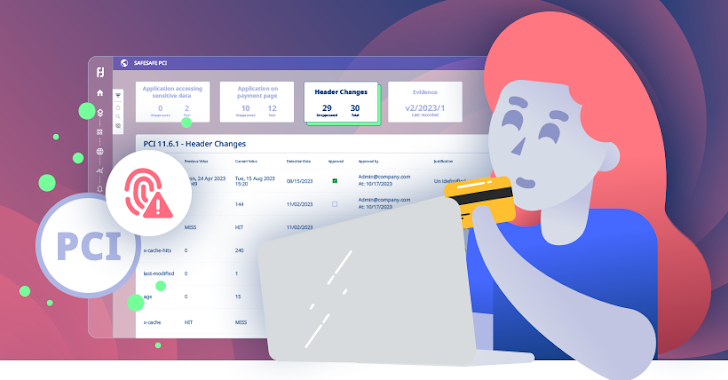
Read MoreSep 16, 2024The Hacker NewsPayment Security / Data Protection The PCI DSS landscape is evolving rapidly. With the Q1 2025 deadline looming ever larger, businesses are scrambling to meet the stringent new requirements of PCI DSS v4.0. Two sections in particular, 6.4.3 and 11.6.1, are troublesome as they demand that organizations rigorously monitor and manage…
Read MoreSep 16, 2024The Hacker NewsIdentity Protection / Incident Response Imagine this… You arrive at work to a chaotic scene. Systems are down, panic is in the air. The culprit? Not a rogue virus, but a compromised identity. The attacker is inside your walls, masquerading as a trusted user. This isn’t a horror movie, it’s the…
Read MorePerfect Forward Secrecy (PFS) is an important mode of modern encryption that secures the former and future sessions. It remains functional even if the current keys have already been compromised. Its primary function is to safeguard sensitive information, which prevents potential future data breaches. PFS is frequently used in security and privacy protocols across various…
Read MoreUsing Anti Data Exfiltration (ADX) to Stop Ransomware and Other Threats to Data Dr. EDWARD AMOROSO, FOUNDER & CEO, TAG This series of blogs developed by TAG Infosphere highlights a powerful new cybersecurity solution known as Anti Data Exfiltration (ADX) which provides on-device data security and threat protection. Commercial vendor BlackFog pioneered ADX which is…
Read MoreSep 16, 2024Ravie LakshmananSpyware / Threat Intelligence Apple has filed a motion to “voluntarily” dismiss its lawsuit against commercial spyware vendor NSO Group, citing a shifting risk landscape that could lead to exposure of critical “threat intelligence” information. The development was first reported by The Washington Post on Friday. The iPhone maker said its efforts,…
Read MoreCybersecurity researchers have warned of ongoing phishing campaigns that abuse refresh entries in HTTP headers to deliver spoofed email login pages that are designed to harvest users’ credentials. “Unlike other phishing webpage distribution behavior through HTML content, these attacks use the response header sent by a server, which occurs before the processing of the HTML…
Read MoreA malware campaign uses the unusual method of locking users in their browser’s kiosk mode to annoy them into entering their Google credentials, which are then stolen by information-stealing malware. Specifically, the malware “locks” the user’s browser on Google’s login page with no obvious way to close the window, as the malware also blocks the “ESC” and…
Read MoreThe Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) are alerting the public of false claims that the U.S. voter registration data has been compromised in cyberattacks. The two agencies note that malicious actors are spreading disinformation to manipulate public “opinion and undermine confidence in U.S. democratic institutions.” According to…
Read MoreA recently fixed “Windows MSHTML spoofing vulnerability” tracked under CVE-2024-43461 is now marked as previously exploited after it was used in attacks by the Void Banshee APT hacking group. When first disclosed as part of the September 2024 Patch Tuesday, Microsoft had not marked the vulnerability as previously exploited. However, on Friday, Microsoft updated the CVE-2024-43461 advisory…
Read MoreRecent Posts
- Tor needs 200 new WebTunnel bridges to fight censorship
- What Is a SOC Report, and Why Does Your Business Need One?
- Affordable and Effective: Best EDR Solutions for Small Business Affordable and Effective: Best EDR Solutions for Small Business
- Top Features to Look for in Endpoint Detection and Response Software Top Features to Look for in Endpoint Detection and Response Software
- What Does EDR Stand For in Threat Management? What Does EDR Stand For in Threat Management?