Author: nlqip
MS-ISAC ADVISORY NUMBER: 2024-061 DATE(S) ISSUED: 05/24/2024 OVERVIEW: A vulnerability has been discovered in Google Chrome that could allow for arbitrary code execution. Google Chrome is a web browser used to access the internet. Successful exploitation of this vulnerability could allow for arbitrary code execution in the context of the logged on user. Depending on…
Read MoreCisco released a bundled publication for security advisories that address vulnerabilities in Cisco Adaptive Security Appliance (ASA), Firepower Management Center (FMC), and Firepower Threat Defense (FTD) software. A cyber threat actor could exploit one of these vulnerabilities to take control of an affected system. Users and administrators are encouraged to review the following publication and…
Read MoreMay 24, 2024NewsroomMalvertising / Endpoint Security Threat actors have been observed making use of fake websites masquerading as legitimate antivirus solutions from Avast, Bitdefender, and Malwarebytes to propagate malware capable of stealing sensitive information from Android and Windows devices. “Hosting malicious software through sites which look legitimate is predatory to general consumers, especially those who…
Read MoreRansomware, on the other hand, saw a decline to 16%, from 23% of incidents in the preceding quarter, Kroll noted, possibly because of the law enforcement takedowns of ransomware-as-a-service organizations such as LockBit and BlackCat. Insider threats mostly malicious Insider threats, the report said, are hitting professional services hardest, accounting for 23% of incidents, with…
Read MoreThe main contributor was Nvidia’s data center revenue, which more than quintupled in the first quarter from the same period last year, growing 427 percent year-over-year to $22.5 billion. Nvidia once again reported triple-digit growth in revenue and profit in the latest quarter from the same period last year, a sign that demand for the…
Read MoreA data breach involving the Dutch city of Eindhoven left the personal information related to almost all of its citizens exposed. As Eindhovens Dagblad reports, two files containing the personal data of 221,511 inhabitants of Eindhoven were accessible to unauthorised parties for a period of time last year. Everyone who lives in the Netherlands has…
Read MoreCybersecurity Snapshot: EPA Urges Water Plants To Boost Cybersecurity, as OpenSSF Launches Threat Intel Platform for Open Source Software
by nlqip
Check out the EPA’s call for water plants to beef up their cyber defenses. Plus, open source developers have a new platform to share threat intelligence. Moreover, business email compromise attacks prompt alert from U.K.’s cyber agency. And CISA tackles DNS encryption best practices. And much more! Dive into six things that are top of…
Read MoreMay 24, 2024The Hacker NewsCybersecurity Webinar Don’t be fooled into thinking that cyber threats are only a problem for large organizations. The truth is that cybercriminals are increasingly targeting smaller businesses, and they’re getting smarter every day. Join our FREE webinar “Navigating the SMB Threat Landscape: Key Insights from Huntress’ Threat Report,” in which Jamie…
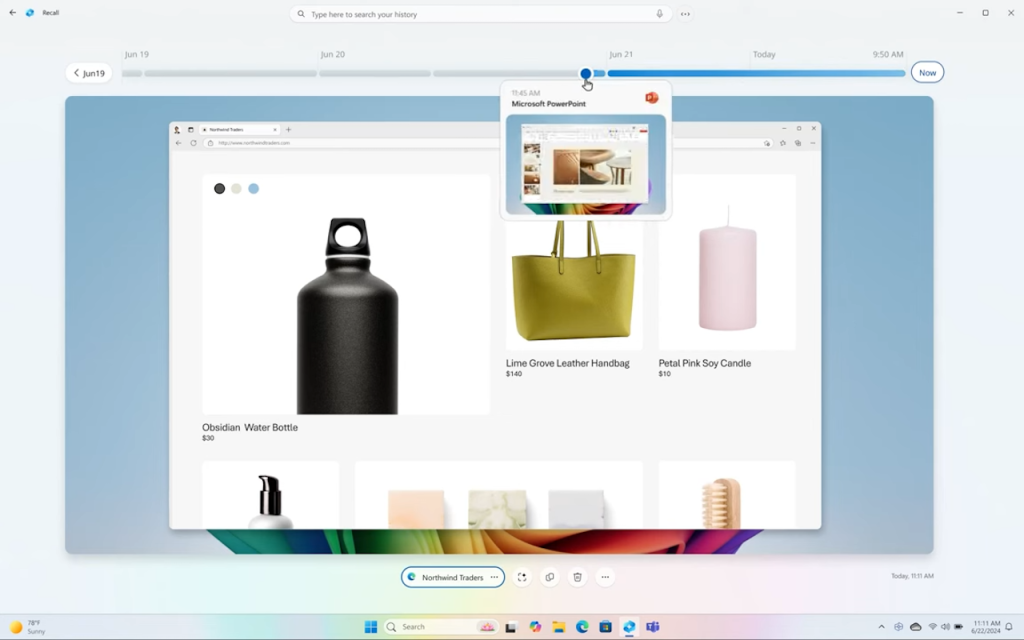
Read MoreJustin Lam, senior research analyst covering information security at S&P Global Market Intelligence, said that tackling security and privacy risks is common practice for businesses and shouldn’t necessarily preclude the use of tools shown to provide benefits to users and businesses. “Enterprises face challenges to balance user privacy, user productivity, internal risk management, surveillance, and compliance,” he…
Read MoreOn the Zero-Day Market New paper: “Zero Progress on Zero Days: How the Last Ten Years Created the Modern Spyware Market“: Abstract: Spyware makes surveillance simple. The last ten years have seen a global market emerge for ready-made software that lets governments surveil their citizens and foreign adversaries alike and to do so more easily…
Read MoreRecent Posts
- CISA: ‘Critical’ Palo Alto Networks Flaw Has Seen Exploitation
- CISA warns of critical Palo Alto Networks bug exploited in attacks
- Cisco’s Revamped Leadership To Pave The Way Toward Becoming A ‘Meaningfully Different’ Company: Exec
- Nokia says hackers leaked third-party app source code
- Ingram Micro’s Collaboration With AWS Is A ‘Game-Changer’ For Partners