Author: nlqip
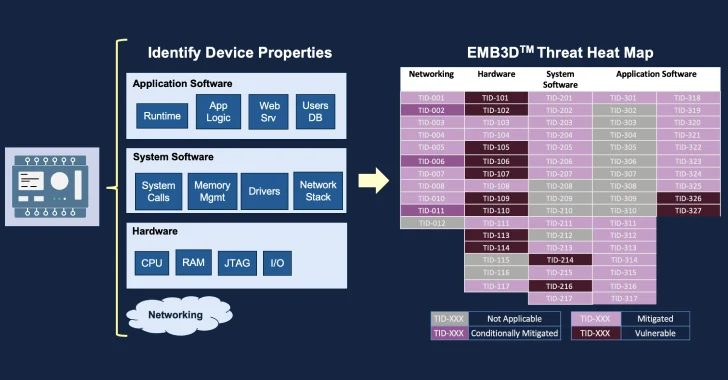
May 13, 2024Newsroom The MITRE Corporation has officially made available a new threat-modeling framework called EMB3D for makers of embedded devices used in critical infrastructure environments. “The model provides a cultivated knowledge base of cyber threats to embedded devices, providing a common understanding of these threats with the security mechanisms required to mitigate them,” the…
Read MorePhishing remains a pervasive cyber threat, utilizing various channels such as email, SMS, and phone calls to deceive victims into divulging sensitive information or downloading malware. With a history dating back to the 1990s, phishing has evolved into sophisticated techniques like spear phishing, business email compromise (BEC), and vishing. These attacks target individuals and organizations,…
Read MoreCISA has added one new vulnerability to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2024-4671 Google Chromium in Visuals Use-After-Free Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known…
Read MoreCRN spoke with the CEOs and CTOs of a number of cybersecurity companies, including Proofpoint, Palo Alto Networks, Rubrik and CrowdStrike, during RSA Conference 2024. Here’s what they had to say. While the many implications of GenAI for security continued to be discussed and debated at last week’s RSA Conference, an array of other issues…
Read MoreThese two related technologies — Secure Access Service Edge (SASE) and Secure Service Edge (SSE) — address a new set of challenges that enterprise IT faces as employees shifted to remote work and applications migrated to the cloud. Enterprise Buyer’s Guides, Network Security, Remote Access Security Source link lol
Read MoreThe Power 100 is culled from the ranks of CRN’s Women of the Channel and spotlights the female executives at vendors and distributors whose insight and influence help drive channel success. Each May, CRN honors 100 women who are driving the channel through their leadership, business acumen and partner advocacy. These women—named to the Power…
Read MoreAMD’s x86 CPU share gains against Intel in the desktop and server segments were due in part to ‘surprisingly strong’ shipments of the company’s Ryzen 5000 processors as well as its 4th– Gen EPYC chips in the first quarter, according to Mercury Research. AMD’s share in the x86 CPU market share inched upward against Intel…
Read MoreThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
by nlqip
May 13, 2024The Hacker NewsBrowser Security / Data Protection With the browser becoming the most prevalent workspace in the enterprise, it is also turning into a popular attack vector for cyber attackers. From account takeovers to malicious extensions to phishing attacks, the browser is a means for stealing sensitive data and accessing organizational systems. Security…
Read MoreLast week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit’s leader “LockBitSupp” claims the feds named the wrong guy, saying the charges don’t explain how they connected him to Khoroshev. This post examines the…
Read MoreThe breach has brought back into focus an earlier Europol security incident reported in March which involved the disappearance of physical personal records belonging to Catherine De Bolle, Europol’s executive director, and other senior officials before September 2023. Despite the agency’s assurances of minimal impact, questions are being raised about the security of data even…
Read More