Author: nlqip
As part of CRN’s 2024 Internet Of Things 50, here’s a look at 10 of the coolest and most noteworthy vendors who are innovating and making big moves within the industrial IoT space. Industrial solutions are expected to capture a large portion of IoT spending by businesses in the coming years, underlining a significant opportunity…
Read MoreThis Assurance Report Card (ARC) pulls together several of the key grouping based on assets type and risk levels to help the CISO understand the current state of the Vulnerability Management program. The National Banking and Securities Commission (CNBV) Annex 72 is a collection of 30 Key Risk Indicators (KRI) that establish compliance standards for…
Read MoreMedia Room
by nlqip
https://www.computing.co.uk/news/4195645/zero-days-fixed-microsofts-patch-tuesd… Source link lol
Read More“We’re responsibly investing in our company’s biggest priorities and the significant opportunities ahead,” a Google spokesperson said in an email. Google reportedly continues to conduct layoffs, this time letting go of employees in its finance and real estate units – but the company continues to invest in geographic growth hubs in Ireland, the U.S. and…
Read MoreIntroduction Over the past few months, F5 Labs has presented a series of articles on fake account creation. We’ve covered why fraudsters create fake accounts and how automation is used to create fake accounts at scale. These articles have described how these fake accounts can negatively impact businesses, but also how security professionals identify fake accounts and leverage security controls to stop bots running fake…
Read MoreIntroduction Disclosures of breaches often include mention of a “web shell” to further attacker ends. As one example, the Clop ransomware group (also known as ‘Lace Tempest,’ TA505, and FIN11) has used web shells as part of their attack chains in both the Kiteworks Accellion FTA breach of 2020 and the plethora of breaches related…
Read MoreScality’s New U.S. CEO: We’re Looking For Partners That Can ‘Bring Solutions To Solve Business Problems’
by nlqip
‘I know it sounds very basic, but it is somebody who wants to help a client, not just provide hardware and software, but can also lay out a services solution with their customers, help them get the solution set up, but also operationally create the blueprint of how the client is going to run the…
Read MoreThe executives tell CRN that AI-powered tools are making an impact on their day-to-day management of IT for customers. For MSPs on the front lines of managing IT systems for customers, tools for generative AI and other AI-powered capabilities are making an impact on their day-to-day operations. That’s the message that MSP executives shared with…
Read MoreIntroduction The first Chief Information Security Officer, or CISO, was named 29 years ago: After Russian hackers infiltrated financial services giant Citicorp (now Citigroup) in 1995 and stole more than $10 million, the Citigroup Board instructed the company’s CEO to recruit a security executive to improve the company’s digital defenses. That person was Steve Katz,…
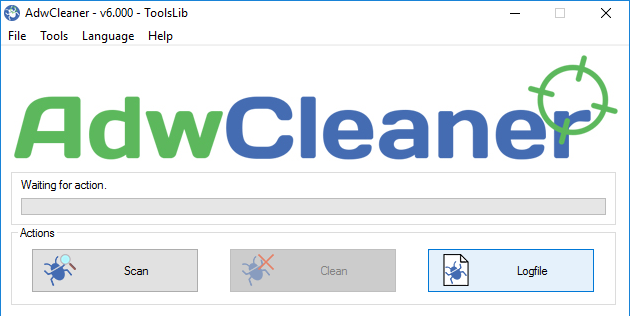
Read MoreBleepingComputer Review: AdwCleaner is a free program that searches for and deletes Adware, Toolbars, Potentially Unwanted Programs (PUP), and browser Hijackers from your computer. By using AdwCleaner you can easily remove many of these types of programs for a better user experience on your computer and while browsing the web. The types of programs that…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA