Author: nlqip
Apply appropriate updates provided by Google to vulnerable systems immediately after appropriate testing. (M1051: Update Software) Safeguard 7.1: Establish and Maintain a Vulnerability Management Process: Establish and maintain a documented vulnerability management process for enterprise assets. Review and update documentation annually, or when significant enterprise changes occur that could impact this Safeguard. Safeguard 7.4: Perform…
Read MoreMPs aren’t just getting excited about an upcoming election, but also the fruity WhatsApp messages they’re receiving, can we trust AI with our health, and who on earth is pretending to be a producer for the Drew Barrymore TV show? All this and much much more is discussed in the latest edition of the “Smashing…
Read MoreWritten by Matt Mills, President, SailPoint From smartphones to video game consoles, people love to throw around the term “next generation.” But what does it actually mean? Well, when the term is applied to a piece of technology, it usually means something that fundamentally changes the way we think about and use that technology. Blackberry…
Read MoreCollectively, these recommendations offer a roadmap for, if not averting similar cloud disasters in the future, then at least positioning CSPs and their customers to deal with these kinds of incidents in a better posture. Although each recommendation is heavily substantive and valuable, experts raise some of the more significant recommendations that CSPs should consider…
Read MoreThe latest email campaign detected by Proofpoint used an invoice-related lure written in German that was crafted to appear as if sent by Metro, a large German retailer. Dozens of organizations from various industries in Germany were targeted. The rogue emails contained a password-protected ZIP archive with the password provided in the email message. Inside,…
Read MoreThe data showed a glass ceiling effect, with almost half (48%) of women experiencing issues related to career growth, such as getting passed over for promotion, significantly more than the 26% of men who reported similar problems. Women typically hit a glass ceiling blocking them from further promotion 6-10 years into their careers. Respect The…
Read MoreOn April 9, Twitter/X began automatically modifying links that mention “twitter.com” to redirect to “x.com” instead. But over the past 48 hours, dozens of new domain names have been registered that demonstrate how this change could be used to craft convincing phishing links — such as fedetwitter[.]com, which is currently rendered as fedex.com in tweets.…
Read MoreApr 10, 2024NewsroomMobile Security / Spyware An active Android malware campaign dubbed eXotic Visit has been primarily targeting users in South Asia, particularly those in India and Pakistan, with malware distributed via dedicated websites and Google Play Store. Slovak cybersecurity firm said the activity, ongoing since November 2021, is not linked to any known threat…
Read MoreApr 10, 2024NewsroomCyber Crime / Malvertising Cybersecurity researchers have discovered a new Raspberry Robin campaign wave that propagates the malware through malicious Windows Script Files (WSFs) since March 2024. “Historically, Raspberry Robin was known to spread through removable media like USB drives, but over time its distributors have experimented with other initial infection vectors,” HP…
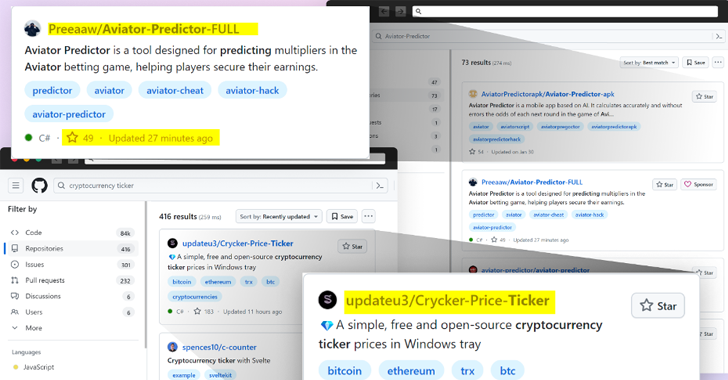
Read MoreApr 10, 2024NewsroomSoftware Security / Supply Chain Attack Threat actors are now taking advantage of GitHub’s search functionality to trick unsuspecting users looking for popular repositories into downloading spurious counterparts that serve malware. The latest assault on the open-source software supply chain involves concealing malicious code within Microsoft Visual Code project files that’s designed to…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA