Author: nlqip
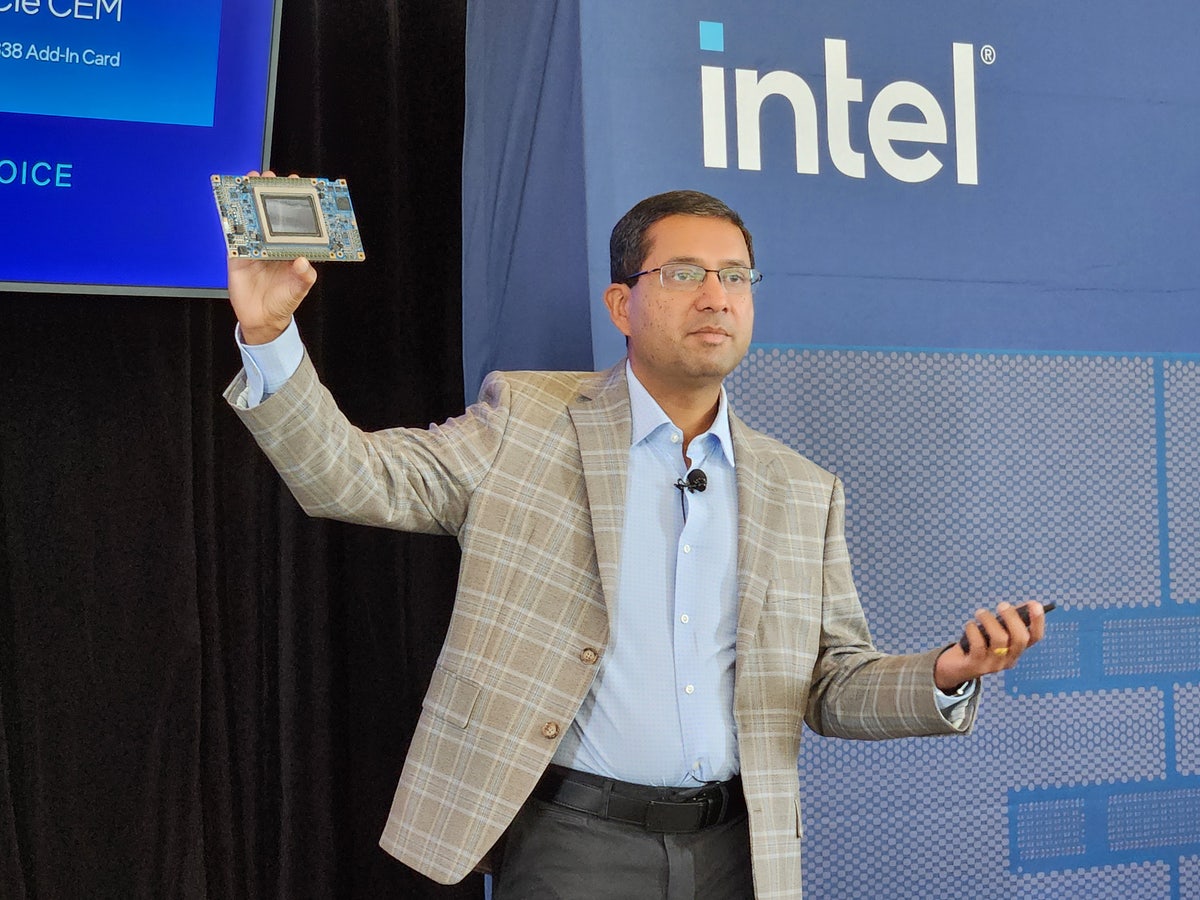
In presentations and in interviews with CRN, Intel executives elaborate on the chipmaker’s strategy to market its Gaudi 3 accelerator chips to businesses who need cost-effective AI systems backed by open ecosystems after CEO Pat Gelsinger admitted that Intel won’t be ‘competing anytime soon for high-end training’ against rivals like Nvidia. Intel said its strategy…
Read More‘This is making it easier for partners to see, if you just do this one thing, here’s where you’re eligible to earn more,’ Google VP Colleen Kapase says. Google Cloud has introduced a new “earnings hub” platform that helps partners track earned and potential incentives, with plans for Workspace and Security Operations incentives tracking “in…
Read MoreVideo, Kids Online “Hey, wanna chat?” This innocent phrase can take on a sinister meaning when it comes from an adult to a child online and even be the start of a predatory relationship 16 Oct 2024 “Hey, wanna chat?” What sounds like a casual and innocent phrase between adults can take a sinister turn…
Read MoreIn the realm of cybersecurity, the role of a SOC (Security Operations Center) analyst is pivotal in protecting organizations from ever-present digital threats. But what exactly does a cyber security SOC analyst do, and how do they respond to real-time threats? What is a SOC Analyst in Cyber Security? Before we examine how a…
Read MoreAn advanced persistent threat (APT) actor with suspected ties to India has sprung forth with a flurry of attacks against high-profile entities and strategic infrastructures in the Middle East and Africa. The activity has been attributed to a group tracked as SideWinder, which is also known as APT-C-17, Baby Elephant, Hardcore Nationalist, Leafperforator, Rattlesnake, Razor…
Read MoreAs technology adoption has shifted to be employee-led, just in time, and from any location or device, IT and security teams have found themselves contending with an ever-sprawling SaaS attack surface, much of which is often unknown or unmanaged. This greatly increases the risk of identity-based threats, and according to a recent report from CrowdStrike,…
Read MoreAccess Denied You don’t have permission to access “http://cybersecurity.att.com/blogs/security-essentials/pitfalls-of-cloud-sprawl-and-how-to-avoid-them” on this server. Reference #18.c5d7ce17.1729159385.3bfe06a https://errors.edgesuite.net/18.c5d7ce17.1729159385.3bfe06a Source link lol
Read MoreFederal prosecutors in the U.S. have charged two Sudanese brothers with running a distributed denial-of-service (DDoS) botnet for hire that conducted a record 35,000 DDoS attacks in a single year, including those that targeted Microsoft’s services in June 2023. The attacks, which were facilitated by Anonymous Sudan’s “powerful DDoS tool,” singled out critical infrastructure, corporate…
Read MoreOct 17, 2024Ravie LakshmananVulnerability / Kubernetes A critical security flaw has been disclosed in the Kubernetes Image Builder that, if successfully exploited, could be abused to gain root access under certain circumstances. The vulnerability, tracked as CVE-2024-9486 (CVSS score: 9.8), has been addressed in version 0.1.38. The project maintainers acknowledged Nicolai Rybnikar for discovering and…
Read MoreIranian hackers are breaching critical infrastructure organizations to collect credentials and network data that can be sold on cybercriminal forums to enable cyberattacks from other threat actors. Government agencies in the U.S., Canada, and Australia believe that Iranian hackers are acting as initial access brokers and use brute-force techniques to gain access to organizations in…
Read MoreRecent Posts
- Walking the Walk: How Tenable Embraces Its “Secure by Design” Pledge to CISA
- 66Degrees CEO On How Google AI Sales Grew 325 Percent
- Hackers abuse Avast anti-rootkit driver to disable defenses
- Microsoft testing Windows 11 support for third-party passkeys
- Windows 11 24H2 update blocked on PCs with Assassin’s Creed, Star Wars Outlaws