Author: nlqip
Always be wary of opening unsolicited attachments – they might harbour malware. That’s a message that is being strongly underlined once again, following the discovery of a cybercrime campaign that is using the cover of travel service providers. Security researchers at Forcepoint say that they have uncovered evidence that malicious hackers are sending out poisoned…
Read MoreThe content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. Exploring advanced AI tactics in social engineering and effective strategies for cyber defense Long-standing as a significant threat in the business world, social…
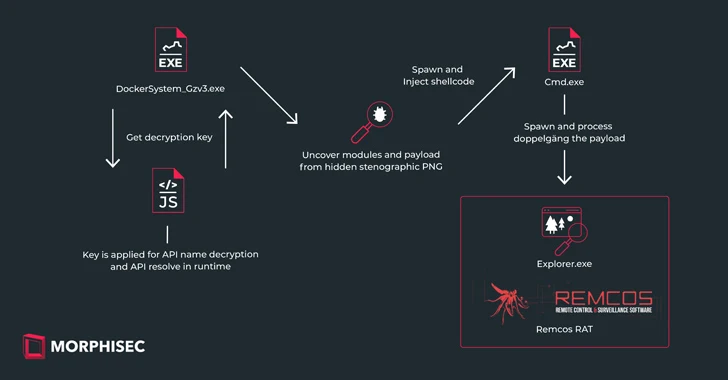
Read MoreFeb 26, 2024The Hacker NewsSteganography / Malware Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as Remcos RAT using a malware loader called IDAT Loader. The attack has been attributed to a threat actor tracked by the Computer Emergency Response Team of…
Read MoreSurprise! The LockBit ransomware group has re-emerged, just days after a high-profile law enforcement operation seized control of its infrastructure and disrupted its operations. “Operation Cronos” saw global agencies around the world work together to seize control of LockBit’s website, where information had been published about ransomware victims and their stolen data, possibly leaving many…
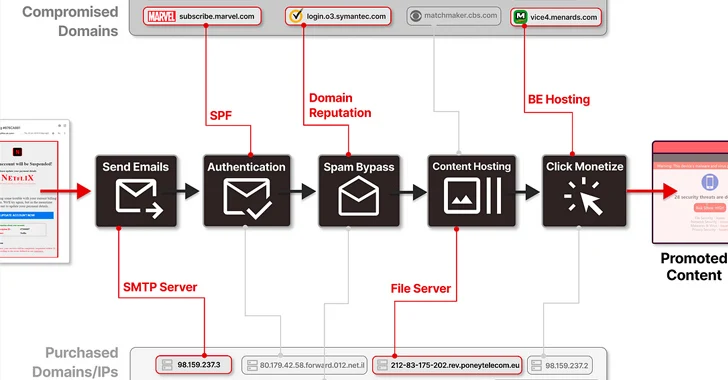
Read MoreMore than 8,000 subdomains belonging to legitimate brands and institutions have been hijacked as part of a sophisticated distribution architecture for spam proliferation and click monetization. Guardio Labs is tracking the coordinated malicious activity, which has been ongoing since at least September 2022, under the name SubdoMailing. The emails range from “counterfeit package delivery alerts…
Read MoreHow SVR-Attributed Actors are Adapting to the Move of Government and Corporations to Cloud Infrastructure OVERVIEW This advisory details recent tactics, techniques, and procedures (TTPs) of the group commonly known as APT29, also known as Midnight Blizzard, the Dukes, or Cozy Bear. The UK National Cyber Security Centre (NCSC) and international partners assess that APT29…
Read MoreFeb 26, 2024The Hacker NewsSoftware Security / Cryptocurrency A set of fake npm packages discovered on the Node.js repository has been found to share ties with North Korean state-sponsored actors, new findings from Phylum show. The packages are named execution-time-async, data-time-utils, login-time-utils, mongodb-connection-utils, and mongodb-execution-utils. One of the packages in question, execution-time-async, masquerades as its…
Read MoreCISA, NCSC-UK, and Partners Release Advisory on Russian SVR Actors Targeting Cloud Infrastructure | CISA
by nlqip
CISA, in partnership with UK National Cyber Security Centre (NCSC) and other U.S. and international partners released the joint advisory, SVR Cyber Actors Adapt Tactics for Initial Cloud Access. This advisory provides recent tactics, techniques, and procedures (TTPs) used by Russian Foreign Intelligence Service (SVR) cyber actors—also known as APT29, the Dukes, CozyBear, and NOBELIUM/Midnight…
Read MoreApple Announces Post-Quantum Encryption Algorithms for iMessage Apple announced PQ3, its post-quantum encryption standard based on the Kyber secure key-encapsulation protocol, one of the post-quantum algorithms selected by NIST in 2022. There’s a lot of detail in the Apple blog post, and more in Douglas Stabila’s security analysis. I am of two minds about this.…
Read More“I didn’t pay much attention to it, because for 5 years of swimming in money I became very lazy,” LockBitSupp said. “At 20:47 I found that the site gives a new error 404 Not Found nginx, tried to enter the server through SSH and could not, the password did not fit, as it turned out…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm