Author: nlqip
“The resulting growth of LLMs … is requiring exponential growth in high-speed connections between chips and data centers,” IBM Research engineer John Knickerbocker said. IBM Research has developed co-packaged optics, new chip assembly and packaging advancements that could increase “beachfront density” – number of optical fibers that can connect at a chip’s edge – sixfold…
Read MoreHealthcare is one of the most highly regulated industry sectors in the world. Adhering to compliance standards while also ensuring optimal patient experiences is a challenge. DSPM capabilities in Tenable Cloud Security can ease the burden on cybersecurity teams. When it comes to cybersecurity, the healthcare sector can find itself stuck between a rock and…
Read MoreTenable Security Center Delivers Focused Vulnerability Prioritization to Close Critical Exposures that Increase Business Risk
by nlqip
Tenable®, the exposure management company, today announced new vulnerability intelligence, risk prioritization and web application scanning features for Tenable Security Center, the world’s #1 vulnerability management solution managed on-premises. Tenable Security Center identifies, investigates and prioritizes vulnerabilities, providing customers with a risk-based view of their security and compliance posture for their on-premises environments. Equipped with…
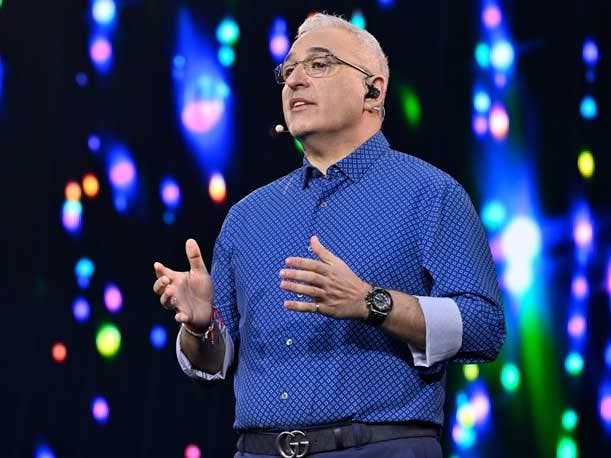
Read MoreCEO Antonio Neri On HPE’s Supercomputing Advantage Over AWS, ‘Huge’ VM Essentials Opportunity And “Super Strong’ Results
by nlqip
Hewlett Packard Enterprise CEO Antonio Neri says he does not see traditional supercomputing workloads moving to AWS’ just-announced UltraCluster AI supercomputer. Hewlett Packard Enterprise CEO Antonio Neri said he does not see traditional supercomputing workloads moving to Amazon Web Services’ just-announced UltraCluster AI supercomputer. “I don’t see anytime soon the traditional supercomputing workloads moving there…
Read MoreCybersecurity Snapshot: Study Raises Open Source Security Red Flags, as Cyber Agencies Offer Prevention Tips Against Telecom Spying Attacks
by nlqip
Don’t miss the Linux Foundation’s deep dive into open source software security. Plus, cyber agencies warn about China-backed cyber espionage campaign targeting telecom data. Meanwhile, a study shows the weight of security considerations in generative AI projects. And get the latest on ransomware trends, financial cybercrime and critical infrastructure security. Dive into six things that…
Read MoreDell Technologies now says it offers AI data readiness with Dell Data Lakehouse, the densest GPU-capacity inside liquid-cooled racks and an AI model-buffing Agentic RAG with Nvidia. Dell Technologies says its AI advances in servers offer customers the densest GPU capacity available for Nvidia’s most sophisticated processors running in liquid-cooled cabinets that, all together, push…
Read MoreTry Tenable Web App Scanning Enjoy full access to our latest web application scanning offering designed for modern applications as part of the Tenable One Exposure Management platform. Safely scan your entire online portfolio for vulnerabilities with a high degree of accuracy without heavy manual effort or disruption to critical web applications. Sign up now.…
Read MoreAT&T, Verizon, CrowdStrike and Microsoft are among the companies that experienced major cloud service outages during the last year. A February AT&T outage that received attention by federal regulators. Issues in September for Verizon customers. And a certain cybersecurity vendor’s update that crashed Windows machines worldwide. These are among the biggest cloud service outages the…
Read MoreAs Intel’s board of directors searches for a new permanent leader and pushes for better execution of its strategy after CEO Pat Gelsinger’s abrupt exit on Sunday, the beleaguered chipmaker adds two veteran semiconductor leaders to its board. Intel said it has added two veteran semiconductor executives to its board of directors: former ASML CEO…
Read MoreToday, the Cybersecurity and Infrastructure Security Agency (CISA) released an updated public version of the Continuous Diagnostics and Mitigation (CDM) Data Model Document. Version 5.0.1 aligns with fiscal year 2023 Federal Information Security Modernization Act (FISMA) metrics. The CDM Data Model Document provides a comprehensive description of a common data schema to ensure that prescribed…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA