Category: AI in news
The world-renowned auction house Christie’s has confirmed that it has fallen victim to a ransomware attack, seemingly orchestrated by a Russia-linked cybercriminal gang. Two weeks ago the CEO of the world’s wealthiest auction house posted on LinkedIn blamed a “technology security incident” after the Christie’s website went unexpectedly offline. Meanwhile, two employees of Christie’s told…
Read MoreMay 29, 2024NewsroomEnterprise Security / Vulnerability Check Point is warning of a zero-day vulnerability in its Network Security gateway products that threat actors have exploited in the wild. Tracked as CVE-2024-24919, the issue impacts CloudGuard Network, Quantum Maestro, Quantum Scalable Chassis, Quantum Security Gateways, and Quantum Spark appliances. “The vulnerability potentially allows an attacker to…
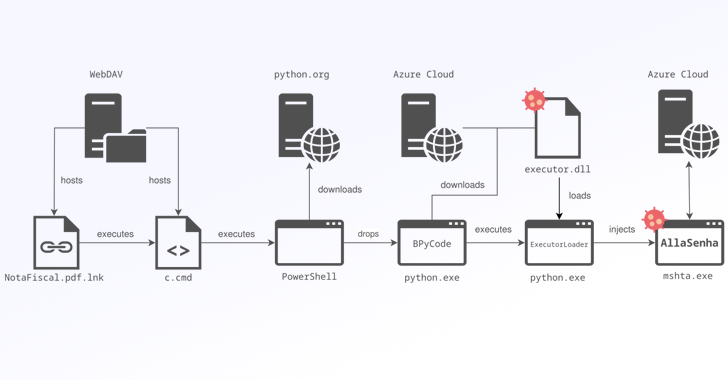
Read MoreBrazilian banking institutions are the target of a new campaign that distributes a custom variant of the Windows-based AllaKore remote access trojan (RAT) called AllaSenha. The malware is “specifically aimed at stealing credentials that are required to access Brazilian bank accounts, [and] leverages Azure cloud as command-and-control (C2) infrastructure,” French cybersecurity company HarfangLab said in…
Read More‘When we look at what’s in our pipeline, it is increasingly filled with newer technologies. That tells us that those newer offerings, whether they’re around cloud, around AI, around quantum, around digital workplace, are really getting the buyers’ attention,’ says Unisys’ Chairman and CEO Peter Altabef. While global IT solution provider Unisys can trace its…
Read MoreThe digital trust measurement gap Understanding and measuring digital trust can directly link digital trust to top line revenue, market share, and other indicators, ISACA found. But not all organizations are keeping track of digital trust. Of those measuring it, 94% agreed digital trust it’s extremely or very important to their organization, yet only 23%…
Read MoreThe user clicks a “log in with WhatsApp” button on a website or scans a QR code, which results in a code appearing in WhatsApp. The user hits “send” on this message as if it’s from them and they are automatically logged in to the site. This works as a basic form of MFA because…
Read MoreCustomer AI spending, Data Cloud traction and MuleSoft progress are expected to come up. A pulse on customer spending on artificial intelligence. Traction in Data Cloud and Einstein 1. And continuing progress in MuleSoft. These are some of the major topics expected to come up Wednesday during Salesforce’s earnings call for its first fiscal quarter,…
Read MoreMay 29, 2024NewsroomCybercrime / Cybersecurity The U.S. Department of Justice (DoJ) has sentenced a 31-year-old to 10 years in prison for laundering more than $4.5 million through business email compromise (BEC) schemes and romance scams. Malachi Mullings, 31, of Sandy Springs, Georgia pleaded guilty to the money laundering offenses in January 2023. According to court…
Read More“Relying on these customers notifications and Check Point’s analysis, the teams found within 24 hours a few potential customers which were subject to similar attempts,” Check Point added. The affected Check Point environments include CloudGuard Network, Quantum Maestro, Quantum Scalable Chassis, Quantum Security Gateways, and Quantum Spark Appliances. Security Gateway Hotfix To fix the vulnerable…
Read MorePrivacy Implications of Tracking Wireless Access Points Brian Krebs reports on research into geolocating routers: Apple and the satellite-based broadband service Starlink each recently took steps to address new research into the potential security and privacy implications of how their services geolocate devices. Researchers from the University of Maryland say they relied on publicly available…
Read MoreRecent Posts
- Fake AI video generators infect Windows, macOS with infostealers
- T-Mobile confirms it was hacked in recent wave of telecom breaches
- GitHub projects targeted with malicious commits to frame researcher
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’