Category: AI in news
Although 55% of organizations are currently piloting or using a generative AI (GenAI) solution, securely deploying the technology remains a significant focus for cyber leaders. A recent ISMG poll of business and cybersecurity professionals revealed that some of the top concerns around GenAI implementation include data security or leakage of sensitive data, privacy, hallucinations, misuse…
Read MoreFCC Fines Major U.S. Wireless Carriers for Selling Customer Location Data – Krebs on Security
by nlqip
The U.S. Federal Communications Commission (FCC) today levied fines totaling nearly $200 million against the four major carriers — including AT&T, Sprint, T-Mobile and Verizon — for illegally sharing access to customers’ location information without consent. The fines mark the culmination of a more than four-year investigation into the actions of the major carriers. In…
Read MoreApr 29, 2024NewsroomMobile Security / Hacking Google on Monday revealed that almost 200,000 app submissions to its Play Store for Android were either rejected or remediated to address issues with access to sensitive data such as location or SMS messages over the past year. The tech giant also said it blocked 333,000 bad accounts from…
Read MoreMarriott admits it falsely claimed for five years it was using encryption during 2018 breach
by nlqip
Douglas Brush, a special master with the US federal courts and the chief visionary officer for Accel Consulting who is not working on the Marriott case, said this twist from Marriott has potentially serious implications for the enterprise. Beyond Marriott, it illustrates some of the dangers associated with any false claims in a breach case.…
Read MoreWhen an organization’s assets span multiple public – and private – clouds, it can be exceedingly difficult to achieve consistency with how workloads are deployed and managed and how policies are enforced in different clouds. For example, each cloud may have different concepts and configurations governing its separate identity and access management (IAM) frameworks. There…
Read MoreApr 29, 2024NewsroomProgramming / Supply Chain A security vulnerability has been discovered in the R programming language that could be exploited by a threat actor to create a malicious RDS (R Data Serialization) file such that it results in code execution when loaded and referenced. The flaw, assigned the CVE identifier CVE-2024-27322, “involves the use…
Read More“UK-developed products and services [will] become less appealing, because adopters will fear that they have been designed for Government access, and the UK will become a more appealing target for criminals and hostile nation states,” the groups warned. Encryption backdoors The revised law could have serious repercussions to UK tech innovation, potentially driving tech talent…
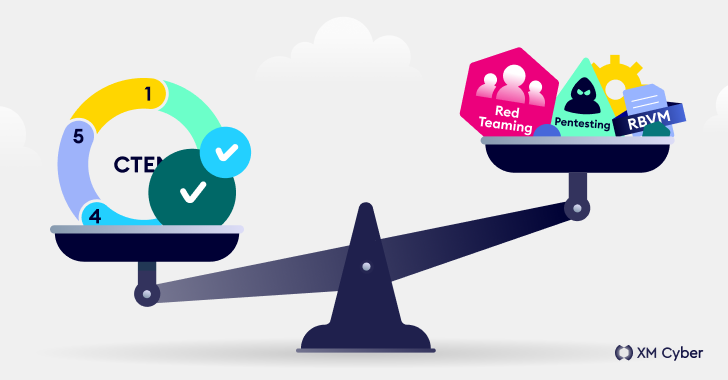
Read MoreNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
by nlqip
It comes as no surprise that today’s cyber threats are orders of magnitude more complex than those of the past. And the ever-evolving tactics that attackers use demand the adoption of better, more holistic and consolidated ways to meet this non-stop challenge. Security teams constantly look for ways to reduce risk while improving security posture,…
Read MoreWhale Song Code During the Cold War, the US Navy tried to make a secret code out of whale song. The basic plan was to develop coded messages from recordings of whales, dolphins, sea lions, and seals. The submarine would broadcast the noises and a computer—the Combo Signal Recognizer (CSR)—would detect the specific patterns and…
Read MoreApr 29, 2024NewsroomSandbox / Vulnerability Multiple critical security flaws have been disclosed in the Judge0 open-source online code execution system that could be exploited to obtain code execution on the target system. The three flaws, all critical in nature, allow an “adversary with sufficient access to perform a sandbox escape and obtain root permissions on…
Read MoreRecent Posts
- Palo Alto Networks patches two firewall zero-days used in attacks
- Vulnerability Summary for the Week of November 11, 2024 | CISA
- US space tech giant Maxar discloses employee data breach
- CISA Adds Two Known Exploited Vulnerabilities to Catalog | CISA
- CISA Adds Three Known Exploited Vulnerabilities to Catalog | CISA