Category: AI in news
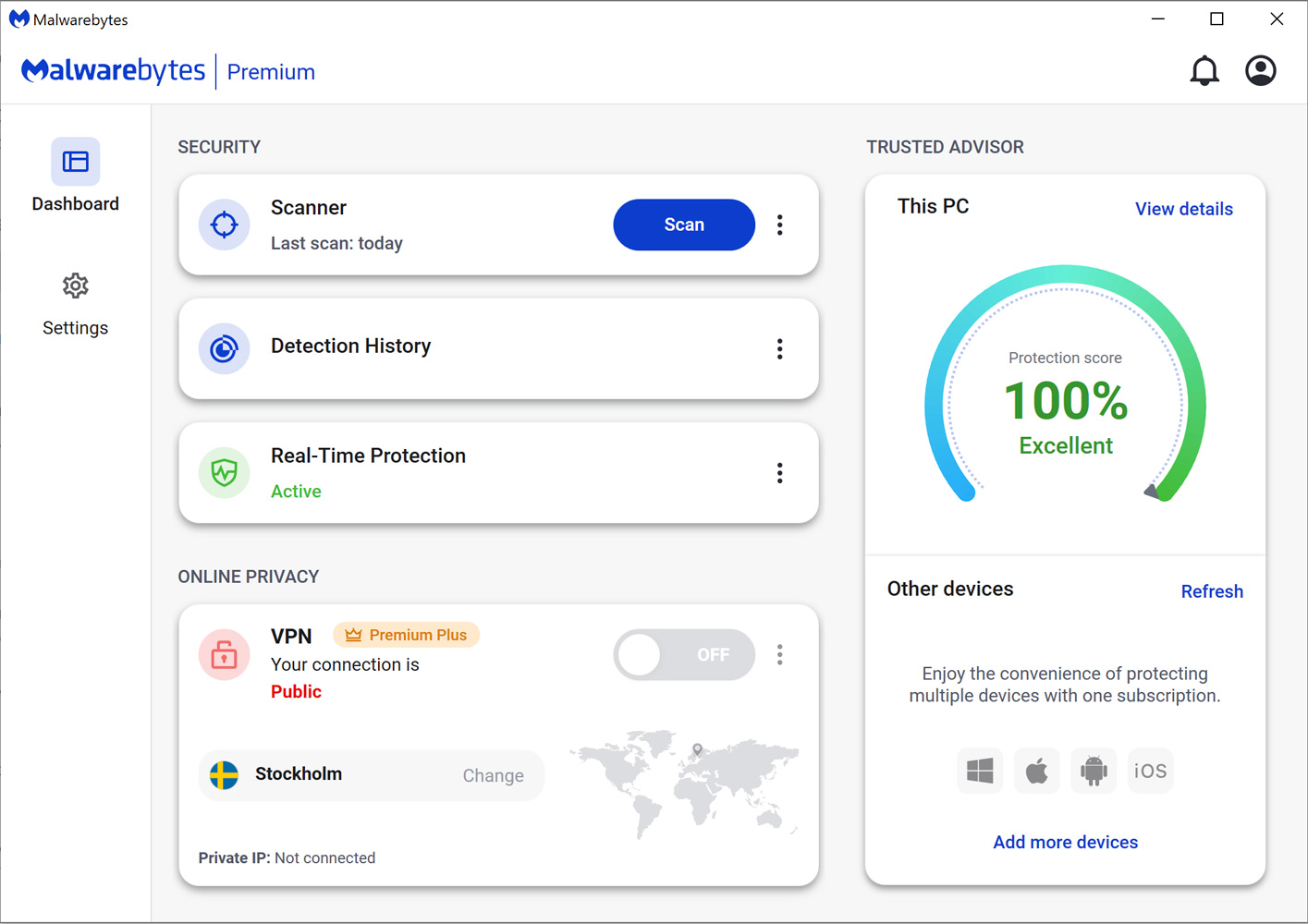
BleepingComputer Review: Malwarebytes is an important security program to protect any user’s computer. It is light-weight, fast, and best of all, excellent at removing the latest infections that may be in the wild. Malwarebytes is updated numerous times throughout the day, which allows you to stay protected from threats as they come out. One of…
Read MoreWomen’s History Month: N-able’s Stefanie Hammond On Saying Yes, Staying Put And Being More Direct
by nlqip
‘I think I probably have one of the best jobs in the entire industry, and that’s pretty cool,’ said Stefanie Hammond, head nerd at N-able. Stefanie Hammond’s secret to success is to say “yes” more often. Hammond, head nerd at Burlington, Mass.-based vendor N-able and named to the CRN 2024 Channel Chief list, has been…
Read MoreTenable and Thales Collaborate to Provide Cyber Defense Simulations to Better Secure Operational Technology Environments
by nlqip
The heart of the Welsh Valleys is home to the Thales Ebbw Vale campus, a world-class facility jointly funded by the Welsh government as part of its regeneration program for the region. At the core of the facility is the Cyber Range, a simulation and virtualization platform for training, testing, exercising and R&D. Tenable has…
Read MoreUpgraded Pegasystems Channel Program Emphasizes Partner Skills, Drops Sales Volume Requirements | CRN
by nlqip
Partner competencies and specializes, combined with “delivery excellence” and customer bookings and references, are the benchmarks by which Pegasystem partners will be assessed under the Pega Partner program framework. Pegasystems is launching an update of its channel program today, putting more emphasis on partner skills and success, offering more vertical industry specializations, and eliminating sales…
Read MoreIntroduction With artificial intelligence (AI) use growing in the enterprise, Chief Information Security Officers play a critical role in its implementation and adoption. CISOs need to prepare for the risks associated with AI content creation as well as AI-assisted security threats from attackers. By following some key best practices, we’ll be better prepared to safely…
Read MoreThis Assurance Report Card (ARC) pulls together several of the key grouping based on assets type and risk levels to help the CISO understand the current state of the Vulnerability Management program. The National Banking and Securities Commission (CNBV) Annex 72 is a collection of 30 Key Risk Indicators (KRI) that establish compliance standards for…
Read More“We’re responsibly investing in our company’s biggest priorities and the significant opportunities ahead,” a Google spokesperson said in an email. Google reportedly continues to conduct layoffs, this time letting go of employees in its finance and real estate units – but the company continues to invest in geographic growth hubs in Ireland, the U.S. and…
Read MoreThe executives tell CRN that AI-powered tools are making an impact on their day-to-day management of IT for customers. For MSPs on the front lines of managing IT systems for customers, tools for generative AI and other AI-powered capabilities are making an impact on their day-to-day operations. That’s the message that MSP executives shared with…
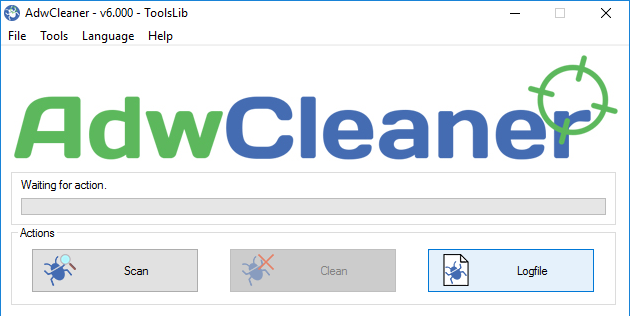
Read MoreBleepingComputer Review: AdwCleaner is a free program that searches for and deletes Adware, Toolbars, Potentially Unwanted Programs (PUP), and browser Hijackers from your computer. By using AdwCleaner you can easily remove many of these types of programs for a better user experience on your computer and while browsing the web. The types of programs that…
Read More‘Together with LeanIX, we want to offer a first-of-its-kind transformation suite to provide holistic support to our customers on their business transformation journeys,’ said SAP CEO Christian Klein. SAP is buying management software specialist LeanIX in a move to embed generative AI into products and create a new transformation solution suite. “Systems and processes go…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm