Category: AI in news
In today’s world, where information spreads at lightning speed, it’s easy to fall into the trap of misinformation. Amidst the noise, Google Fact Checking Tools aim to empower you with the ability to distinguish reliable sources from those perpetuating false claims. What are Google Fact Checking Tools? Google offers a suite of tools designed to…
Read MoreArtificial intelligence (AI) is rapidly transforming various industries, and the world of literature is no exception. AI-powered writing assistants are becoming increasingly sophisticated, blurring the lines between human and machine-generated content. This begs the question: can AI write a book in its entirety, and if so, what are the implications for the future of authorship?…
Read MoreApr 15, 2024NewsroomFirmware Security / Vulnerability A security flaw impacting the Lighttpd web server used in baseboard management controllers (BMCs) has remained unpatched by device vendors like Intel and Lenovo, new findings from Binarly reveal. While the original shortcoming was discovered and patched by the Lighttpd maintainers way back in August 2018 with version 1.4.51,…
Read MoreThe U.S. government is warning that smart locks securing entry to an estimated 50,000 dwellings nationwide contain hard-coded credentials that can be used to remotely open any of the locks. The lock’s maker Chirp Systems remains unresponsive, even though it was first notified about the critical weakness in March 2021. Meanwhile, Chirp’s parent company, RealPage,…
Read MoreImagine a world where the software that powers your favorite apps, secures your online transactions, and keeps your digital life could be outsmarted and taken over by a cleverly disguised piece of code. This isn’t a plot from the latest cyber-thriller; it’s actually been a reality for years now. How this will change – in…
Read MoreOn April 12th, to make it easy for users to check if their information was hacked, breach tracking service HaveIBeenPwned added the leaked database to its website. The incident contributed a total of 2,842,669 breached records to the HIBP database, of which the service noted that 46% were duplicates already present in its records. As…
Read MoreNew Lattice Cryptanalytic Technique A new paper presents a polynomial-time quantum algorithm for solving certain hard lattice problems. This could be a big deal for post-quantum cryptographic algorithms, since many of them base their security on hard lattice problems. A few things to note. One, this paper has not yet been peer reviewed. As this…
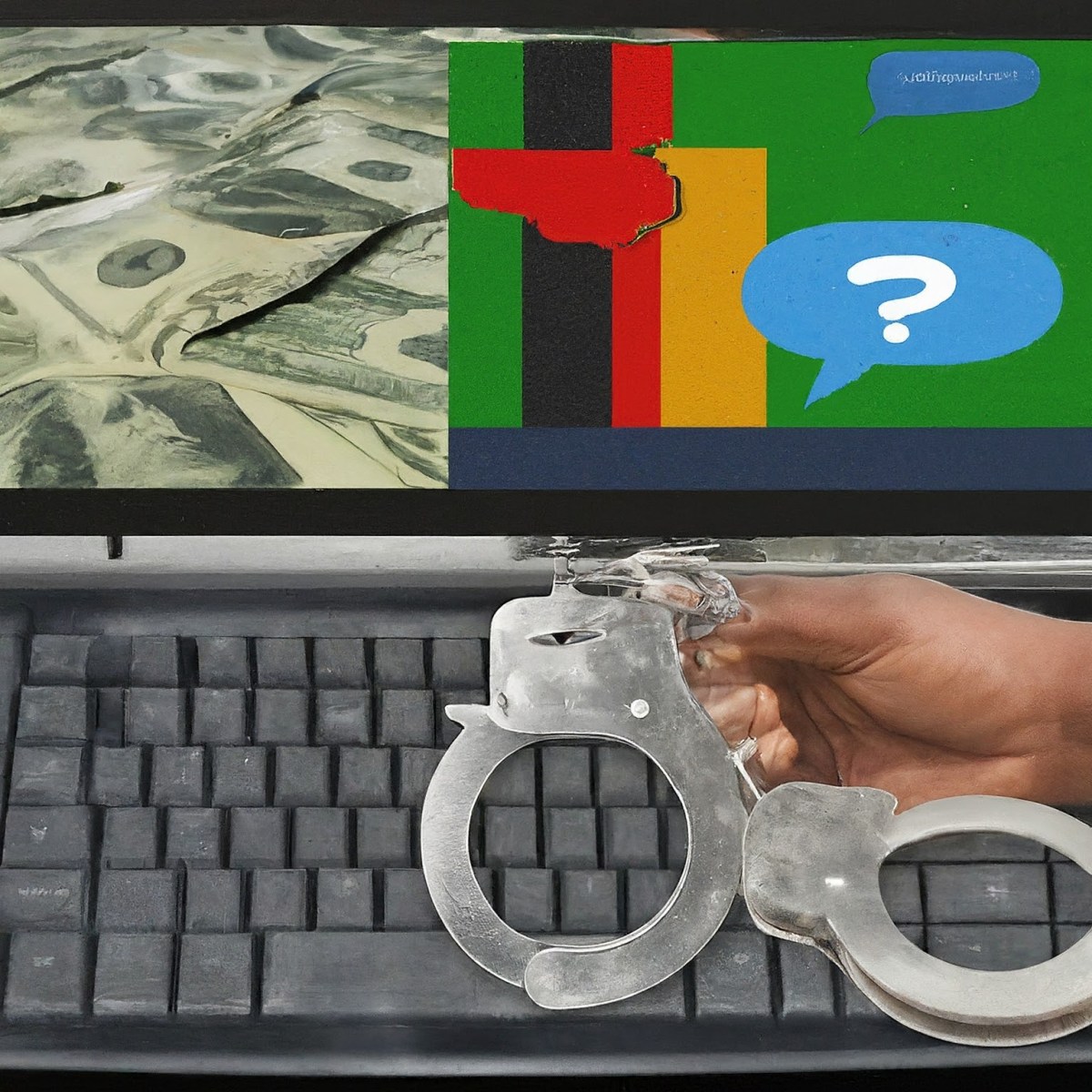
Read MoreLaw enforcement officers in Zambia have arrested 77 people at a call centre company they allege had employed local school-leavers to engage in scam internet users around the world. According to Zambian authorities, Chinese-run Golden Top Support Services, based in an upmarket area of capital city Lusaka, recruited Zambian youths between the ages of 20-25,…
Read MoreApr 15, 2024NewsroomSpyware / Mobile Security Cybersecurity researchers have discovered a “renewed” cyber espionage campaign targeting users in South Asia with the aim of delivering an Apple iOS spyware implant called LightSpy. “The latest iteration of LightSpy, dubbed ‘F_Warehouse,’ boasts a modular framework with extensive spying features,” the BlackBerry Threat Research and Intelligence Team said…
Read Moreffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt ffrt…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm