Category: AI in news
The need for reliable intelligence is pressing in threat hunting and emerging AI technologies can fulfill that to a good extent, according to a Censys study. The study included US and Europe-based organizations across industries and noted that current threat-hunting practices are “as much an art as science” and can use a discipline of common,…
Read MoreAutomakers Are Sharing Driver Data with Insurers without Consent Kasmir Hill has the story: Modern cars are internet-enabled, allowing access to services like navigation, roadside assistance and car apps that drivers can connect to their vehicles to locate them or unlock them remotely. In recent years, automakers, including G.M., Honda, Kia and Hyundai, have started…
Read MoreBeing a CISO is a balancing act: ensuring organizations are secure without compromising users’ productivity. This requires taking multiple elements into consideration, like cost, complexity, performance and user experience. CISOs around the globe use Cato SSE 360, as part of the Cato SASE Cloud platform to balance these factors without compromise. This article details how…
Read MoreMar 14, 2024NewsroomCyber Threat / Malware The threat actor known as Blind Eagle has been observed using a loader malware called Ande Loader to deliver remote access trojans (RATs) like Remcos RAT and NjRAT. The attacks, which take the form of phishing emails, targeted Spanish-speaking users in the manufacturing industry based in North America, eSentire…
Read MoreIn addition to having an inventory of existing tools in use, there also should be a process to onboard and offboard future tools and services from the organizational inventory securely. AI security and privacy training It’s often quipped that “humans are the weakest link,” however that doesn’t need to be the case if an organization…
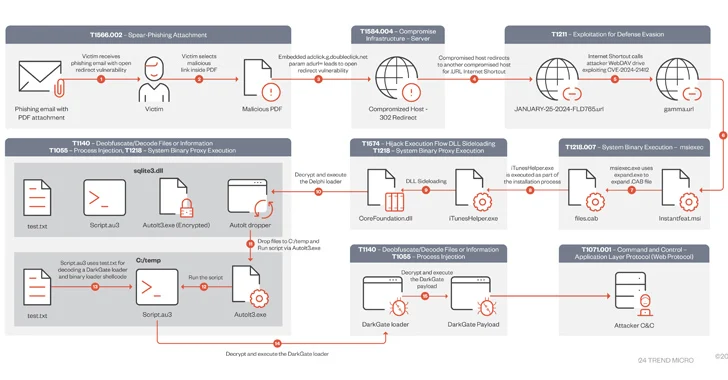
Read MoreMar 14, 2024NewsroomMalware / Cyber Attack A DarkGate malware campaign observed in mid-January 2024 leveraged a recently patched security flaw in Microsoft Windows as a zero-day using bogus software installers. “During this campaign, users were lured using PDFs that contained Google DoubleClick Digital Marketing (DDM) open redirects that led unsuspecting victims to compromised sites hosting…
Read MoreSmashing Security podcast #363: Stuck streaming sticks, TikTok conspiracies, and spying cars
by nlqip
Roku users are revolting after their TVs are bricked by the company, we learn how to make money through conspiracy videos on TikTok, and just how much is your car snooping on your driving? All this and much much more is discussed in the latest edition of the “Smashing Security” podcast by cybersecurity veterans Graham…
Read MoreAre you part of an organization that has made significant strides in the realm of cybersecurity? Do you believe your security projects and initiatives have demonstrated outstanding business value and thought leadership? If so, now is the time to showcase your achievements and gain recognition among your peers. The CSO50 Conference + Awards, scheduled for…
Read More“PowerShell allows users to evaluate values inside strings before they are used,” the researcher explained. “This can be done by adding $(<experssion_to_be_evaluated>) to your string […]. Any PowerShell command can be inserted between the parentheses and will be evaluated — such as $(Start-Process cmd), $(Invoke-Expression exp), and other PowerShell treats.” So, for example, if an…
Read MoreIntroducing Microsoft Copilot for Security The marriage of generative AI with proven security solutions can augment the work of security professionals by accelerating processing speeds and pattern detection to help gain an edge over cybercriminals. Sponsored by Microsoft Source link ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde ddde…
Read MoreRecent Posts
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm
- Seven Trends to Watch for in 2025
- Multiple Vulnerabilities in Ivanti Products Could Allow for Remote Code Execution
- Ivanti Releases Security Updates for Connect Secure, Policy Secure, and ZTA Gateways | CISA
- CISA Adds One Vulnerability to the KEV Catalog | CISA