Category: AI in news
Aug 20, 2024Ravie LakshmananVulnerability / Threat Intelligence A previously undocumented backdoor named Msupedge has been put to use against a cyber attack targeting an unnamed university in Taiwan. “The most notable feature of this backdoor is that it communicates with a command-and-control (C&C) server via DNS traffic,” the Symantec Threat Hunter Team, part of Broadcom,…
Read MoreSamantha Mabey, director of digital security solutions at Entrust, commented: “Now that NIST has finalized three quantum-resistant security algorithms, it becomes increasingly crucial for CISOs to prepare for the quantum computing era. The shift to post-quantum cryptography is more than a technical update; it’s a vital step in protecting sensitive information, and promises to be…
Read MoreAug 20, 2024Ravie LakshmananMalware / Cyber Espionage Cybersecurity researchers have shed light on a threat actor known as Blind Eagle that has persistently targeted entities and individuals in Colombia, Ecuador, Chile, Panama, and other Latin American nations. Targets of these attacks span several sectors, including governmental institutions, financial companies, energy and oil and gas companies.…
Read MoreMoreover, there are no safeguards at the repository level to detect bad packages. “Anyone can write a piece of code and just upload it to those platforms,” Yehuda Gelb, research engineer at Checkmarx, tells CSO. “For instance, in Python, you can just create a Python package and upload it, and there’s no one really in…
Read MoreAug 20, 2024Ravie LakshmananVulnerability / Ransomware The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security flaw impacting Jenkins to its Known Exploited Vulnerabilities (KEV) catalog, following its exploitation in ransomware attacks. The vulnerability, tracked as CVE-2024-23897 (CVSS score: 9.8), is a path traversal flaw that could lead to code execution. “Jenkins…
Read MoreNew details are emerging about a breach at National Public Data (NPD), a consumer data broker that recently spilled hundreds of millions of Americans’ Social Security Numbers, addresses, and phone numbers online. KrebsOnSecurity has learned that another NPD data broker which shares access to the same consumer records inadvertently published the passwords to its back-end…
Read MoreAug 19, 2024Ravie LakshmananThreat Intelligence / Cryptocurrency A new type of malware called UULoader is being used by threat actors to deliver next-stage payloads like Gh0st RAT and Mimikatz. The Cyberint Research Team, which discovered the malware, said it’s distributed in the form of malicious installers for legitimate applications targeting Korean and Chinese speakers. There…
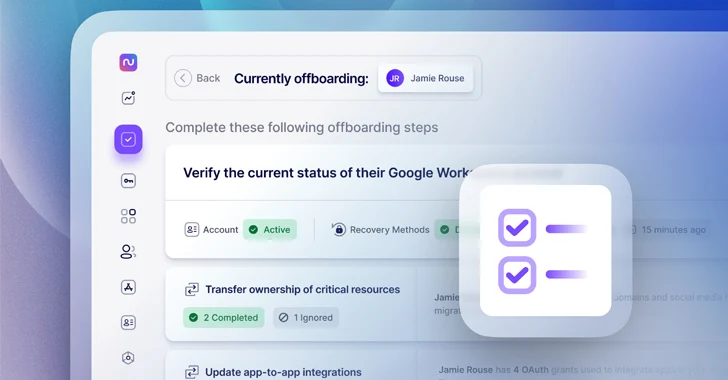
Read MoreAccording to recent research on employee offboarding, 70% of IT professionals say they’ve experienced the negative effects of incomplete IT offboarding, whether in the form of a security incident tied to an account that wasn’t deprovisioned, a surprise bill for resources that aren’t in use anymore, or a missed handoff of a critical resource or…
Read MoreThe State of Ransomware Palo Alto Networks published its semi-annual report on ransomware. From the Executive Summary: Unit 42 monitors ransomware and extortion leak sites closely to keep tabs on threat activity. We reviewed compromise announcements from 53 dedicated leak sites in the first half of 2024 and found 1,762 new posts. This averages to…
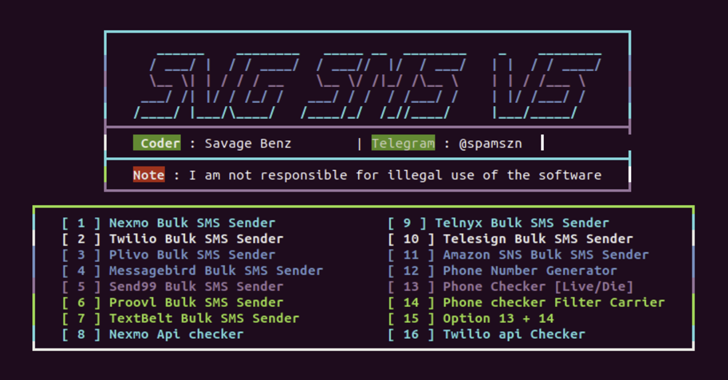
Read MoreAug 19, 2024Ravie LakshmananCloud Security / Threat Intelligence Malicious actors are using a cloud attack tool named Xeon Sender to conduct SMS phishing and spam campaigns on a large scale by abusing legitimate services. “Attackers can use Xeon to send messages through multiple software-as-a-service (SaaS) providers using valid credentials for the service providers,” SentinelOne security…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA