Category: AI in news
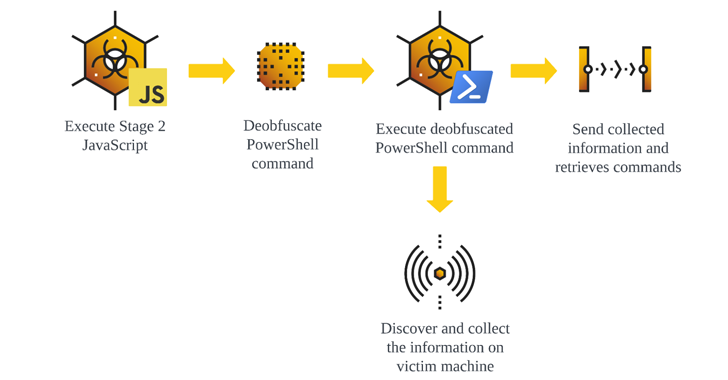
Jul 05, 2024NewsroomSEO Poisoning / Cyber Attack, The malware known as GootLoader continues to be in active use by threat actors looking to deliver additional payloads to compromised hosts. “Updates to the GootLoader payload have resulted in several versions of GootLoader, with GootLoader 3 currently in active use,” cybersecurity firm Cybereason said in an analysis…
Read MoreWhat does a logic bomb attack do? As the Stuxnet example demonstrates, a logic bomb attack gets its name because the malicious code activates when some logical condition, or trigger, is satisfied: It can be explained as an if-then statement. There are two forms a logic bomb’s trigger can take: positive or negative. A positive trigger goes off if something happens, whereas…
Read MoreJul 05, 2024NewsroomSupply Chain Attack / Malware The supply chain attack targeting widely-used Polyfill[.]io JavaScript library is wider in scope than previously thought, with new findings from Censys showing that over 380,000 hosts are embedding a polyfill script linking to the malicious domain as of July 2, 2024. This includes references to “https://cdn.polyfill[.]io” or “https://cdn.polyfill[.]com”…
Read MoreJul 05, 2024NewsroomNetwork Security / Cyber Attack Cybersecurity researchers have uncovered a new botnet called Zergeca that’s capable of conducting distributed denial-of-service (DDoS) attacks. Written in Golang, the botnet is so named for its reference to a string named “ootheca” present in the command-and-control (C2) servers (“ootheca[.]pw” and “ootheca[.]top”). “Functionally, Zergeca is not just a…
Read MoreWhat’s happening? Security researchers have warned that a new ransomware group has taken an unusual twist on the traditional method of extorting money from its corporate victims. So what’s different this time? Whereas many ransomware attacks see a company’s company’s data exfiltrated by attackers, and the threat made that stolen data will be sold to…
Read MoreSince September 2021, Europol’s European Cybercrime Centre (EC3) assisted the operation with analytical and forensic support and enabled information exchange among all partners. Additionally, law enforcement operated a “malware information sharing platform,” inviting private partners to add real-time threat intelligence to the effort. “Over the span of the whole investigation, over 730 pieces of threat…
Read MoreSegment 2: Area hospitals are crowded with people reporting breathing difficulties, and public health officials are encouraging people all over the city to “shelter in place” as a precaution. Headquarters is currently upwind of the explosion. The company needs to decide what to tell its employees to do but isn’t sure whether it has the legal…
Read MoreJul 04, 2024NewsroomArtificial Intelligence / Data Privacy Brazil’s data protection authority, Autoridade Nacional de Proteção de Dados (ANPD), has temporarily banned Meta from processing users’ personal data to train the company’s artificial intelligence (AI) algorithms. The ANPD said it found “evidence of processing of personal data based on inadequate legal hypothesis, lack of transparency, limitation…
Read MoreWhat CISOs should do now Kaspersky claims 270,000 corporate clients, although, to be clear, that counts every customer in the world. While many of its previous customers have already migrated to other security products, those in the US that are still using their software need to make plans now. “Don’t wait until October, the last…
Read MoreA coordinated law enforcement operation codenamed MORPHEUS has felled close to 600 servers that were used by cybercriminal groups and were part of an attack infrastructure associated with the Cobalt Strike. The crackdown targeted older, unlicensed versions of the Cobalt Strike red teaming framework between June 24 and 28, according to Europol. Of the 690…
Read MoreRecent Posts
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’
- Botnet exploits GeoVision zero-day to install Mirai malware
- FTC reports 50% drop in unwanted call complaints since 2021
- Bitfinex hacker gets 5 years in prison for 120,000 bitcoin heist
- Here Are The Stellar Startup Edge Computing/IoT Vendors To Know In 2024


![Polyfill[.]io Attack Impacts Over 380,000 Hosts, Including Major Companies](https://kartwheelnewz.info/wp-content/uploads/2024/07/Polyfillio-Attack-Impacts-Over-380000-Hosts-Including-Major-Companies.png)