Category: AI in news
Security and Human Behavior (SHB) 2024 This week, I hosted the seventeenth Workshop on Security and Human Behavior at the Harvard Kennedy School. This is the first workshop since our co-founder, Ross Anderson, died unexpectedly. SHB is a small, annual, invitational workshop of people studying various aspects of the human side of security. The fifty…
Read More“SORBS has a long and somewhat checkered history. It was created in the early 2000s, with a DNSBL (Domain Name System-based Blackhole List) version coming online in January 2002,” Chandler wrote. “The closure of SORBS does not mark any real turning point in the email security landscape. Although it was one of the oldest DNSBL…
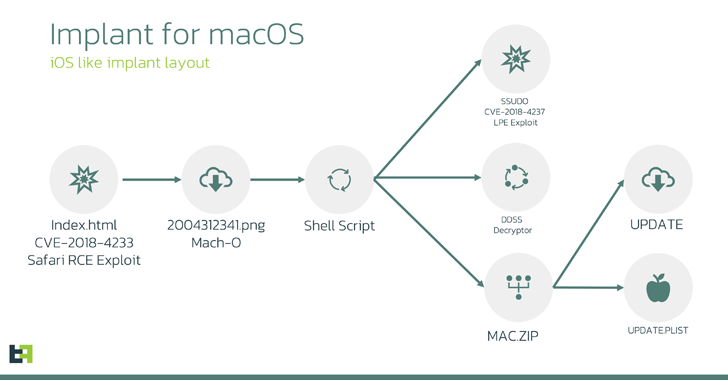
Read MoreCybersecurity researchers have disclosed that the LightSpy spyware allegedly targeting Apple iOS users is in fact a previously undocumented macOS variant of the implant. The findings come from both Huntress Labs and ThreatFabric, which separately analyzed the artifacts associated with the cross-platform malware framework that likely possesses capabilities to infect Android, iOS, Windows, macOS, Linux,…
Read MoreThe two malware programs are so similar that it’s hard to tell their code apart, the Symantec researchers said, noting that the only differences are an added sleep command to RansomHub’s variant and the commands that are available to execute through the Windows command line shell cmd.exe. However, these commands are configurable in the malware…
Read More16-year-old arrested in France in connection with high-profile Epsilon hacking group attacks
by nlqip
A 16-year-old youth has been arrested in France on suspicion of having run a malware-for-rent business. The unnamed Frenchman, who goes by online handles including “ChatNoir” and “Casquette”, is said to be a key member of the Epsilon hacking group, which has in the recent past stolen millions of records from the likes of French…
Read MoreCybersecurity Snapshot: NIST Program Assesses How AI Systems Will Behave in the Real World, While FBI Has Troves of Decryption Keys for LockBit Victims
by nlqip
Check out the new ARIA program from NIST, designed to evaluate if an AI system will be safe and fair once it’s launched. Plus, the FBI offers to help LockBit victims with thousands of decryption keys. In addition, Deloitte finds that boosting cybersecurity is key for generative AI deployment success. And why identity security is…
Read MoreJun 07, 2024The Hacker NewsSoftware Supply Chain / Myrror Security Traditional SCAs Are Broken: Did You Know You Are Missing Critical Pieces? Application Security professionals face enormous challenges securing their software supply chains, racing against time to beat the attacker to the mark. Software Composition Analysis (SCA) tools have become a basic instrument in the…
Read MoreThe Justice Department Took Down the 911 S5 Botnet The US Justice Department has dismantled an enormous botnet: According to an indictment unsealed on May 24, from 2014 through July 2022, Wang and others are alleged to have created and disseminated malware to compromise and amass a network of millions of residential Windows computers worldwide.…
Read MoreWhat is whitelisting? Whitelisting is a cybersecurity strategy under which only pre-approved or trusted users, entities, or actions are allowed to operate on a system or network. Instead of trying to keep one step ahead of cyber attackers to identify and block malicious code, with a whitelist approach, IT security teams instead identify trustworthy agents,…
Read MoreJun 07, 2024NewsroomCyber Attack / Malware The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of cyber attacks targeting defense forces in the country with a malware called SPECTR as part of an espionage campaign dubbed SickSync. The agency attributed the attacks to a threat actor it tracks under the moniker UAC-0020, which is…
Read MoreRecent Posts
- Fake AI video generators infect Windows, macOS with infostealers
- T-Mobile confirms it was hacked in recent wave of telecom breaches
- GitHub projects targeted with malicious commits to frame researcher
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’