Category: Viral
Oct 24, 2024Ravie LakshmananRansomware / Cybercrime Cybersecurity researchers have discovered an advanced version of the Qilin ransomware sporting increased sophistication and tactics to evade detection. The new variant is being tracked by cybersecurity firm Halcyon under the moniker Qilin.B. “Notably, Qilin.B now supports AES-256-CTR encryption for systems with AESNI capabilities, while still retaining Chacha20 for…
Read MoreA suspected nation-state campaign has been targeting FortiManager customers — likely including MSPs — since at least late June, according to security researchers. The attacks exploiting a critical-severity vulnerability in Fortinet FortiManager are likely targeting MSPs in a nation-state espionage campaign, according to a security researcher. In a post Tuesday, well-known researcher Kevin Beaumont noted…
Read MoreESET researchers have discovered new Rust-based tooling leading to the deployment of Embargo ransomware. Embargo is a relatively new player in the ransomware scene, first observed by ESET in June 2024. The new toolkit consists of a loader and an EDR killer, named MDeployer and MS4Killer respectively by ESET. MS4Killer is particularly noteworthy as it…
Read More‘With Amit [Zavery], we found the dream innovator to captivate the market with a compelling vision for ServiceNow as the AI platform for business transformation,’ says ServiceNow CEO Bill McDermott about hiring its new president, chief product officer and chief operating officer. Google Cloud’s former general manager of cloud operations and business platform, Amit Zavery,…
Read MoreIterate.ai’s Generate application is part of a new SMB App Pack that Intel is bundling with AI PCs for channel partners to sell, and it has partnered with TD Synnex to handle distribution for the application, which the company says is only the beginning of its channel ambitions. An Intel ISV partner said it’s going…
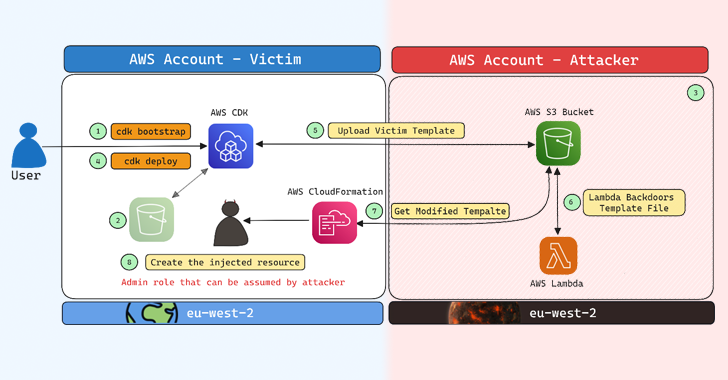
Read MoreCybersecurity researchers have disclosed a security flaw impacting Amazon Web Services (AWS) Cloud Development Kit (CDK) that could have resulted in an account takeover under specific circumstances. “The impact of this issue could, in certain scenarios, allow an attacker to gain administrative access to a target AWS account, resulting in a full account takeover,” Aqua…
Read MoreThe vulnerability—which has been exploited in attacks compromising more than 50 FortiManager devices, according to Mandiant researchers—was disclosed by Fortinet Wednesday. A critical-severity FortiManager vulnerability publicly disclosed by Fortinet this week has been exploited in attacks dating back to late June, according to Mandiant researchers. The attacks exploiting the flaw (tracked at CVE-2024-47575) has compromised…
Read MoreOct 24, 2024Ravie LakshmananVulnerability / Network Security Cisco on Wednesday said it has released updates to address an actively exploited security flaw in its Adaptive Security Appliance (ASA) that could lead to a denial-of-service (DoS) condition. The vulnerability, tracked as CVE-2024-20481 (CVSS score: 5.8), affects the Remote Access VPN (RAVPN) service of Cisco ASA and…
Read MoreSometimes, it turns out that the answers we struggled so hard to find were sitting right in front of us for so long that we somehow overlooked them. When the Department of Homeland Security, through the Cybersecurity and Infrastructure Security Agency (CISA), in coordination with the FBI, issues a cybersecurity warning and prescribes specific action,…
Read MoreThe North Korean threat actor known as Lazarus Group has been attributed to the zero-day exploitation of a now-patched security flaw in Google Chrome to seize control of infected devices. Cybersecurity vendor Kaspersky said it discovered a novel attack chain in May 2024 that targeted the personal computer of an unnamed Russian national with the…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA