Category: Viral
Not long ago, the ability to digitally track someone’s daily movements just by knowing their home address, employer, or place of worship was considered a dangerous power that should remain only within the purview of nation states. But a new lawsuit in a likely constitutional battle over a New Jersey privacy law shows that anyone…
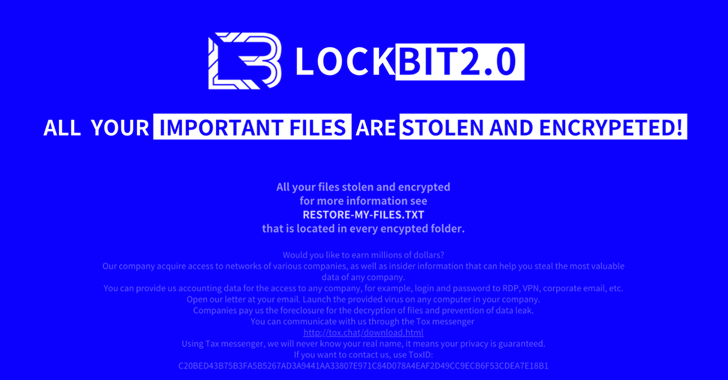
Read MoreThreat actors have been observed abusing Amazon S3 (Simple Storage Service) Transfer Acceleration feature as part of ransomware attacks designed to exfiltrate victim data and upload them to S3 buckets under their control. “Attempts were made to disguise the Golang ransomware as the notorious LockBit ransomware,” Trend Micro researchers Jaromir Horejsi and Nitesh Surana said.…
Read MoreIt may come as a surprise to learn that 34% of security practitioners are in the dark about how many SaaS applications are deployed in their organizations. And it’s no wonder—the recent AppOmni 2024 State of SaaS Security Report reveals that only 15% of organizations centralize SaaS security within their cybersecurity teams. These statistics not…
Read MoreOct 23, 2024Ravie LakshmananArtificial Intelligence / Vulnerability Cybersecurity researchers have shed light on a new adversarial technique that could be used to jailbreak large language models (LLMs) during the course of an interactive conversation by sneaking in an undesirable instruction between benign ones. The approach has been codenamed Deceptive Delight by Palo Alto Networks Unit…
Read More‘Storage is a part of intelligent data infrastructure, which combines unified data storage, intelligent services for data and workload optimization, and solutions that integrate those foundational capabilities with the big ecosystems that make it better for customers,’ says NetApp CEO George Kurian. Storage Company Or Not NetApp, with its leading role in storage hardware and…
Read MoreThe SEC announced penalties of $4 million for Unisys and roughly $1 million apiece for Avaya, Check Point and Mimecast over what the agency said were ‘materially misleading disclosures’ after the series of attacks in 2020 and early 2021. The U.S. Securities and Exchange Commission on Tuesday announced penalties against Unisys, Avaya, Check Point Software…
Read MoreLenovo ISG Leader Says ‘Meet-In-The-Channel’ AI Solutions Made For Partners To Deliver Value
by nlqip
‘We think that the AI market is going to pick up over the next two years in that on-prem segment and channel partners are going to be a very important part of that as we go across those markets,’ says Vlad Rozanovich, senior vice president of infrastructure solutions at Lenovo. Lenovo is leaning on highly…
Read MoreScams Watch out for schemes where fraudsters trick people into sharing verification codes so they can gain access to their phone numbers 21 Oct 2024 • , 5 min. read In our hyper-connected world, technology has transformed the way we communicate, enabling us to connect with anyone, anywhere, at the touch of a button. One…
Read More‘This really marks for many of us the culmination of a four- or five-year journey,’ OpenText SVP Geoff Bibby said during a virtual event Tuesday. OpenText announced a major expansion of its Secure Cloud platform Monday in what executives called a massive investment into generating growth opportunities with its MSP partners. The OpenText Secure Cloud…
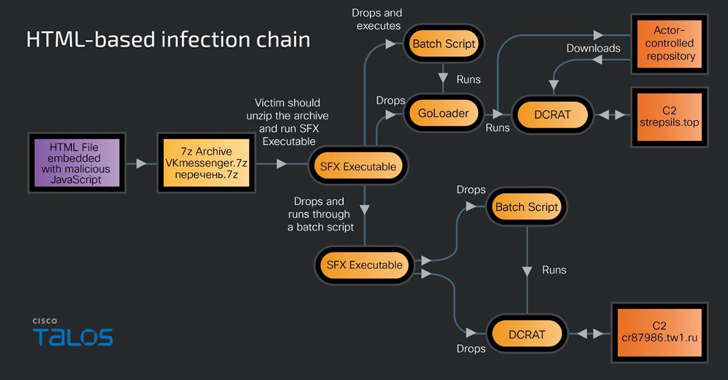
Read MoreRussian-speaking users have become the target of a new phishing campaign that leverages an open-source phishing toolkit called Gophish to deliver DarkCrystal RAT (aka DCRat) and a previously undocumented remote access trojan dubbed PowerRAT. “The campaign involves modular infection chains that are either Maldoc or HTML-based infections and require the victim’s intervention to trigger the…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA