Category: Viral
Did you know that Network Detection and Response (NDR) has become the most effective technology to detect cyber threats? In contrast to SIEM, NDR offers adaptive cybersecurity with reduced false alerts and efficient threat response. Are you aware of Network Detection and Response (NDR) and how it’s become the most effective technology to detect cyber…
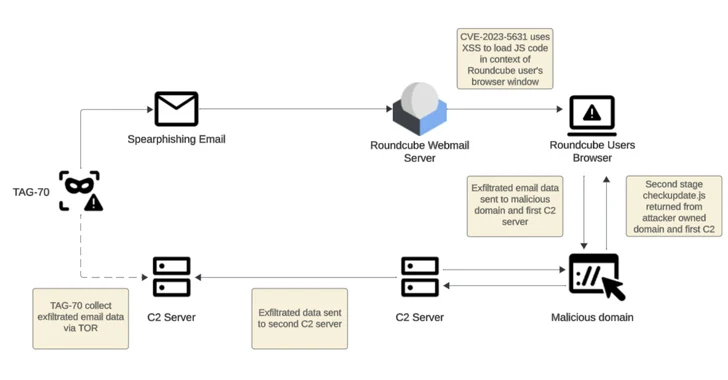
Read MoreFeb 19, 2024NewsroomCyber Espionage / Vulnerability Threat actors operating with interests aligned to Belarus and Russia have been linked to a new cyber espionage campaign that likely exploited cross-site scripting (XSS) vulnerabilities in Roundcube webmail servers to target over 80 organizations. These entities are primarily located in Georgia, Poland, and Ukraine, according to Recorded Future,…
Read MoreVideo Here’s how the results of vulnerability scans factor into decisions on cyber-insurance and how human intelligence comes into play in the assessment of such digital signals 16 Feb 2024 Cyber-insurance has been an increasingly hot topic lately, with the cyber-insurance industry growing of 62 percent last year, which largely appears to be attributable to…
Read MoreFeb 17, 2024NewsroomArtificial Intelligence / Data Protection Google has announced that it’s open-sourcing Magika, an artificial intelligence (AI)-powered tool to identify file types, to help defenders accurately detect binary and textual file types. “Magika outperforms conventional file identification methods providing an overall 30% accuracy boost and up to 95% higher precision on traditionally hard to…
Read MoreVideo Artificial intelligence is on everybody’s lips these days, but there are also many misconceptions about what AI actually is and isn’t. We unpack the basics and examine AI’s broader implications. 15 Feb 2024 Artificial intelligence (AI) is clearly the topic du jour as technologies that fall under the umbrella term of AI become increasingly…
Read MoreWith breaches making the headlines on an almost weekly basis, the cybersecurity challenges we face are becoming visible not only to large enterprises, who have built security capabilities over the years, but also to small to medium businesses and the broader public. While this is creating greater awareness among smaller businesses of the need to…
Read MoreThreat Actor Leverages Compromised Account of Former Employee to Access State Government Organization | CISA
by nlqip
SUMMARY The Cybersecurity and Infrastructure Security Agency (CISA) and the Multi-State Information Sharing & Analysis Center (MS-ISAC) conducted an incident response assessment of a state government organization’s network environment after documents containing host and user information, including metadata, were posted on a dark web brokerage site. Analysis confirmed that an unidentified threat actor compromised network…
Read MoreA reverse engineering of the firmware running on Ivanti Pulse Secure appliances has revealed numerous weaknesses, once again underscoring the challenge of securing software supply chains. Eclypsiusm, which acquired firmware version 9.1.18.2-24467.1 as part of the process, said the base operating system used by the Utah-based software company for the device is CentOS 6.4. “Pulse…
Read MoreThe burgeoning field of digital forensics plays a crucial role in investigating a wide range of cybercrimes and cybersecurity incidents. Indeed, in our technology-centric world, even investigations of ‘traditional’ crimes often include an element of digital evidence that is waiting to be retrieved and analyzed. This art of uncovering, analyzing and interpreting digital evidence has…
Read MoreFeb 14, 2024NewsroomArtificial Intelligence / Cyber Attack Nation-state actors associated with Russia, North Korea, Iran, and China are experimenting with artificial intelligence (AI) and large language models (LLMs) to complement their ongoing cyber attack operations. The findings come from a report published by Microsoft in collaboration with OpenAI, both of which said they disrupted efforts…
Read MoreRecent Posts
- Arm To Seek Retrial In Qualcomm Case After Mixed Verdict
- Jury Sides With Qualcomm Over Arm In Case Related To Snapdragon X PC Chips
- Equinix Makes Dell AI Factory With Nvidia Available Through Partners
- AMD’s EPYC CPU Boss Seeks To Push Into SMB, Midmarket With Partners
- Fortinet Releases Security Updates for FortiManager | CISA