Cybersecurity Snapshot: Study Raises Open Source Security Red Flags, as Cyber Agencies Offer Prevention Tips Against Telecom Spying Attacks
by nlqip
Don’t miss the Linux Foundation’s deep dive into open source software security. Plus, cyber agencies warn about China-backed cyber espionage campaign targeting telecom data. Meanwhile, a study shows the weight of security considerations in generative AI projects. And get the latest on ransomware trends, financial cybercrime and critical infrastructure security. Dive into six things that…
Read MoreDell Technologies now says it offers AI data readiness with Dell Data Lakehouse, the densest GPU-capacity inside liquid-cooled racks and an AI model-buffing Agentic RAG with Nvidia. Dell Technologies says its AI advances in servers offer customers the densest GPU capacity available for Nvidia’s most sophisticated processors running in liquid-cooled cabinets that, all together, push…
Read MoreTry Tenable Web App Scanning Enjoy full access to our latest web application scanning offering designed for modern applications as part of the Tenable One Exposure Management platform. Safely scan your entire online portfolio for vulnerabilities with a high degree of accuracy without heavy manual effort or disruption to critical web applications. Sign up now.…
Read MoreAT&T, Verizon, CrowdStrike and Microsoft are among the companies that experienced major cloud service outages during the last year. A February AT&T outage that received attention by federal regulators. Issues in September for Verizon customers. And a certain cybersecurity vendor’s update that crashed Windows machines worldwide. These are among the biggest cloud service outages the…
Read MoreAs Intel’s board of directors searches for a new permanent leader and pushes for better execution of its strategy after CEO Pat Gelsinger’s abrupt exit on Sunday, the beleaguered chipmaker adds two veteran semiconductor leaders to its board. Intel said it has added two veteran semiconductor executives to its board of directors: former ASML CEO…
Read MoreToday, the Cybersecurity and Infrastructure Security Agency (CISA) released an updated public version of the Continuous Diagnostics and Mitigation (CDM) Data Model Document. Version 5.0.1 aligns with fiscal year 2023 Federal Information Security Modernization Act (FISMA) metrics. The CDM Data Model Document provides a comprehensive description of a common data schema to ensure that prescribed…
Read MoreCISA released two Industrial Control Systems (ICS) advisories on December 5, 2024. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. CISA encourages users and administrators to review newly released ICS advisories for technical details and mitigations. Source link lol
Read MoreASD’s ACSC, CISA, and US and International Partners Release Guidance on Choosing Secure and Verifiable Technologies | CISA
by nlqip
Today, CISA—in partnership with the Australian Signals Directorate Australian Cyber Security Centre (ASD ACSC), and other international partners—released updates to a Secure by Design Alert, Choosing Secure and Verifiable Technologies. Partners that provided recommendations in this alert include: The Canadian Centre for Cyber Security (CCCS). United Kingdom’s National Cyber Security Centre (NCSC-UK). New Zealand’s National…
Read More‘Not only did we grow our AWS business 184 percent (in 2024), our pipeline is forecasting over 300 percent growth in 2025,’ said DoiT International’s Tracie Stamm. Amazon Web Services partners are witnessing massive sales growth in 2024 thanks to the company’s ever-expanding generative AI product portfolio and AI channel investments. Global powerhouse DoiT International…
Read MoreHow NIST is working with Tenable and other private sector stakeholders to better enable zero trust implementation. Trust no one. Verify everything. All the time. When it comes to cybersecurity and protecting your expanding attack surface, that’s more than a catchphrase. It’s the way you must approach access to your network, systems and assets. Ultimately,…
Read MoreRecent Posts
- Google Cloud Hires Tech Superstar Francis DeSouza As New COO
- AWS Invests $11B In Georgia To ‘Support The Future Of AI’ Via Data Centers
- Google’s Willow Quantum Chip and Its Potential Threat to…
- Citrix Parent Cloud Software Group Confirms Layoffs
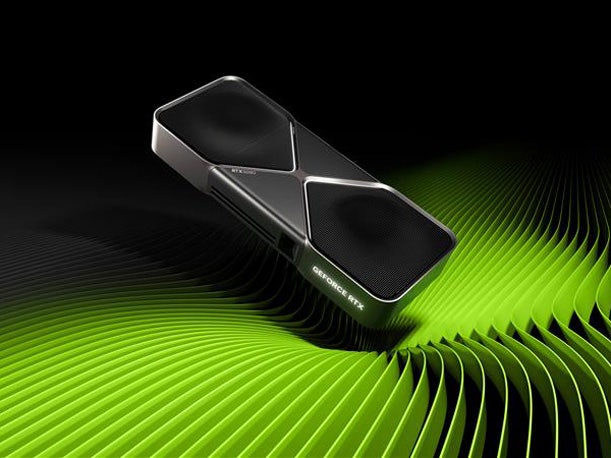
- Nvidia Seeks To Turbocharge AI PC Development With GeForce RTX 50 GPUs