Other levels of compensation, without RCE, include demonstrating a controlled write or a memory corruption. The baseline for bugs that do not demonstrate such “higher-quality reports” range from US$7,000 to US$25,000. Last year, the total payouts in Google’s bug hunter program were US$10 million dollars, distributed among 632 people from 68 countries. Just over a…
Read MoreAug 29, 2024Ravie LakshmananBrowser Security / Vulnerability Cybersecurity researchers have flagged multiple in-the-wild exploit campaigns that leveraged now-patched flaws in Apple Safari and Google Chrome browsers to infect mobile users with information-stealing malware. “These campaigns delivered n-day exploits for which patches were available, but would still be effective against unpatched devices,” Google Threat Analysis Group…
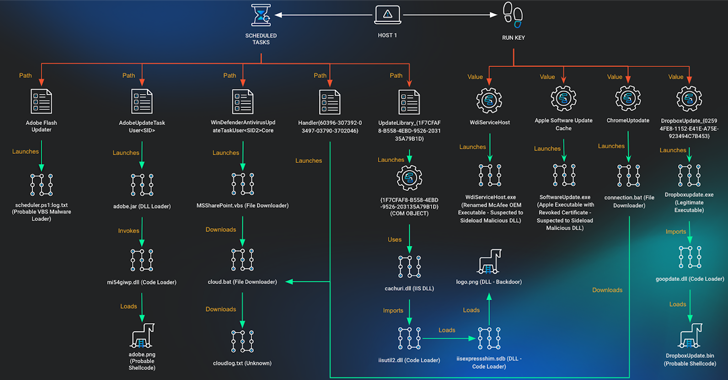
Read MoreAug 29, 2024Ravie LakshmananCyber Espionage / Malware A non-profit supporting Vietnamese human rights has been the target of a multi-year campaign designed to deliver a variety of malware on compromised hosts. Cybersecurity company Huntress attributed the activity to a threat cluster known as APT32, a Vietnamese-aligned hacking crew that’s also known as APT-C-00, Canvas Cyclone…
Read MoreAdm. Grace Hopper’s 1982 NSA Lecture Has Been Published The “long lost lecture” by Adm. Grace Hopper has been published by the NSA. (Note that there are two parts.) It’s a wonderful talk: funny, engaging, wise, prescient. Remember that talk was given in 1982, less than a year before the ARPANET switched to TCP/IP and…
Read MoreImage: Midjourney The Corona Mirai-based malware botnet is spreading through a 5-year-old remote code execution (RCE) zero-day in AVTECH IP cameras, which have been discontinued for years and will not receive a patch. The flaw, discovered by Akamai’s Aline Eliovich, is tracked as CVE-2024-7029 and is a high-severity (CVSS v4 score: 8.7) issue in the…
Read MoreImportantly, with its development based in Dubai and St Petersburg, Telegram isn’t an American company. For prosecutors, both inside and outside of the US, that has become an issue. Should the authorities want to grab metadata such as the IP address of a specific user on a social media, messaging or email platform, companies registered…
Read MoreWho doesn’t fancy earning US $2.5 million? That’s the reward that’s on offer from the US Department and State and Secret Service for information leading to the arrest and/or conviction of a Belarusian man who allegedly was a key figure behind the development and distribution of the notorious Angler Exploit Kit. 38-year-old Vladimir Kadariya is…
Read MoreCISA has added one new vulnerability to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2024-7965 Google Chromium V8 Inappropriate Implementation Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited…
Read MoreCISA released three Industrial Control Systems (ICS) advisories on August 29, 2024. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. CISA encourages users and administrators to review the newly released ICS advisories for technical details and mitigations. Source link lol
Read MoreThe goal of the partnership is to ensure Citrix Service Provider partners ‘have the level of coverage, service, technical support, so on and so forth that they need to be effective in their business and maintain flexibility in the model in which they want to consume,’ says Ethan Fitzsimons, Citrix’s channel chief. Citrix, a business…
Read MoreRecent Posts
- Fake AI video generators infect Windows, macOS with infostealers
- T-Mobile confirms it was hacked in recent wave of telecom breaches
- GitHub projects targeted with malicious commits to frame researcher
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’