Tenable®, the exposure management company, today announced that it has named Shai Morag to the role of chief product officer. Morag will focus on delivering increased momentum and scale across Tenable’s entire portfolio, driving the company’s next era of growth by building security products for a cloud-first world. Morag joined Tenable in 2023 through the…
Read MoreTenable Research discovered multiple privilege-escalation issues in the Azure Health Bot Service via a server-side request forgery (SSRF), which allowed researchers access to cross-tenant resources. The Azure Health Bot Service is a cloud platform that allows healthcare professionals to deploy AI-powered virtual health assistants. Tenable Research discovered critical vulnerabilities that allowed access to cross-tenant resources…
Read MoreNascent yet prominent group With activities traceable to August 2023, the group quickly grew fame as a formidable threat agency and made a dark web entry in February 2024, advertising leaked data on recently disrupted BreachForums and other leak sites. The group, the FBI pointed out, had claimed many victims internationally which included 43 companies…
Read MoreAug 13, 2024The Hacker NewsCyber Defense / Compliance Traditionally, the focus has been on defending against digital threats such as malware, ransomware, and phishing attacks by detecting them and responding. However, as cyber threats become more sophisticated. There is a growing recognition of the importance of measures that stop new attacks before they are recognized.…
Read MoreOn the Voynich Manuscript Really interesting article on the ancient-manuscript scholars who are applying their techniques to the Voynich Manuscript. No one has been able to understand the writing yet, but there are some new understandings: Davis presented her findings at the medieval-studies conference and published them in 2020 in the journal Manuscript Studies. She…
Read MoreThe U.S. Federal Bureau of Investigation (FBI) on Monday announced the disruption of online infrastructure associated with a nascent ransomware group called Dispossessor (aka Radar). The effort saw the dismantling of three U.S. servers, three United Kingdom servers, 18 German servers, eight U.S.-based criminal domains, and one German-based criminal domain. Dispossessor is said to be…
Read MoreMoreover, under a 2023 AI safety and security White House executive order, NIST released last week three final guidance documents and a draft guidance document from the newly created US AI Safety Institute, all intended to help mitigate AI risks. NIST also re-released a test platform called Dioptra for assessing AI’s “trustworthy” characteristics, namely AI…
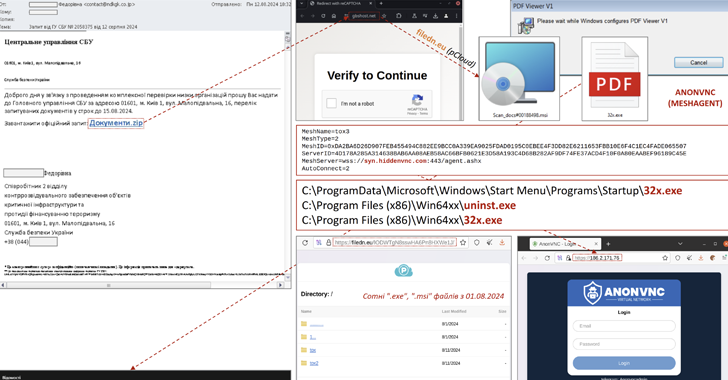
Read MoreAug 13, 2024Ravie LakshmananThreat Intelligence / Malware The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of a new phishing campaign that masquerades as the Security Service of Ukraine to distribute malware capable of remote desktop access. The agency is tracking the activity under the name UAC-0198. More than 100 computers are estimated to…
Read MoreEuropean privacy advocate NOYB (None of Your Business) has filed nine GDPR complaints about X using the personal data from over 60 million users in Europe to train “Grok,” the social media company’s large language model. According to NOYB, X did not inform its users that their data was being used to train AI and did…
Read MoreThe FBI announced on Monday that it seized the servers and websites of the Radar/Dispossessor ransomware operation following a joint international investigation. The joint operation was carried out in collaboration with the U.K.’s National Crime Agency, the Bamberg Public Prosecutor’s Office, and the Bavarian State Criminal Police Office (BLKA). Law enforcement seized three U.S. servers,…
Read MoreRecent Posts
- Fake AI video generators infect Windows, macOS with infostealers
- T-Mobile confirms it was hacked in recent wave of telecom breaches
- GitHub projects targeted with malicious commits to frame researcher
- NSO Group used another WhatsApp zero-day after being sued, court docs say
- Ingram Micro’s Sahoo: ‘Don’t React To AI.’ Act On AI’